
The demand for software developer roles at :contentReference[oaicite:0]{index=0} is rapidly increasing, especially in tech-driven cities like :contentReference[oaicite:1]{index=1}. As a global leader in cloud computing, e-commerce, and scalable software solutions, Amazon looks for candidates with strong expertise in data structures, algorithms, system design, and coding efficiency. Many aspiring developers in Chennai are actively preparing to secure positions at Amazon due to its competitive salary packages, innovative work culture, and long-term career growth opportunities. To support your preparation, we have compiled a set of Amazon Software Developer Interview Questions in Chennai, helping you understand the interview pattern and succeed with confidence. Let’s get started!
1. What is Software Development?
Ans:
Software development is the structured process of designing, building, testing, deploying, and maintaining software applications. It includes understanding requirements, writing efficient code, fixing defects, and improving system performance continuously. Organizations depend on software development to create websites, mobile apps, enterprise tools, and cloud platforms. Strong software development skills require logical thinking, problem-solving ability, and technical consistency over time. This topic is commonly asked in fresher developer interviews.
2. How to prepare for Software Developer interviews?
Ans:
- Building strong knowledge in programming languages, data structures, algorithms, and object-oriented concepts creates a solid technical base for coding interviews. These areas form the foundation of most developer hiring processes. Strong fundamentals improve confidence greatly.
- Practicing coding problems regularly on arrays, strings, trees, graphs, and dynamic programming improves speed and problem-solving confidence significantly. Repeated practice builds pattern recognition and accuracy. Consistency gives better results.
- Understanding operating systems, databases, networking, and system design adds broader technical readiness for interviews effectively. These subjects help answer theory and practical questions clearly. Wider knowledge creates stronger profiles.
- Mock interviews and communication practice help explain solutions clearly during technical discussions. Good communication improves interviewer confidence in candidate ability. Clear explanation matters greatly.
3. What is Object Oriented Programming?
Ans:
Object Oriented Programming is a programming paradigm based on objects containing data and behavior together. It uses concepts such as classes, inheritance, polymorphism, abstraction, and encapsulation widely. This approach improves code reusability, maintainability, and modular software design significantly. Languages such as Java, C++, Python, and C# support object oriented programming models. OOP concepts are highly important for developer interviews.
4. How to explain OOP pillars clearly?
Ans:
- Encapsulation means combining data and methods together while restricting unnecessary external direct access effectively. It protects internal values from unsafe modification. This improves maintainability strongly.
- Inheritance allows one class to reuse features of another class, reducing repeated coding effort significantly. Shared behavior can be extended into child classes easily. This saves development time.
- Polymorphism enables one interface to support different implementations based on runtime behavior clearly. The same method call can act differently for separate objects. Flexibility increases greatly.
- Abstraction hides internal complexity and exposes only essential functionality to users naturally. Users interact with simple interfaces instead of deep internal logic. This creates cleaner systems.
5. What is a Class in programming?
Ans:
A class is a blueprint used to create objects with common properties and methods. It defines structure and expected behavior before actual instances are created. For example, an Employee class may contain name, id, and salary attributes. Methods inside the class perform operations related to those attributes efficiently. Classes are fundamental in object oriented development.
6. How to prepare class and object concepts?
Ans:
- Learning that a class is a template while an object is a real instance creates immediate clarity strongly. This distinction is one of the first OOP basics. Clear fundamentals help interviews.
- Practicing examples like Car class and specific car objects improves conceptual understanding significantly. Real-world examples make theory easier to remember. Examples build confidence.
- Understanding constructors, attributes, and methods adds useful technical depth effectively. These components are regularly discussed in interviews. Technical clarity matters.
- Writing simple code samples strengthens interview confidence naturally. Practical coding reinforces theory better than memorization alone. Practice gives better recall.
7. What is an Object in programming?
Ans:
An object is a runtime instance created from a class definition in object oriented programming. It contains actual values for properties and can execute class methods. Multiple objects can be created from the same class blueprint independently. Objects help represent real-world entities in software applications clearly. This topic is common in developer interviews.
8. Write a program for encapsulation using class.
Ans:
This example shows encapsulation using private data and public methods.
- #include <iostream>
- using namespace std;
- class Employee {
- private:
- int salary;
- public:
- void setSalary(int s){ salary=s; }
- int getSalary(){ return salary; }
- };
- int main() {
- Employee e;
- e.setSalary(25000);
- cout << e.getSalary();
- return 0;
- }
In this example, private data is accessed through public methods.
9. What is inheritance in programming?
Ans:
Inheritance is a feature where one class acquires properties and behavior of another class. The parent class provides reusable members for child classes automatically. This reduces duplicated code and supports hierarchical software design patterns. Inheritance is widely used in enterprise systems with shared behaviors. It is an important OOP interview concept.
10. How to explain polymorphism simply?
Ans:
- Polymorphism means one method name can perform different actions in different classes clearly. The same interface behaves uniquely for each object. This increases flexibility.
- Method overriding is runtime polymorphism commonly used in inheritance hierarchies significantly. Child classes redefine inherited behavior when needed. This is widely used.
- Method overloading is compile-time polymorphism using different parameter lists effectively. Same method names with varied inputs improve readability. It simplifies coding.
- Polymorphism improves flexibility and reusable software design strongly. It supports scalable and maintainable enterprise applications. This is a major advantage.
11. What is abstraction in programming?
Ans:
Abstraction means hiding internal implementation complexity while exposing only necessary features externally. Users interact with simple interfaces without knowing internal processing details. Examples include ATM systems and vehicle controls used daily. Abstract classes and interfaces commonly support abstraction in many languages. Abstraction improves modularity and clean architecture significantly.
12. How to prepare abstraction interview answers?
Ans:
- Explaining feature hiding with real-world examples creates stronger conceptual clarity quickly. ATM and remote control examples are easy to understand. Practical examples improve answers.
- Mentioning interfaces and abstract classes adds technical relevance significantly. These are common coding and theory interview topics. Technical depth is useful.
- Comparing abstraction with encapsulation removes common beginner confusion effectively. Many candidates mix both concepts during interviews. Clear distinction creates impact.
- Practicing concise examples improves communication naturally. Short clear explanations are easier for interviewers to follow. Clarity matters greatly.
13. What is Data Structure?
Ans:
A data structure is a method of organizing data for efficient access and modification. Examples include arrays, linked lists, stacks, queues, trees, and graphs widely used. Correct data structure choice improves performance, memory use, and scalability significantly. Software developers rely heavily on data structures for optimized solutions. This topic is central to Amazon interviews.
14. What is the difference between Array and Linked List?
Ans:
| Criteria | Array | Linked List |
|---|---|---|
| Memory | Stored in contiguous memory. | Stored in separate linked nodes. |
| Access | Fast random access by index. | Sequential traversal required. |
| Insertion | Costly in middle positions. | Easier after known node. |
| Size | Usually fixed or predefined. | Dynamic size growth possible. |
15. What is an Array?
Ans:
An array is a collection of elements stored in contiguous memory locations. Elements are accessed using indexes, making retrieval operations fast and efficient. Arrays are widely used for storing lists of numbers, strings, and objects. Insertion in middle positions may require shifting existing elements. Arrays are common coding interview topics.
