General
-
Understanding Python in DevOps Automation and Efficiency
Introduction Importance of Python in DevOps Automation with Python Scripts Using Python for Configuration Management Integrating Python with CI/CD Tools Monitoring and Logging with Python Scripting for Cloud Services (AWS, Azure) Debugging and Best Practices Infrastructure as Code with Python Advanced Use Cases of Python in...
-
Azure Front Door: Secure, Scalable Web Traffic Management
Introduction to Azure Front Door What Makes Azure Front Door Stand Out? Key Features of Azure Front Door How Azure Front Door Works Benefits of Using Azure Front Door Azure Front Door vs. Azure Application Gateway: A Comparison Use Cases for Azure Front Door How to Set Up and Configure Azure Front Door Conclusion Ready to Pursue Your...
-
Getting Started with AWS OpsWorks: A Comprehensive Guide
Introduction to AWS OpsWorks What is AWS OpsWorks? Key Features of AWS OpsWorks OpsWorks Stacks vs. OpsWorks for Chef Automate vs. OpsWorks for Puppet Enterprise Understanding the AWS OpsWorks Architecture How to Set Up and Configure AWS OpsWorks Everyday Use Cases for AWS OpsWorks Benefits of Using AWS OpsWorks Conclusion Are You...
-
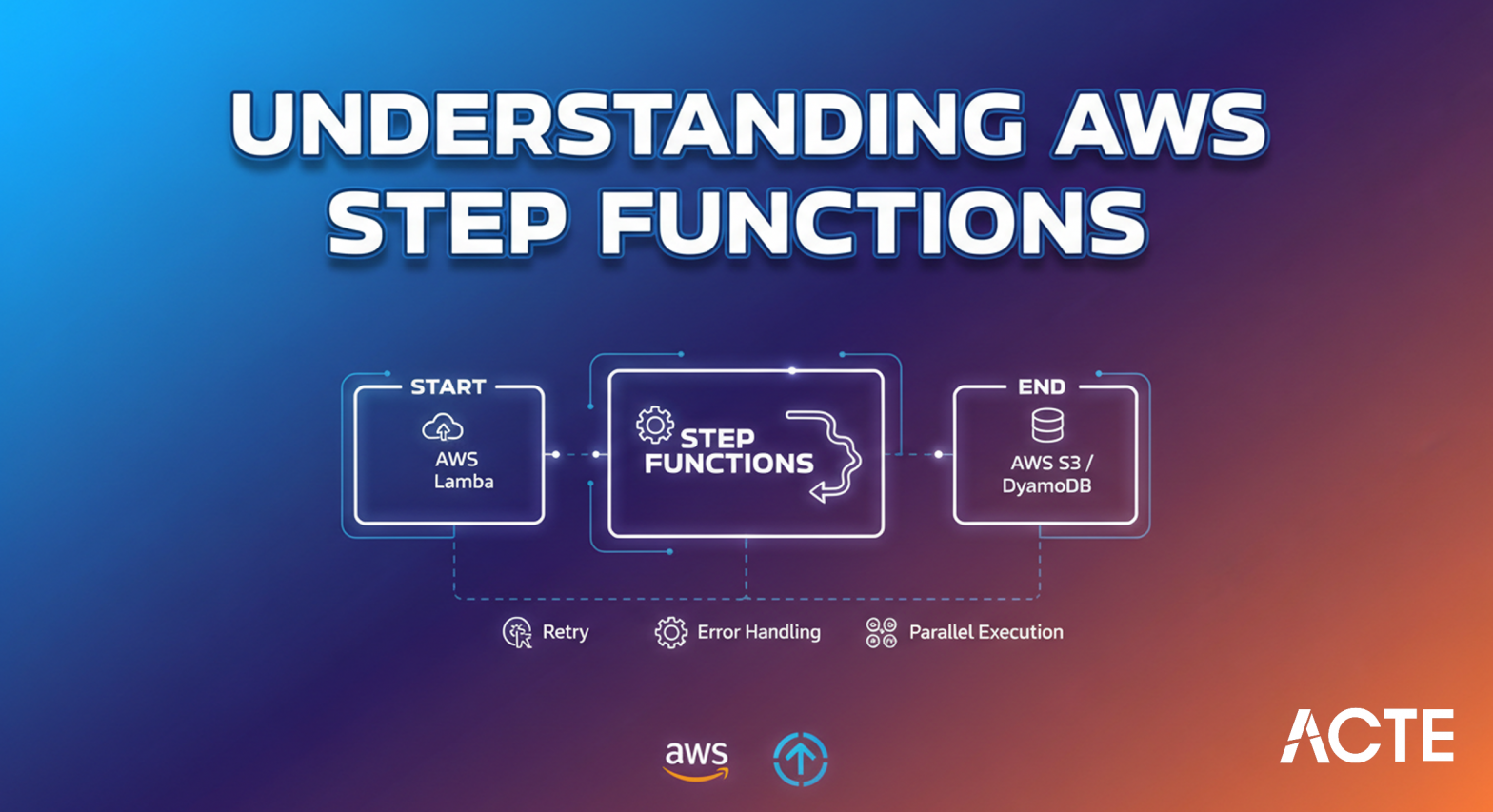
Understanding AWS Step Functions: Features and Benefits
Introduction to AWS Step Functions Key Features of AWS Step Functions Benefits of Using AWS Step Functions How AWS Step Functions Work Setting Up AWS Step Functions Integrating AWS Step Functions with Other AWS Services AWS Step Functions vs. Traditional Workflow Management Use Cases of AWS Step Functions Security and Compliance in AWS Step...
