
Cybersecurity professionals that engage in ethical hacking, sometimes referred to as penetration testing or white-hat hacking, purposefully try to find weaknesses in computer systems, networks, or applications with the owner’s consent. Enhancing these systems’ security is the main objective of ethical hacking, which aims to find and fix any vulnerabilities before malevolent hackers may take advantage of them.In order to replicate the strategies of cybercriminals, ethical hackers employ a variety of methods and instruments in an effort to find weaknesses in software, setups, and password strength. Their acts are authorised and controlled since they operate inside legal bounds and adhere to tight norms of behaviour.
1.What is ethical hacking?
Ans:
Ethical hacking, sometimes known as penetration testing or white-hat hacking, involves the same processes, techniques, and tools that hackers use, but with one major distinction ethical hackers have explicit permission to break into the systems they test. Their primary purpose is to discover vulnerabilities from a malicious hacker’s viewpoint to better secure systems.
2.Difference between a black hat, white hat, and grey hat hacker?
Ans:
Black Hat Hackers: These individuals hack with malicious intent, often driven by personal or financial gain.
White Hat Hackers: Known as “ethical hackers,” these people obtain authorization to breach systems in an effort to identify weaknesses that will allow organisations to strengthen their security.
Grey Hat Hackers: Operating in the grey area between wrong and right, these hackers might break into systems without permission, but without malicious intent.
3.What is a ‘vulnerability’?
Ans:
A “vulnerability” is described as a weakness or flaw that can be used to harm someone or obtain unauthorised access in a system, piece of software, or procedure.
4.What is a ‘payload’?
Ans:
A “Payload” describes the portion of data that is actually the intended message that is transmitted. In the context of cybersecurity, a payload often refers to the component of malware that performs the malicious action. For example, when a computer worm is delivered to a system, the delivery mechanism is separate from the harmful action it carries out; the latter is the payload. In other contexts, such as in networking, a payload refers to the actual data being sent over the network, excluding headers or metadata.
5. What is penetration testing?
Ans:
Penetration testing, also referred to “pen testing,” is the process of imitating attacks to assess a system’s security and identify vulnerabilities. There are three types of
knowledge gaps: grey (limited knowledge), white (full knowledge), and black (no prior knowledge). The steps in the process are reporting, scanning, exploiting, and reconnaissance. Organisations can use it to find and fix security flaws.
6. Explain “phishing.”
Ans:
Phishing is a cyberattack technique in which malicious actors assume the identity of a reliable organisation in order to deceive victims into disclosing personal information, such as credit card numbers or passwords. This is usually accomplished through phoney emails, texts, or websites that appear authentic but are really meant to spread malware or collect user information.
7.What is SQL injection?
Ans:
SQL injection (SQLi) is a type of cyber attack in which an attacker attempts to execute malicious SQL statements in a target database by inserting or “injecting” them into an input field. This could provide the attacker access to view, edit, or remove data, get around authentication, or even perform database administration tasks.
8. What’s a ‘zero-day’ vulnerability?
Ans:
A ‘zero-day’ vulnerability refers to a software flaw that is unknown to the software’s vendor and doesn’t yet have an official patch or fix. The term “zero-day” implies that developers have “zero days” to fix the issue before it’s potentially exploited by attackers.
9.Describe a ‘man-in-the-middle’ attack.
Ans:
When someone secretly intercepts or relays communication between two parties, it’s known as a “man-in-the-middle” attack. The attacker can eavesdrop, alter, or inject new information into the communication. This can be used to steal sensitive data, inject malicious content, or manipulate transactions.
10. What’s a DDOS attack?
Ans:
The goal of a DDoS (Distributed Denial of Service) attack is to prevent legitimate users from accessing a website, server, or online service by flooding it with excessive traffic from multiple sources. Attackers use a network of compromised devices, often called a “botnet,” to flood the target with requests. This overload can cause the target system to slow down, crash, or become unreachable. DDoS attacks can be motivated by rivalry, protest, or simply malicious intent.
11.What is OS fingerprinting?
Ans:
OS fingerprinting is a technique used to determine the operating system of a remote computer. By analyzing how a computer responds to certain requests or by examining specific characteristics of network packets coming from that computer, an attacker (or a security researcher) can infer its operating system.There are two types
- Active fingerprinting
- Passive fingerprinting
12.What is ‘security through obscurity’?
Ans:
Security through obscurity’ is a concept in the field of security where the protection of information or a system is based on keeping its inner workings secret from potential attackers. The idea is that if the attackers don’t know how the system works, they’ll have a harder time exploiting it.
13.What is a honeypot?
Ans:
The purpose of a honeypot is to prevent, intercept, or identify attempts to access information systems without authorization. Essentially, it’s a decoy system set up to look like a legitimate part of a network or infrastructure, but its primary purpose is to attract and log unauthorized access attempts, often to study the methods and tactics used by attackers.
14. What’s the difference between IDS and IPS?
Ans:
IDS (Intrusion Detection System):
Detects: Monitors network traffic and identifies suspicious patterns or activities.
Alerts: Notifies administrators of the potential threat.
Passive: Doesn’t take direct action against the threat, but logs and reports it.
IPS (Intrusion Prevention System):
Detects and Prevents: Not only identifies malicious activity but also takes predefined actions to stop or mitigate the threat.
Active: Acts upon the threat, which might include blocking traffic, disconnecting sessions, or reconfiguring other security controls.
15.What is CSRF?