16. How to solve array interview problems better?
Ans:
- Practicing traversal, prefix sums, sliding window, and two-pointer methods improves speed significantly. These patterns solve many array interview questions efficiently. Pattern mastery helps greatly.
- Understanding indexing and boundary conditions reduces common coding mistakes effectively. Off-by-one errors are frequent in arrays. Careful boundaries improve accuracy.
- Learning sorting-based approaches adds alternate problem-solving strategies naturally. Some hard problems become easier after sorting first. Multiple methods are valuable.
- Writing optimized code with clear logic helps technical rounds strongly. Readable code creates stronger interviewer impressions. Clean solutions matter.
17. What is Linked List?
Ans:
A linked list is a linear data structure made of connected nodes. Each node stores data and a reference to the next node. It allows dynamic memory usage and efficient insertions in many cases. Random access is slower compared with arrays because traversal is needed. Linked lists are frequent interview topics.
18. How to prepare linked list concepts?
Ans:
- Learning node structure with data and pointer references creates clarity immediately. Visualizing nodes makes concepts easier to understand. Basics are important.
- Practicing reversal, cycle detection, and middle node problems improves readiness significantly. These are classic linked list interview questions. Practice builds speed.
- Comparing linked lists with arrays builds stronger understanding effectively. Each structure has unique strengths and limits. Comparison improves judgment.
- Drawing diagrams helps visualize operations naturally. Pointer movement becomes simpler through visuals. Diagrams improve memory.
19. What is Stack data structure?
Ans:
A stack is a linear structure following Last In First Out order. Insertion and deletion happen only from the top position. Common applications include function calls, undo systems, and expression evaluation. Push and pop are the primary operations in stacks. Stacks are important coding interview concepts.
20. How to prepare stack problems efficiently?
Ans:
- Learning LIFO behavior with plate stack examples creates intuitive clarity strongly. Real examples make stack order easy to remember. Concepts become simple.
- Practicing balanced parentheses and next greater element problems improves readiness significantly. These are highly common stack interview problems. Practice helps success.
- Understanding implementation using arrays or linked lists adds technical depth effectively. Multiple implementations show stronger knowledge. This improves confidence.
- Revising time complexity builds confidence naturally. Efficient operations are important in interviews. Complexity awareness matters.
21. What is Queue data structure?
Ans:
A queue is a linear structure following First In First Out processing order. Insertion occurs at rear while deletion happens from front positions. Queues are used in scheduling, buffering, and request handling systems widely. Variants include circular queue, deque, and priority queue forms. Queues are common developer interview topics.
22. How to explain queue applications clearly?
Ans:
- Printer task scheduling uses queue order to process requests sequentially and fairly. Earlier jobs are handled first logically. This reflects FIFO behavior.
- Web servers use queues for handling incoming requests during traffic spikes effectively. Queues help manage overload smoothly. Real systems depend on this.
- Breadth-first search in graphs commonly depends on queue operations significantly. Level-by-level traversal is naturally suited for queues. This is a classic use case.
- Operating systems use queues in task scheduling naturally. Processes are often arranged in waiting lines. Queue logic is practical.
23. What is Time Complexity?
Ans:
Time complexity measures how runtime grows as input size increases gradually. It helps compare algorithm efficiency independent of hardware differences. Common notations include O(1), O(log n), O(n), and O(n²). Efficient algorithms are crucial for large-scale systems and interviews. Time complexity is heavily asked at Amazon.
24. How to prepare complexity analysis strongly?
Ans:
- Learning loop counting and nested iteration analysis creates strong understanding quickly. Many complexity questions start from loops. Basics are essential.
- Practicing recursion complexity improves advanced problem-solving readiness significantly. Recursive calls often confuse beginners. Practice removes confusion.
- Comparing multiple solutions based on complexity adds maturity effectively. Better solutions should justify efficiency clearly. Analysis creates stronger answers.
- Explaining tradeoffs clearly helps interview discussions naturally. Sometimes memory is traded for speed. Balanced thinking matters greatly.
25. What are first stage tips for Amazon developer interviews?
Ans:
Strong first stage preparation should focus on coding basics and core computer science concepts. Candidates should practice arrays, strings, linked lists, stacks, and complexity analysis thoroughly. Clear communication while solving problems often creates stronger impressions significantly. Regular revision improves speed, confidence, and consistency during assessments effectively. Disciplined preparation creates the best foundation for success.
26. What is Space Complexity?
Ans:
Space complexity measures the amount of memory required by an algorithm as input size increases gradually. It includes auxiliary memory used during execution apart from input storage itself. Efficient memory usage becomes highly important in large scale systems and embedded environments. Some algorithms trade extra memory to gain faster execution speed significantly. Space complexity is a common developer interview concept.
27. How to prepare space complexity analysis?
Ans:
- Learning how arrays, recursion stacks, and temporary variables consume memory creates strong conceptual clarity quickly. These components are common sources of extra space in programs. Understanding them improves interview confidence.
- Comparing in-place algorithms with extra-buffer solutions improves technical understanding significantly for interviews. Some methods save memory while others improve speed. Trade-off awareness is highly valuable.
- Practicing examples where memory optimization changes performance adds practical relevance effectively. Real coding problems often reward better space usage. Practice builds stronger judgment.
- Revising common Big O memory patterns helps answer confidently during coding rounds naturally. Familiar formulas improve faster explanations. Repetition strengthens memory.
28. What is Recursion in programming?
Ans:
Recursion is a technique where a function calls itself to solve smaller subproblems repeatedly. It usually requires a clear base condition to stop infinite repeated execution safely. Many tree traversals, backtracking tasks, and divide-conquer algorithms depend on recursion. Recursive solutions may appear elegant but can use additional stack memory significantly. Recursion is frequently asked in coding interviews.
29. How to prepare recursion problems effectively?
Ans:
- Understanding base case and recursive case structure creates immediate clarity for solving problems correctly. Every recursion problem depends on these two parts strongly. Clear basics prevent infinite loops.
- Practicing factorial, Fibonacci, tree traversal, and subset generation builds stronger confidence significantly. These are classic recursion interview examples. Repetition improves speed.
- Learning stack behavior during recursive calls improves debugging ability effectively in interviews. Knowing call flow helps trace errors clearly. This adds technical maturity.
- Converting recursion into iteration when possible adds technical maturity naturally. Some problems run better without recursion depth limits. This shows advanced thinking.
30. Write a program for Binary Search.
Ans:
This example searches an element in a sorted array using binary search.
- #include <stdio.h>
- int main() {
- int arr[5]={10,20,30,40,50};
- int low=0, high=4, mid, key=30;
- while(low<=high){
- mid=(low+high)/2;
- if(arr[mid]==key){
- printf(“Found at index %d”,mid);
- break;
- }
- else if(key>arr[mid]) low=mid+1;
- else high=mid-1;
- }
- return 0;
- }
In this example, the program searches value 30 in sorted array.
31. How to solve binary search questions better?
Ans:
- Learning low, high, and mid pointer movement creates strong conceptual understanding quickly. These pointers control the shrinking search range efficiently. Correct movement is essential.
