An IT Security Policy identifies the rules and procedures for all individuals accessing and using an organization’s IT assets and resources.
Information Technology (IT) Security Policy identifies the rules and procedures for all individuals accessing and using an organization’s IT assets and resources. Effective IT Security Policy is a model of the organization’s culture, in which rules and procedures are driven from its employees’ approach to their information and work. Thus, an effective IT security policy is a unique document for each organization, cultivated from its people’s perspectives on risk tolerance, how they see and value their information and the resulting availability that they maintain of that information. For this reason, many companies will find a boilerplate IT security policy inappropriate due to its lack of consideration for how the organization’s people actually use and share information among themselves and to the public.
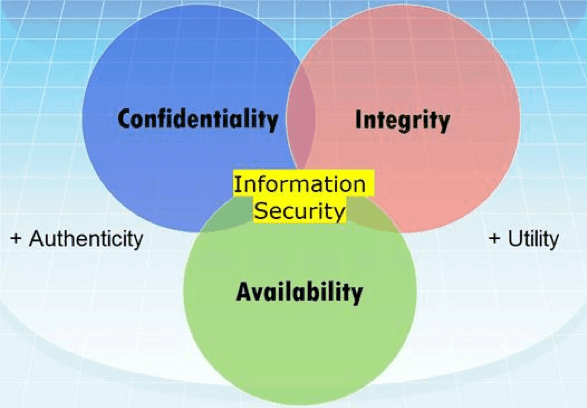
The objectives of an IT security policy is the preservation of confidentiality, integrity, and availability of systems and information used by an organization’s members. These three principles compose the CIA triad:
- Confidentiality involves the protection of assets from unauthorized entities
- Integrity ensures the modification of assets is handled in a specified and authorized manner
- Availability is a state of the system in which authorized users have continuous access to said assets
The Importance of an Information Security Policy
- Creating an effective security policy and taking steps to ensure compliance is a critical step to prevent and mitigate security breaches. To make your security policy truly effective, update it in response to changes in your company, new threats, conclusions drawn from previous breaches, and other changes to your security posture.
- Make your information security policy practical and enforceable. It should have an exception system in place to accommodate requirements and urgencies that arise from different parts of the organization.
8 Elements of an Information Security Policy
A security policy can be as broad as you want it to be from everything related to IT security and the security of related physical assets, but enforceable in its full scope. The following list offers some important considerations when developing an information security policy.
1. Purpose
First state the purpose of the policy which may be to:
- Create an overall approach to information security.
- Detect and preempt information security breaches such as misuse of networks, data, applications, and computer systems.
- Maintain the reputation of the organization, and uphold ethical and legal responsibilities.
- Respect customer rights, including how to react to inquiries and complaints about non-compliance.
2. Audience
Define the audience to whom the information security policy applies. You may also specify which audiences are out of the scope of the policy (for example, staff in another business unit that manages security separately may not be in the scope of the policy).
3. Information security objectives
Guide your management team to agree on well-defined objectives for strategy and security. Information security focuses on three main objectives:
- Confidentiality—only individuals with authorization canshould access data and information assets
- Integrity—data should be intact, accurate and complete, and IT systems must be kept operational
- Availability—users should be able to access information or systems when needed
4. Authority and access control policy
- Hierarchical pattern—a senior manager may have the authority to decide what data can be shared and with whom. The security policy may have different terms for a senior manager vs. a junior employee. The policy should outline the level of authority over data and IT systems for each organizational role.
- Network security policy—users are only able to access company networks and servers via unique logins that demand authentication, including passwords, biometrics, ID cards, or tokens. You should monitor all systems and record all login attempts.
5. Data classification
The policy should classify data, which may include “top secret”, “secret”, “confidential” and “public”. Your objective in classifying data is:
- To ensure that sensitive data cannot be accessed by individuals with lower clearance levels.
- To protect highly important data, and avoid needless security measures for unimportant data.
6. Data support and operations
- Data protection regulations—systems that store personal data, or other sensitive data, must be protected according to organizational standards, best practices, industry compliance standards, relevant regulations. Most security standards require, at a minimum, encryption, a firewall, and anti-malware protection.
- Data backup—encrypt data backup according to industry best practices. Securely store backup media, or move back up to secure cloud storage.
- Movement of data—only transfer data via secure protocols. Encrypt any information copied to portable devices or transmitted across a public network.
7. Security awareness and behavior
Share IT security policies with your staff. Conduct training sessions to inform employees of your security procedures and mechanisms, including data protection measures, access protection measures, and sensitive data classification.
- Social engineering—place a special emphasis on the dangers of social engineering attacks (such as phishing emails). Make employees responsible for noticing, preventing and reporting such attacks.