-
Exploring AWS CodeCommit: Secure and Scalable Source Control
Introduction to AWS CodeCommit Key Features of AWS CodeCommit Benefits of Using AWS CodeCommit How AWS CodeCommit Works Setting Up AWS CodeCommit Integrating AWS CodeCommit with Other Tools AWS CodeCommit vs. Other Version Control Systems Use Cases of AWS CodeCommit Security and Compliance in AWS CodeCommit Pricing and Cost Management Common...
-
Mastering AWS S3 CLI: Efficient Cloud Storage Management
Introduction to AWS S3 CLI Setting Up AWS CLI for S3 Operations Managing Buckets with AWS S3 CLI Basic AWS S3 CLI Commands Working with Objects in S3 Using CLI S3 Bucket Policies and Permissions via CLI Troubleshooting S3 CLI Commands Advanced S3 CLI Features Security Best Practices for S3 CLI Usage Conclusion Introduction to AWS S3...
-
Exploring AWS ElastiCache: Boosting Application Performance
Introduction: What is AWS ElastiCache? Key Features of AWS ElastiCache How AWS ElastiCache Works: The Technical Overview Benefits of Using AWS ElastiCache for Your Applications Supported Caching Engines: Redis and Memcached Setting Up AWS ElastiCache: A Simple Guide Real-World Use Cases of AWS ElastiCache Conclusion Introduction:...
-
Unlocking Edge Computing with AWS Greengrass: A Guide
What is AWS Greengrass? AWS Greengrass Core and Devices Setting Up AWS Greengrass Greengrass Use Cases Deploying Lambda Functions to Greengrass Security Features of AWS Greengrass Best Practices for AWS Greengrass Conclusion What is AWS Greengrass? AWS Greengrass is an IoT (Internet of Things) service provided by Amazon Web Services (AWS)...
-
Understanding AWS NAT Gateway: Benefits and Key Use Cases
Introduction What is an AWS NAT Gateway? NAT Gateway vs NAT Instance Setting Up a NAT Gateway in AWS Monitoring AWS NAT Gateway Scaling NAT Gateway in AWS Security Considerations for NAT Gateway Troubleshooting NAT Gateway Issues Conclusion Introduction In modern cloud architectures, the need for secure and reliable internet...
-
Creating Scalable and Secure Microservices on AWS
Introduction to Microservices on AWS AWS Services for Microservices Architecture Building Microservices with AWS Lambda Containerization for Microservices in AWS Scaling Microservices in AWS Monitoring Microservices with AWS Security Considerations for Microservices on AWS Conclusion Introduction to Microservices on AWS Microservices...
- Top Wipro Interview Questions for IT Freshers
- Wipro Java OOP Interview Questions and Answers For Freshers
- How to Crack Wipro Interview from Rural Tamilnadu Background
- How to Crack Wipro Interview: Complete Guide
- 90+ Microsoft DSA Questions and Answers For freshers
- Most Asked Java Interview Questions in Google for Freshers
- DSA Interview Questions For Freshers in Google
- How to Crack Google Technical Interview as a Fresher
- Frequntly asked Data Science Interview Questions in Google For Freshers
- Infosys Virtual Interview Questions and Answers in India
Interview Questions and Answers
- Data Science Masters Program Training Course
- Python Master Program Training Course
- Software Testing Master Program Training course
- Data Analyst Masters Program Training Course
- Full Stack Developer Masters Program Training Course
- Digital Marketing Masters Program Training Course
- Java Full Stack Developer Master Training
- Cloud Computing Master Program Training Course
 LMS
LMS