- Practicing first occurrence, last occurrence, and rotated array problems improves readiness significantly. Interviewers often ask these popular variations. Practice increases confidence.
- Handling boundary conditions carefully prevents common coding mistakes effectively. Many wrong answers happen from index errors. Careful coding improves accuracy.
- Revising logarithmic complexity strengthens interview explanations naturally. Binary search is valued for speed on large inputs. Complexity knowledge impresses interviewers.
32. What is Sorting Algorithm?
Ans:
A sorting algorithm arranges data elements in ascending or descending order systematically. Common methods include bubble sort, merge sort, quick sort, and heap sort. Sorting helps improve searching, reporting, and downstream data processing tasks greatly. Different algorithms vary in speed, memory use, and stability behavior. Sorting is central to software interviews.
33. How to prepare sorting concepts properly?
Ans:
- Learning comparison between O(n²) and O(n log n) sorts builds strong technical clarity quickly. Complexity comparison helps choose better algorithms. This is important in interviews.
- Practicing merge sort and quick sort implementations improves coding readiness significantly. These algorithms are asked frequently in technical rounds. Practice builds confidence.
- Understanding stable versus unstable sorting adds useful interview depth effectively. Stability matters in many real-world scenarios. This shows deeper knowledge.
- Solving array problems using sorting increases problem-solving flexibility naturally. Sorting often simplifies complex logic greatly. It is a powerful technique.
34. What is HashMap?
Ans:
HashMap is a data structure that stores key-value pairs for fast access. It uses hashing techniques to locate data efficiently in average constant time. HashMaps are widely used for counting, caching, indexing, and lookup operations. Performance may reduce during heavy collisions without proper resizing strategies. Hashing is frequently tested in interviews.
35. How to prepare hashing problems strongly?
Ans:
- Learning key-value storage with frequency count examples creates immediate understanding strongly. Counting problems often depend on maps heavily. This builds strong basics.
- Practicing duplicate detection and two-sum style questions improves readiness significantly. These are common hashing interview problems. Practice improves speed.
- Understanding collisions and load factors adds technical maturity effectively. Internal behavior knowledge shows advanced understanding. It adds interview value.
- Revising time complexity advantages helps during interviews naturally. Fast average lookup is the biggest strength of hashing. Clear explanation matters.
36. What is Tree data structure?
Ans:
A tree is a hierarchical data structure consisting of nodes connected by edges. It contains a root node and child relationships across multiple levels. Trees are used in file systems, databases, and search implementations widely. Binary trees and binary search trees are common practical forms. Trees are major coding interview topics.
37. How to prepare tree problems efficiently?
Ans:
- Learning preorder, inorder, and postorder traversals builds strong conceptual foundations quickly. Traversals are the base of most tree problems. Strong basics are essential.
- Practicing height, diameter, and balanced tree problems improves readiness significantly. These are standard interview topics. Practice increases confidence.
- Understanding recursive solutions adds powerful problem-solving capability effectively. Many tree problems are easiest through recursion. This improves coding ability.
- Drawing tree diagrams improves clarity during interviews naturally. Visual structure helps explain logic better. Diagrams reduce confusion.
38. What is Binary Search Tree?
Ans:
Binary Search Tree is a binary tree where left nodes are smaller than root. Right nodes always contain values greater than the current root node. This ordered structure supports efficient search, insertion, and deletion operations. Performance depends on tree balance and overall shape significantly. BST is a common Amazon interview concept.
39. How to prepare BST interview questions?
Ans:
- Practicing search, insert, and delete operations creates strong structural understanding quickly. These are the core BST operations asked often. Practice improves coding speed.
- Learning inorder traversal returns sorted output improves conceptual clarity significantly. This property is a key advantage of BST. Interviewers ask it frequently.
- Studying balanced versus skewed trees adds practical performance awareness effectively. Tree shape directly affects efficiency greatly. This is useful knowledge.
- Solving lowest common ancestor questions builds readiness naturally. LCA is a common BST interview problem. Practice strengthens confidence.
40. What is the difference between Tree and Graph data structure?
Ans:
| Criteria | Tree | Graph |
|---|---|---|
| Structure | Hierarchical node structure. | Network of connected nodes. |
| Cycles | Does not contain cycles. | May contain cycles. |
| Root Node | Usually has one root node. | No mandatory root node. |
| Usage | File systems, BST, hierarchy. | Maps, networks, routing. |
41. How to prepare graph concepts strongly?
Ans:
- Understanding vertices and edges with visual diagrams creates strong clarity quickly. Graph drawing makes connections easier to understand. Visual learning helps greatly.
- Practicing BFS, DFS, shortest path, and cycle detection improves readiness significantly. These are common graph interview topics. Practice builds confidence.
- Learning adjacency list and matrix representations adds technical depth effectively. Representation choice affects memory and speed. This shows maturity.
- Revising real-world network examples helps memory naturally. Examples connect theory with practical use. This improves retention.
42. What is BFS algorithm?
Ans:
Breadth First Search explores graph or tree nodes level by level systematically. It commonly uses a queue to process neighboring nodes in order. BFS is useful for shortest path in unweighted graphs frequently. This method also helps in connectivity and traversal problems widely. BFS is often asked in coding rounds.
43. How to prepare BFS problems properly?
Ans:
- Learning queue-based traversal mechanics creates immediate conceptual clarity strongly. Queue order drives BFS level processing correctly. Basics are essential.
- Practicing grid shortest path and level order tree questions improves readiness significantly. These are common BFS applications. Practice improves confidence.
- Understanding visited arrays prevents repeated processing effectively. Revisiting nodes can create loops or wasted work. Proper tracking is important.
- Revising time complexity improves interview explanations naturally. Complexity discussion shows stronger algorithm understanding. This adds value.
44. What is DFS algorithm?
Ans:
Depth First Search explores nodes deeply before backtracking to other branches later. It can be implemented using recursion or an explicit stack structure. DFS is useful for cycle detection, path finding, and components problems. Many graph and tree problems rely on DFS techniques heavily. DFS is an essential interview topic.
45. How to prepare DFS concepts effectively?
Ans:
- Learning recursive traversal flow creates strong technical understanding quickly for beginners. DFS often uses recursion naturally. Understanding call flow is important.
- Practicing islands, path search, and topological-style problems improves readiness significantly. These are popular DFS applications in interviews. Practice builds strength.
- Comparing DFS with BFS adds valuable conceptual depth effectively. Both methods solve different types of problems. Comparison improves clarity.
- Drawing recursion trees helps debugging naturally during interviews. Visual tracing makes logic easier to explain. Diagrams improve communication.
46. What is Dynamic Programming?
Ans:
Dynamic Programming is a method used to solve overlapping subproblems efficiently. It stores previous results to avoid repeated unnecessary calculations repeatedly. This technique often converts exponential solutions into polynomial-time approaches significantly. Examples include knapsack, Fibonacci, and longest subsequence problems widely. Dynamic programming is highly important at Amazon.
47. How to prepare dynamic programming strongly?
Ans:
- Understanding recursion plus memoization creates immediate DP clarity for beginners quickly. Memoization is often the easiest starting point. It simplifies learning.