- Clean desk policy—secure laptops with a cable lock. Shred documents that are no longer needed. Keep printer areas clean so documents do not fall into the wrong hands.
- Acceptable Internet usage policy—define how the Internet should be restricted. Do you allow YouTube, social media websites, etc.? Block unwanted websites using a proxy.
8. Responsibilities, rights, and duties of personnel
- Appoint staff to carry out user access reviews, education, change management, incident management, implementation, and periodic updates of the security policy. Responsibilities should be clearly defined as part of the security policy.
- In establishing the foundation for a security program, companies will usually first designate an employee to be responsible for cybersecurity. It will be this employee who will begin the process of creating a plan to manage their company’s risk through security technologies, auditable work processes, and documented policies and procedures.
A mature security program will require the following policies and procedures:
1. Acceptable Use Policy (AUP)
An AUP stipulates the constraints and practices that an employee using organizational IT assets must agree to access to the corporate network or the internet. It isa standard onboarding policy for new employees. They are given an AUP to read and sign before being granted a network ID. It is recommended that and organization’s IT, security, legal and HR departments discuss what is included in this policy. An example that is available for fair use can be found at ACTE.
2. Access Control Policy (ACP)
The ACP outlines the access available to employees in regard to an organization’s data and information systems. Some topics that are typically included in the policy are access control standards such as NIST’s Access Control and Implementation Guides. Other items covered in this policy are standards for user access, network access controls, operating system software controls, the complexity of corporate passwords. Additional supplementary items often outlined include methods for monitoring how corporate systems are accessed and used; how unattended workstations should be secured; and how access is removed when an employee leaves the organization. An excellent example of this policy is available at IAPP.
3. Change Management Policy
A change management policy refers to a formal process for making changes to IT, software development, services/operations. The goal of a change management program is to increase the awareness and understanding of proposed changes across an organization and to ensure that all changes are conducted methodically to minimize any adverse impact on services and customers. A good example of an IT change management policy available for fair use is at ACTE.
4. Information Security Policy
An organization’s information security policies are typically high-level policies that can cover a large number of security controls. The primary information security policy is issued by the company to ensure that all employees who use information technology assets within the breadth of the organization, or its networks, comply with its stated rules and guidelines. I have seen organizations ask employees to sign this document to acknowledge that they have read it (which is generally done with the signing of the AUP policy). This policy is designed for employees to recognize that there are rules that they will be held accountable to about the sensitivity of the corporate information and IT assets. The State of Illinois provides an excellent example of a cybersecurity policy that is available for download.
5. Incident Response (IR) Policy
The incident response policy is an organized approach to how the company will manage an incident and remediate the impact of operations. It’s the one policy CISOs hope to never have to use. However, the goal of this policy is to describe the process of handling an incident concerning limiting the damage to business operations, customers, reducing recovery time and costs. Carnegie Mellon University provides an example of a high-level IR plan and ACTE offers a plan specific to data breaches.
6. Remote Access Policy
The remote access policy is a document that outlines and defines acceptable methods of remotely connecting to an organization’s internal networks. I have also seen this policy include addendums with rules for the use of BYOD assets. This policy is a requirement for organizations that have dispersed networks with the ability to extend into insecure network locations, such as the local coffee house or unmanaged home networks. An example of a remote access policy is available at ACTE.
7. Email/Communication Policy
A company’s email policy is a document that is used to formally outline how employees can use the business’ chosen electronic communication medium. I have seen this policy cover email, blogs, social media, chat technologies. The primary goal of this policy is to provide guidelines to employees on what is considered the acceptable and unacceptable use of any corporate communication technology. An example of an email policy is available at ACTE
8. Disaster Recovery Policy
An organization’s disaster recovery plan will generally include both cybersecurity and IT teams’ input and will be developed as part of the larger business continuity plan. The CISO and teams will manage an incident through the incident response policy. If the event has a significant business impact, the Business Continuity Plan will be activated. An example of a disaster recovery policy is available at ACTE.
9. Business Continuity Plan (BCP)
The BCP will coordinate efforts across the organization and will use the disaster recovery plan to restore hardware, applications,and data deemed essential for business continuity. BCP’s are unique to each business because they describe how the organization will operate in an emergency. Two examples of BCP’s that organizations can use to create their own are available at FEMA and Kapnick.
CONCLUSION:
- The above policies and documents are just some of the basic guidelines I use to build successful security programs. There are many more that a CISO will develop as their organization matures and the security program expands.
- their are two resources I would recommend to people who have been selected to create their company’s first security policies. The first, as highlighted above, is the ACTE Information Security Policy Templates website with numerous policies available for download Another source Always remember to evangelize you’re new policies and guidelines with employees. Employees must be aware and up-to-date on any IT and cybersecurity procedure changes.