- Practicing tabulation methods improves iterative coding confidence significantly. Bottom-up solutions are efficient and common. Practice builds speed.
- Learning state definition and transitions adds strong problem-solving maturity effectively. Good state design is the heart of DP. This is highly important.
- Starting with simple patterns before advanced problems helps progress naturally. Gradual learning prevents confusion. Step-by-step growth works best.
48. What is Database normalization?
Ans:
Database normalization is the process of organizing tables to reduce redundancy. It improves data consistency and avoids update anomalies significantly. Normal forms such as 1NF, 2NF, and 3NF are commonly studied. Well-normalized schemas support cleaner and maintainable database design structures. Normalization is common in developer interviews.
49. How to prepare DBMS basics properly?
Ans:
- Learning tables, keys, joins, and normalization builds strong database foundations quickly. These are core DBMS interview topics. Strong basics improve confidence.
- Practicing SQL queries for filtering and grouping improves technical readiness significantly. SQL coding is common in technical rounds. Practice increases speed.
- Understanding transactions and indexing adds valuable interview depth effectively. These concepts are important in real systems. This shows maturity.
- Revising practical schema examples strengthens confidence naturally. Real examples improve understanding and memory. Practical learning works best.
50. What are second stage Amazon preparation tips?
Ans:
Second stage preparation should emphasize algorithms, recursion, trees, graphs, and databases thoroughly. Candidates should solve medium-level coding problems with time-bound discipline regularly. Clear explanations of logic often matter as much as final code quality. Mock interviews help improve confidence and debugging speed significantly. Consistent structured practice creates stronger success probability.
51. What is SQL?
Ans:
SQL stands for Structured Query Language used to manage relational database systems efficiently. It allows creation of tables, insertion of records, updating values, and querying stored information. Most enterprise applications depend on SQL databases for structured and reliable data storage. Commands are usually divided into definition, manipulation, control, and transaction categories. SQL is a common software developer interview topic.
52. How to prepare SQL interview topics strongly?
Ans:
- Learning SELECT, INSERT, UPDATE, DELETE, and CREATE commands builds a strong database foundation quickly. These commands are the base of most SQL operations in projects. Strong basics improve interview confidence.
- Practicing joins, grouping, sorting, and subqueries improves technical confidence significantly during interviews. These topics are frequently used in reporting and analytics tasks. Practical query skill is highly valuable.
- Understanding indexes, transactions, and normalization adds useful practical depth effectively. These concepts improve performance, consistency, and better schema design. Advanced basics create stronger impact.
- Solving real table-based problems strengthens query writing speed naturally. Hands-on practice improves accuracy and logical thinking greatly. Regular practice builds confidence.
53. What is Primary Key?
Ans:
A primary key is a column or combination of columns uniquely identifying each table row. It prevents duplicate records and ensures every stored row remains distinguishable clearly. Primary keys are widely used for relationships between connected database tables. These keys are usually indexed for faster searching and referencing operations. Primary key basics are frequently asked in interviews.
54. How to explain foreign key concepts clearly?
Ans:
- A foreign key is a column that references the primary key of another table. It creates logical links between related database tables clearly. This is important in relational design.
- It helps maintain referential integrity by allowing only valid linked records significantly. Invalid relationships are reduced through proper constraints. Data quality improves greatly.
- Relationships such as customers and orders commonly use foreign key connections effectively. Many business systems depend on such structured links daily. Examples improve understanding.
- Understanding foreign keys improves database design discussions naturally during interviews. Clear concepts help answer schema-related questions confidently. Strong basics matter.
55. What is Join in SQL?
Ans:
A join combines rows from multiple tables based on related columns between them. It helps retrieve meaningful combined data stored across normalized schemas efficiently. Common join types include inner, left, right, and full outer joins. Joins are essential in reporting, analytics, and business application development systems. SQL joins are highly common interview questions.
56. How to prepare SQL joins properly?
Ans:
- Practicing customer-order and employee-department examples creates immediate join clarity strongly. Real business examples make relationships easier to understand clearly. Practical learning improves memory.
- Understanding inner join versus left join differences improves technical maturity significantly. Knowing result variations helps solve interview queries correctly. Comparison builds clarity.
- Writing multi-table join queries adds practical confidence effectively. Many enterprise reports depend on joining several related tables together. Practice increases readiness.
- Revising null handling in outer joins strengthens interview readiness naturally. Null values often confuse beginners during joins. Careful revision prevents mistakes.
57. What is Operating System?
Ans:
An operating system is system software managing hardware and application resources efficiently. It handles memory, processes, files, devices, and user interactions continuously. Examples include Linux, Windows, macOS, Android, and server operating environments. Without an operating system, application execution would become highly difficult. OS basics are common in developer interviews.
58. Write a program for process creation simulation.
Ans:
This example displays multiple running processes.
- #include <stdio.h>
- int main() {
- for(int i=1;i<=3;i++)
- printf(“Process %d Running\n”, i);
- return 0;
- }
In this example, the program simulates three running processes.
59. What is Process in Operating System?
Ans:
A process is a program currently executing with allocated memory and resources. Each process has its own state, registers, and execution context maintained separately. Modern systems run many processes concurrently through scheduling mechanisms efficiently. Processes provide isolation that improves reliability and security significantly. Process management is frequently discussed in interviews.
60. How to explain thread concepts clearly?
Ans:
- A thread is the smallest execution unit within a process environment. It performs tasks while sharing resources of the parent process clearly. Thread basics are common interview topics.
- Multiple threads share process memory and improve parallel task execution significantly. This helps increase responsiveness and faster work completion. Concurrency becomes stronger.
- Threads are useful for web servers, background tasks, and responsive applications effectively. Many modern systems rely on multithreading daily. Practical examples improve answers.
- Understanding thread safety adds strong interview value naturally. Safe shared resource handling prevents bugs and crashes. This topic is highly valuable.
61. What is Deadlock?
Ans:
Deadlock is a condition where processes wait indefinitely for resources held mutually. No participating process can continue execution without external intervention afterward. Typical causes include circular wait, hold and wait, and no preemption. Deadlock prevention and detection are important operating system strategies. Deadlock is a classic interview topic.
62. How to prepare concurrency concepts properly?
Ans:
- Learning race conditions, locks, semaphores, and deadlocks builds concurrency foundations quickly. These are standard synchronization topics in interviews regularly. Strong understanding is important.
- Practicing producer-consumer style examples improves conceptual clarity significantly. Classic problems help explain coordination between threads clearly. Examples strengthen logic.
- Understanding resource ordering prevents many deadlock situations effectively. Proper sequence design reduces waiting cycles greatly. Prevention is valuable.
- Revising real-world multithreading issues helps interviews naturally. Practical scenarios make answers more professional and convincing. Experience-based thinking helps.
63. What is the difference between HTTP and HTTPS?
Ans:
| Criteria | HTTP | HTTPS |
|---|---|---|
| Security | Data sent without encryption. | Data sent with encryption. |
| Port | Usually uses port 80. | Usually uses port 443. |
| Usage | Basic websites and testing. | Secure websites and payments. |
| Trust | Less secure connection. | More trusted secure connection. |
64. How to explain HTTPS importance clearly?
Ans:
- HTTPS is secure HTTP using encryption for safer communication over networks. Encrypted traffic protects sensitive information during transfer clearly. Security is greatly improved.
- It protects passwords, payments, and personal data from interception significantly. Users trust websites that secure private information properly. This is highly important.
- SSL or TLS certificates authenticate websites and build trust effectively. Certificates verify server identity for users and browsers. Trust improves user confidence.
- Modern production systems strongly prefer HTTPS by default naturally. Search engines and browsers also encourage secure websites regularly. HTTPS is standard practice.
65. What is REST API?
Ans:
REST API is a web service style using resources and standard HTTP methods. It allows systems to communicate through structured endpoints efficiently. Stateless communication makes REST services scalable and simpler to maintain. JSON is commonly used as response and request data format. REST APIs are major developer interview topics.
66. How to prepare API interview questions strongly?
Ans:
- Learning CRUD mapping with GET, POST, PUT, and DELETE creates strong clarity quickly. These methods represent common resource operations in APIs clearly. Fundamentals are essential.
- Understanding status codes such as 200, 404, and 500 improves readiness significantly. Correct codes reflect proper backend design and debugging awareness. This is often asked.
- Practicing sample endpoint design adds practical confidence effectively. Designing routes helps understand real project communication flow. Hands-on practice matters.
- Revising authentication basics strengthens interview maturity naturally. Security concepts like tokens and sessions are valuable topics. Strong revision helps.
67. What is JSON?
Ans:
JSON stands for JavaScript Object Notation used for lightweight data exchange. It stores information using key-value pairs, arrays, and nested objects. JSON is easy for humans to read and machines to parse efficiently. Modern APIs widely use JSON for communication across systems. JSON knowledge is expected in interviews.
68. How to explain caching concepts properly?
Ans:
- Caching stores frequently used data temporarily for faster future access significantly. This reduces repeated processing and delays greatly. Performance improves strongly.
- It reduces repeated database queries and lowers server load effectively. Backend systems become more scalable under traffic pressure. Efficiency increases.
- Application, browser, and distributed caches are common practical forms naturally. Different layers use caching for different needs clearly. Variety improves architecture.
- Understanding cache invalidation adds advanced interview value strongly. Removing stale data correctly is a major real-world challenge. Deeper knowledge helps.
69. What is the difference between Git and GitHub?
Ans:
| Criteria | Git | GitHub |
|---|---|---|
| Meaning | Version control system. | Cloud platform for Git repositories. |
| Usage | Tracks source code changes. | Hosts projects and collaboration. |
| Location | Works locally on system. | Works online through web platform. |
| Purpose | Manage code history. | Share and manage repositories. |
70. How to prepare Git interview topics effectively?
Ans:
- Learning clone, add, commit, push, and pull commands builds fundamentals quickly. These commands are used regularly in team development workflows clearly. Basics are essential.
- Understanding branches and merge conflicts improves team workflow readiness significantly. Branching supports parallel feature development efficiently. Conflict resolution is valuable.
- Practicing revert and reset concepts adds practical technical depth effectively. Recovery commands help manage mistakes safely during development. Strong knowledge matters.
- Using Git regularly strengthens confidence naturally. Hands-on daily use improves speed and command recall greatly. Practice builds mastery.
71. What is Agile methodology?
Ans:
Agile methodology is an iterative software development approach focused on adaptability. Work is delivered in smaller increments with frequent feedback cycles. Teams collaborate closely and adjust requirements as priorities evolve. Scrum is one of the most widely used Agile frameworks globally. Agile concepts appear often in interviews.
72. How to explain Scrum basics clearly?
Ans:
- Scrum divides work into short sprints with measurable deliverables regularly. Short cycles improve delivery visibility and planning clearly. Agile teams benefit greatly.
- Roles commonly include Product Owner, Scrum Master, and development team members significantly. Each role supports project success with clear responsibilities. Structure is important.
- Daily standups improve communication and progress visibility effectively. Quick meetings help remove blockers early. Coordination becomes stronger.
- Sprint reviews and retrospectives support continuous improvement naturally. Teams learn from each cycle and improve future work. Growth mindset matters.
73. Write a program for unit test pass check.
Ans:
This example checks whether expected result matches actual result.
- #include <stdio.h>
- int main() {
- int expected=20, actual=20;
- if(expected==actual)
- printf(“Unit Test Passed”);
- else
- printf(“Unit Test Failed”);
- return 0;
- }
In this example, the unit test passes successfully.
74. How to prepare coding plus testing rounds properly?
Ans:
- Writing clean modular code makes unit testing easier and more reliable significantly. Smaller components are simpler to test and maintain clearly. Good design helps testing.
- Learning assertions, mocks, and test cases improves technical maturity effectively. These tools help validate behavior under different conditions. Testing knowledge is valuable.
- Practicing debugging strategies helps fix errors faster during interviews naturally. Efficient debugging saves time and improves confidence greatly. This skill matters.
- Explaining testing mindset creates stronger professional impression quickly. Employers value candidates who care about quality consistently. Mindset influences selection.
75. What are third stage Amazon interview preparation tips?
Ans:
Third stage preparation should combine coding strength with system and development fundamentals. Candidates should revise SQL, APIs, operating systems, Git, and Agile concepts thoroughly. Balanced communication and structured thinking often improve final performance significantly. Mock technical discussions help explain tradeoffs with confidence effectively. Consistent practice creates stronger selection probability.
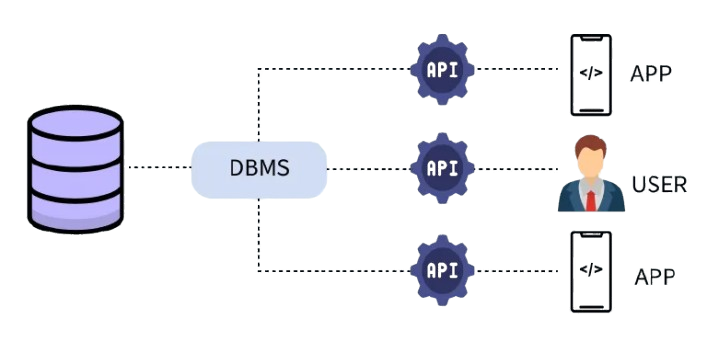
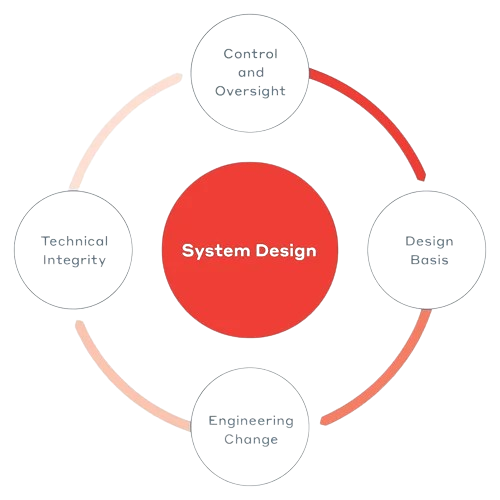
76. What is System Design?
Ans:
System design is the process of planning architecture, components, and interactions of software systems carefully. It focuses on scalability, reliability, maintainability, and performance under real workloads. Developers discuss databases, APIs, caching, load balancing, and deployment strategies often. Good system design balances business needs with technical tradeoffs effectively. System design is important in software developer interviews.
76. Write a program for total servers in system design.
Ans:
This example calculates total active servers in a system.
- #include <stdio.h>
- int main() {
- int web=5, app=3, db=2;
- int total = web + app + db;
- printf(“Total Servers = %d”, total);
- return 0;
- }
In this example, the program calculates total number of servers.
77. How to prepare system design basics strongly?
Ans:
- Learning how users, services, databases, and networks interact creates strong architecture clarity quickly. Understanding complete request flow helps explain systems confidently during interviews. This builds strong fundamentals.
- Understanding scalability, availability, and consistency improves technical maturity significantly during interviews. These concepts are core pillars of modern distributed systems. Strong basics improve answers.
- Practicing designs for chat apps or e-commerce systems adds practical confidence effectively. Real examples help convert theory into usable architecture thinking. Practice creates better recall.
- Explaining tradeoffs clearly creates stronger interviewer impressions naturally. Interviewers value balanced decisions more than memorized buzzwords alone. Clear reasoning matters greatly.
78. What is the difference between Vertical Scaling and Horizontal Scaling?
Ans:
| Criteria | Vertical Scaling | Horizontal Scaling |
|---|---|---|
| Meaning | Increase power of one server. | Add more servers to system. |
| Cost | May need expensive hardware. | Uses multiple machines gradually. |
| Fault Tolerance | Lower if one server fails. | Better due to distributed setup. |
| Use Case | Small to medium systems. | Large scale applications. |
79. How to explain vertical and horizontal scaling clearly?
Ans:
- Vertical scaling increases power of one server using stronger hardware resources significantly. It is simpler initially but has physical upgrade limits. This suits smaller workloads.
- Horizontal scaling adds multiple servers to distribute traffic more efficiently effectively. More machines share requests and improve capacity greatly. This is common in cloud systems.
- Horizontal methods usually improve fault tolerance for large systems naturally. If one server fails others can continue service smoothly. Reliability becomes stronger.
- Understanding both approaches strengthens system design readiness quickly. Choosing correct scaling type depends on budget and workload patterns. Tradeoff knowledge is valuable.
80. What is Load Balancer?
Ans:
A load balancer distributes incoming requests across multiple servers intelligently. It prevents overload on single machines and improves response performance significantly. Load balancers also support failover when one server becomes unavailable unexpectedly. They are widely used in cloud and enterprise production environments. This topic appears often in interviews.
81. How to prepare load balancing concepts properly?
Ans:
- Learning request distribution purpose creates immediate clarity for architecture discussions strongly. Balanced traffic improves speed and server utilization significantly. This is a key concept.
- Understanding round robin and least connections methods improves technical depth significantly. Different algorithms suit different traffic patterns and workloads. Method knowledge helps interviews.
- Studying failover and health checks adds practical relevance effectively. Healthy servers receive traffic while failed nodes are removed quickly. Reliability improves greatly.
- Using website traffic examples improves memory naturally. Real scenarios make abstract concepts easier to explain clearly. Examples create confidence.
82. What is Caching in distributed systems?
Ans:
Caching stores frequently requested data in faster storage for quick retrieval. It reduces repeated database hits and lowers backend processing costs significantly. Distributed systems use caches to improve latency and user experience greatly. Examples include Redis, Memcached, browser cache, and CDN layers widely. Caching is common in Amazon interviews.
83. How to explain cache invalidation clearly?
Ans:
- Cache invalidation means removing stale data when original values change significantly. Fresh data must replace outdated cached responses quickly. Accuracy depends on this process.
- Without invalidation, users may receive outdated information repeatedly and incorrectly. Wrong prices or stock values can harm trust seriously. Correctness matters greatly.
- Time-based expiry and write-through methods are common practical solutions effectively. Different systems choose strategies based on consistency needs. Method selection is important.
- Understanding consistency challenges adds advanced interview value naturally. Interviewers often ask how speed and freshness are balanced carefully. Tradeoffs create strong answers.
84. What is Database Indexing?
Ans:
Database indexing is a technique that speeds up data retrieval operations significantly. Indexes act like book indexes allowing faster search without scanning all rows. They improve SELECT query performance on large tables greatly. Too many indexes may slow insert, update, and delete operations. Indexing is frequently asked in interviews.
85. How to prepare database performance topics strongly?
Ans:
- Learning indexes, query optimization, and joins creates strong database readiness quickly. These topics appear often in backend interviews and projects. Fundamentals are essential.
- Understanding read speed versus write overhead improves technical maturity significantly. Faster reads may come with slower updates in indexed tables. Tradeoffs are important.
- Practicing explain plans and filtering logic adds practical depth effectively. Query plans reveal bottlenecks and inefficient scans clearly. Real practice builds confidence.
- Revising normalization and denormalization supports broader discussions naturally. Data modeling affects both speed and maintainability greatly. Design awareness helps interviews.
86. What is CAP Theorem?
Ans:
CAP theorem states distributed systems cannot fully guarantee consistency, availability, and partition tolerance simultaneously. During network partitions, a system usually prioritizes consistency or availability decisions. This concept helps explain tradeoffs in large distributed databases clearly. Modern cloud systems often balance these properties carefully based on needs. CAP theorem is useful for interviews.
87. How to explain CAP theorem simply?
Ans:
- Consistency means every user sees latest correct data across nodes clearly. All replicas should return same updated information. This ensures trust.
- Availability means requests receive responses even during failures significantly. Systems continue serving users without complete shutdowns. Responsiveness is valuable.
- Partition tolerance means systems continue despite network communication breaks effectively. Nodes may lose connectivity but system still operates partially. This is crucial in distributed setups.
- Tradeoff examples strengthen distributed system interview answers naturally. Practical comparisons make CAP theorem easier to explain clearly. Examples create impact.
88. Write a program for microservices count display.
Ans:
This example displays total microservices used in an application.
- #include <stdio.h>
- int main() {
- int services = 12;
- printf(“Total Microservices = %d”, services);
- return 0;
- }
In this example, the program prints total microservices count.
89. How to prepare microservices concepts properly?
Ans:
- Learning service independence and domain separation creates strong clarity quickly. Each service handles one business capability clearly. This improves modular thinking.
- Understanding APIs, service discovery, and communication improves technical depth significantly. Services need structured interaction to function smoothly. Integration knowledge matters.
- Comparing monolith versus microservices adds practical interview value effectively. Comparison answers show balanced engineering judgment strongly. Interviewers appreciate tradeoff thinking.
- Studying logging and monitoring challenges strengthens readiness naturally. Many services create operational complexity at scale. Awareness improves maturity.
90. What is the difference between Monolithic Architecture and Microservices Architecture?
Ans:
| Criteria | Monolithic Architecture | Microservices Architecture |
|---|---|---|
| Structure | Single deployable application. | Many small independent services. |
| Scaling | Whole app scaled together. | Each service scaled separately. |
| Deployment | Single deployment unit. | Independent deployments. |
| Complexity | Simpler initially. | More operational complexity. |
91. How to explain microservices versus monolith clearly?
Ans:
- Monolith uses one application unit, while microservices split functionality into services distinctly. Deployment style is the main visible difference clearly. Structure affects maintenance.
- Microservices improve independent scaling and deployments significantly for large platforms. Teams can release changes faster with less coordination. Flexibility improves greatly.
- Monolith may be easier to start for small teams effectively. Fewer moving parts simplify early development and debugging. Simplicity has value.
- Tradeoff understanding creates strong system design interview responses naturally. No architecture is perfect for every scenario. Balanced thinking is essential.
92. What is Message Queue?
Ans:
A message queue enables asynchronous communication between separate services or applications. Producers send messages while consumers process them later independently. Queues improve reliability, buffering, and workload smoothing under traffic spikes greatly. Examples include RabbitMQ, Kafka, and cloud queue services widely. Message queues are common system interview topics.
93. How to prepare asynchronous architecture concepts?
Ans:
- Learning producer-consumer patterns creates immediate understanding of queue systems strongly. Producers generate work while consumers process tasks later. This model is widely used.
- Understanding retries and delayed processing improves technical maturity significantly. Failed tasks can be reprocessed without losing requests. Reliability increases greatly.
- Studying order processing examples adds practical relevance effectively. Real commerce systems often use queues for payments and notifications. Examples improve clarity.
- Comparing sync versus async communication strengthens answers naturally. Knowing when to use each style shows design maturity. Tradeoff knowledge matters.
94. What is CDN?
Ans:
CDN stands for Content Delivery Network used for faster global content delivery. It stores static assets on geographically distributed edge servers worldwide. Users receive data from nearest locations reducing latency significantly. CDNs also help absorb traffic spikes and improve availability greatly. CDN basics are useful in interviews.
95. How to explain CDN benefits clearly?
Ans:
- Nearest-server delivery improves page speed and user experience strongly. Shorter distance usually means faster response times. Speed improves satisfaction.
- Static files like images and scripts load faster significantly. Repeated assets are served efficiently from edge locations. Performance becomes smoother.
- Origin servers receive less traffic pressure effectively during heavy demand. Offloading traffic protects backend systems from overload. Stability improves greatly.
- Security protections often add extra practical value naturally. Many CDNs include DDoS filtering and TLS support. Protection is useful.
96. What is Logging in software systems?
Ans:
Logging is the recording of events, errors, and operational information during execution. It helps teams debug issues and monitor production behavior efficiently. Structured logs improve searching and analytics across distributed services greatly. Good logging balances useful detail with storage considerations carefully. Logging concepts appear in interviews often.
97. How to prepare debugging and logging topics properly?
Ans:
- Learning log levels such as info, warning, and error builds clarity quickly. Different levels help filter important events efficiently. Structured logs are valuable.
- Understanding tracing requests across services improves distributed debugging significantly. Request tracing helps locate failures in complex systems. This is highly practical.
- Practicing root cause analysis adds practical confidence effectively. Systematic debugging saves time during incidents greatly. Methodical thinking matters.
- Mentioning clean logs creates stronger professional impression naturally. Useful logs avoid noise while preserving key details. Quality logging is respected.
98. What is Monitoring in production systems?
Ans:
Monitoring tracks health, performance, and availability of running systems continuously. Metrics may include CPU usage, latency, traffic, and error rates. Alerts help teams respond quickly before major customer impact occurs. Modern systems rely on dashboards and observability platforms heavily. Monitoring is valuable in developer interviews.
99. How to prepare reliability engineering basics?
Ans:
- Learning metrics, alerts, and dashboards creates strong operational awareness quickly. These tools show system health in real time clearly. Visibility is important.
- Understanding uptime targets and incident response improves maturity significantly. Reliable teams plan failures before they happen. Preparedness matters greatly.
- Studying latency and throughput relationships adds practical depth effectively. Fast systems need both low delay and good capacity. Performance balance is key.
- Explaining prevention mindset strengthens interview answers naturally. Preventing incidents is better than reacting later. Reliability thinking impresses interviewers.
100. What are fourth stage Amazon interview preparation tips?
Ans:
Fourth stage preparation should combine coding excellence with scalable system thinking thoroughly. Candidates should revise caching, indexing, APIs, queues, and architecture tradeoffs carefully. Simple structured explanations often outperform unnecessarily complex answers significantly. Practice sessions with whiteboard or verbal design improve confidence effectively. Consistent preparation creates stronger final-round success probability.
101. What is Amazon Leadership Principle Customer Obsession?
Ans:
Customer Obsession is a core leadership principle focused on customer trust and satisfaction continuously. Teams begin decisions by understanding customer needs, pain points, and expectations carefully. Long-term loyalty is built through quality experiences rather than short-term gains alone. This principle drives innovation, reliability, and service improvements across products globally. Behavioral interviews often test this principle strongly.
102. How to prepare Customer Obsession interview answers?
Ans:
- Studying examples where customer problems were solved quickly creates strong behavioral readiness significantly. Real service-focused stories show practical alignment with company values clearly. Relevant examples improve answer quality.
- Explaining focus on quality, speed, and trust improves interview relevance effectively. These factors are central to customer satisfaction in most businesses. Balanced answers create stronger impact.
- Using measurable outcomes adds stronger impact during leadership discussions naturally. Numbers such as time saved or complaints reduced increase credibility greatly. Metrics make stories stronger.
- Structured STAR storytelling improves communication confidence quickly. Organized answers are easier for interviewers to understand clearly. Structure reduces confusion.
103. What is the difference between Ownership and Responsibility?
Ans:
| Criteria | Ownership | Responsibility |
|---|---|---|
| Meaning | Taking complete accountability for results. | Handling assigned tasks or duties. |
| Focus | Long-term success and improvement. | Completing current work correctly. |
| Mindset | Proactive and initiative driven. | Task execution driven. |
| Example | Fixing issue beyond assigned scope. | Finishing allocated ticket. |
104. How to prepare Ownership behavioral questions strongly?
Ans:
- Reviewing situations involving initiative and accountability builds strong behavioral clarity quickly. Ownership stories should show responsibility taken without supervision clearly. Initiative is highly valued.
- Showing responsibility for mistakes and corrections improves credibility significantly. Honest learning from failures demonstrates maturity and trustworthiness strongly. Accountability creates respect.
- Explaining long-term thinking adds relevance for Amazon culture effectively. Ownership often includes future improvements beyond immediate tasks. Strategic thinking matters.
- Clear examples with outcomes strengthen final responses naturally. Results help interviewers judge impact and effectiveness clearly. Outcomes improve answers.
105. What is Bias for Action principle?
Ans:
Bias for Action emphasizes timely decisions and fast execution in uncertain conditions. Many opportunities disappear when teams delay decisions excessively for perfection. Calculated risks are encouraged when speed creates customer or business value. Learning quickly from experiments is preferred over slow indecision often. This principle appears regularly in interviews.
106. How to prepare Bias for Action examples properly?
Ans:
- Collecting examples where urgent action solved problems creates strong readiness quickly. Fast response situations show decision-making under pressure clearly. Such stories are valuable.
- Demonstrating calculated risk rather than reckless behavior improves answer quality significantly. Smart judgment matters more than random speed. Balanced action is preferred.
- Highlighting speed with accountability adds interview relevance effectively. Good answers show action plus ownership of results clearly. Responsibility matters greatly.
- Using measurable results strengthens behavioral impact naturally. Tangible outcomes make urgent action stories more believable strongly. Metrics improve confidence.
107. What is Dive Deep principle?
Ans:
Dive Deep means understanding details rather than accepting surface-level assumptions blindly. Strong problem solvers verify data, metrics, logs, and root causes carefully. Leaders balance broad vision with detailed operational awareness consistently. This principle supports better debugging, quality, and decision-making outcomes greatly. Dive Deep is common in technical interviews.
108. How to prepare Dive Deep behavioral answers?
Ans:
- Choosing examples involving investigation and root cause analysis creates clarity quickly. Detailed problem-solving stories show analytical maturity clearly. Good examples build trust.
- Mentioning data-driven decisions improves technical maturity significantly during interviews. Facts and evidence create stronger decisions than guesses. Data focus is valuable.
- Showing persistence through complex issues adds stronger credibility effectively. Deep investigation often requires patience and discipline. Persistence impresses interviewers.
- Explaining final measurable improvement strengthens responses naturally. Outcomes such as reduced errors or faster systems prove impact clearly. Results matter.
109. What is Learn and Be Curious principle?
Ans:
Learn and Be Curious promotes continuous growth through knowledge expansion regularly. Technology changes rapidly, making constant learning essential for long careers. Curiosity often leads to innovation, better tools, and smarter processes. This principle values experimentation and open-minded exploration strongly. Behavioral interviews may assess learning mindset often.
110. How to prepare learning mindset interview responses?
Ans:
- Sharing examples of learning new tools or skills builds strong readiness quickly. Fresh learning stories show adaptability in changing environments clearly. Adaptability is important.
- Demonstrating self-driven growth improves cultural alignment significantly for interviews. Independent learners often perform well in fast-moving teams. Self-motivation matters.
- Mentioning practical application of learned knowledge adds impact effectively. Learning becomes stronger when applied to real problems clearly. Usage proves value.
- Showing curiosity toward improvement strengthens final answers naturally. Curiosity often leads to innovation and better methods strongly. This principle values growth.
111. Write a program for coding assessment score calculation.
Ans:
This example calculates average score of three coding questions.
- #include <stdio.h>
- int main() {
- int q1=80, q2=90, q3=85;
- float avg;
- avg=(q1+q2+q3)/3.0;
- printf(“Coding Score = %.2f”, avg);
- return 0;
- }
In this example, the program calculates coding assessment average score.
112. How to prepare online coding rounds strongly?
Ans:
- Practicing medium-level problems under time limits builds speed and confidence quickly. Timed training simulates real assessment pressure clearly. Practice improves control.
- Reviewing common patterns such as sliding window improves technical readiness significantly. Pattern recognition helps solve unseen questions faster. Repetition builds speed.
- Testing solutions with edge cases adds practical coding quality effectively. Hidden cases often decide final scores strongly. Thorough testing is valuable.
- Managing time across questions strengthens final performance naturally. Smart allocation prevents losing marks on easy questions clearly. Strategy matters.
113. What is the difference between Behavioral Interview and Technical Interview?
Ans:
| Criteria | Behavioral Interview | Technical Interview |
|---|---|---|
| Focus | Past actions and soft skills. | Coding and technical knowledge. |
| Questions | Leadership, teamwork, conflicts. | DSA, system design, debugging. |
| Evaluation | Communication and decision making. | Logic and problem solving. |
| Purpose | Checks cultural fit. | Checks technical readiness. |
114. How to prepare STAR method answers properly?
Ans:
- Situation should explain context clearly without unnecessary details for strong openings. A clear background helps interviewers understand the challenge quickly. Good openings matter.
- Task should define responsibility and challenge involved significantly. This part explains ownership and expectations clearly. Responsibility must be visible.
- Action should highlight decisions, effort, and execution steps effectively. Most evaluation happens through this section strongly. Actions show capability.
- Result should show measurable impact and learning naturally. Outcomes and lessons make stories complete and memorable clearly. Results strengthen answers.
115. Write a program for code optimization comparison.
Ans:
This example compares old runtime and optimized runtime.
- #include <stdio.h>
- int main() {
- int oldTime=10, newTime=4;
- printf(“Saved Time = %d”, oldTime-newTime);
- return 0;
- }
In this example, optimized code saves execution time.
116. How to improve coding optimization skills?
Ans:
- Practicing brute-force to optimal transitions builds stronger problem-solving maturity quickly. This teaches how to refine ideas step by step clearly. Growth becomes visible.
- Learning hash maps, heaps, and binary search improves efficiency options significantly. These tools are common in optimized solutions frequently. Strong tools matter.
- Comparing time and space complexity adds technical depth effectively. Tradeoff analysis shows advanced thinking clearly. Efficiency awareness impresses interviewers.
- Reviewing accepted solutions strengthens growth naturally. Studying better approaches reveals patterns and shortcuts clearly. Learning from solutions is useful.
117. What is communication importance in developer interviews?
Ans:
Communication helps interviewers understand logic, assumptions, and decision-making process clearly. Strong candidates often explain approaches before writing final code solutions. Clear speech reduces confusion during debugging and follow-up discussions significantly. Good communication also reflects teamwork readiness in professional environments. This skill strongly influences outcomes.
118. How to prepare communication for technical rounds?
Ans:
- Practicing explanation of algorithms aloud builds confidence quickly. Verbal clarity improves technical discussions during interviews clearly. Speaking practice is valuable.
- Describing edge cases and tradeoffs improves technical impression significantly. Detailed communication shows deeper thinking strongly. Good explanations matter.
- Using structured steps keeps discussions clear and efficient effectively. Organized communication saves time and avoids confusion clearly. Structure helps performance.
- Mock interviews strengthen fluency naturally over time. Repeated practice reduces hesitation and nervousness strongly. Fluency improves results.
119. What is final interview day strategy?
Ans:
Final interview day success depends on calmness, preparation, and structured thinking consistently. Candidates should read questions carefully and clarify assumptions when needed. Balanced pacing helps solve problems without rushing unnecessarily. Confidence with humility often creates positive impressions significantly. Professionalism matters throughout all rounds.
120. What are ultimate Amazon Software Developer success tips?
Ans:
- Mastering data structures, algorithms, and coding patterns creates the strongest technical foundation for selection rounds. Strong fundamentals support faster and better problem solving clearly. Basics are essential.
- Understanding leadership principles with real examples improves behavioral interview performance significantly and consistently. Culture alignment matters strongly in final decisions. Examples increase impact.
- Practicing communication, optimization, and debugging builds stronger end-to-end readiness effectively. Balanced preparation covers all major interview areas clearly. Complete readiness is valuable.
- Consistent disciplined preparation gives the best probability of securing the role naturally. Daily effort usually outperforms last-minute preparation significantly. Consistency wins.
 LMS
LMS