Ans:
Cross-Site Request Forgery is an attack in which the victim is duped into submitting a malicious request on the attacker’s behalf. It’s a type of web security vulnerability where an attacker tricking the victim into carrying out undesirable behaviors on a website where the victim has verified their identity.
16. How does HTTPS work?
Ans:
HTTPS provides secure communication over the internet using TLS/SSL encryption. When accessing an HTTPS site, the browser and website exchange certificates and establish a shared “session key” through a process called a handshake. This key encrypts all communication between the two, ensuring data privacy and integrity. After the session, the key is discarded.
17. What’s the principle of “least privilege”?
Ans:
The “least privilege” principle states that a user, process, or system should be granted only the minimal levels of access – or permissions – required to perform its tasks. This reduces potential damage if an attacker compromises that user or process.
18. How do you keep current with security news and vulnerabilities?
Ans:
- Follow security blogs and websites.
- Subscribe to mailing lists like Bugtraq.
- Attend security conferences like DEF CON.
- Monitor vendor websites for security bulletins.
- Check advisories from Computer Emergency Response Teams (CERTs).
- Participate in security forums and communities.
19. What is a rainbow table attack?
Ans:
A rainbow table attack uses precomputed tables filled with hash values for numerous possible passwords to decrypt encrypted passwords quickly. However, by adding a unique “salt” (random data) to each password before it’s hashed, systems can thwart such attacks because the salt ensures each hash is unique, even if users have identical passwords.
20.How would you handle a situation where an unauthorised employee accessed confidential data?
Ans:
- Stop further access.
- Investigate the breach.
- Document findings.
- Alert management.
- Address security gaps.
- Discipline the employee.
21. What is “social engineering”?
Ans:
Social engineering is the manipulation of individuals into disclosing confidential information or performing specific actions, usually for malicious purposes. Instead of targeting software or hardware vulnerabilities, social engineering exploits human psychology. Common tactics include phishing (sending deceptive emails to get users to reveal credentials), pretexting (using a fabricated scenario to obtain information), baiting (enticing users to download malicious software), and tailgating (gaining physical access to a restricted area by following someone).
22. Describe “Two-Factor Authentication (2FA)”.
Ans:
Two different forms of identification must be presented by users in order to obtain access to an account or system using two-factor authentication, which is a security feature. Typically, one form is something the user knows, such as a password, and the second form is something the user possesses, such as a physical token, a smartphone app that generates a code, or a text message with a one-time code.
23.What is “brute force” attack?
Ans:
An attacker may employ a trial-and-error technique known as a “brute force” attack to try and guess a password or PIN. Using this method, the attacker iteratively tries every combination until they find the right one. It is similar to trying every key on a lock until it finally opens.
24. How do “keyloggers” work?
Ans:
Keyloggers are malicious software or hardware tools that record keystrokes made by a user. Their primary purpose is to capture sensitive data, such as passwords or credit card numbers. They can be installed via malicious downloads, email attachments, or physical devices, and once active, they silently log keypresses and send the data to attackers.
25. What is “port scanning”?
Ans:
“Port scanning” is the process of probing a server or host to discover open ports on a computer network. By identifying open ports, an attacker can determine what services are running and potentially find vulnerabilities to exploit. Common tools used for port scanning include Nmap and Netcat.
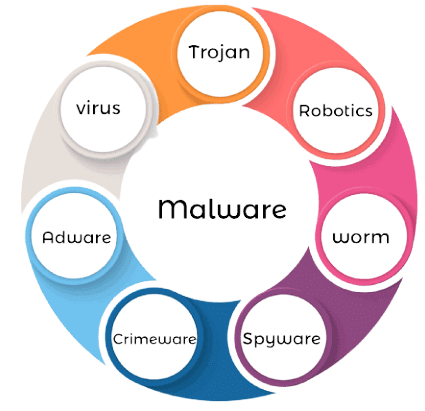
26. What is “malware” and its types?
Ans:
Malware is malicious software intended to harm or exploit devices. Types include
Virus: Replicates and attaches to software.
Worm: Self-spreading across networks.
Trojan: Malicious software in disguise.
Ransomware: Locks data, asks for payment.
Spyware: Monitors users secretly.
Adware: Shows unwanted ads.
27. Explain “VPN” and its importance in ethical hacking.
Ans:
Using a VPN, you can create a encrypted connection to the internet. For ethical hacking, VPNs are necessary because they ensure anonymity, hide the IP address of the user
- Offer a secure testing environment.
- Allow remote access to client networks.
- Protect transmitted data through encryption.
- Help bypass network restrictions or filters.
28. What’s the difference between encryption and hashing?
Ans:
| Aspect | Encryption | Hashing | |
| Reversibility |
original data can be retrieved by decrypting the encrypted message. |
cannot be undone to restore the initial data. | |
| Output Length | the result is usually the same as the input. | A fixed-size hash (digest) is the output; the length is fixed. | |
| Algorithms | SHA-256, SHA-3, and MD5 are a few examples. | examples include DES, RSA, and AES. | |
| Security Focus |
protects data while it’s being sent or stored |
assures the authenticity and integrity of data |
29. Why is “patch management” crucial?
Ans:
Patch management” is crucial because it involves regularly updating software to fix vulnerabilities, reducing the risk of security breaches and ensuring systems remain secure and efficient.
30.What is “steganography”?
Ans:
Steganography is the process of enclosing a piece of data inside another, usually in a way that makes the hidden data difficult to find. Unlike encryption, which scrambles data but makes its presence known, steganography aims to hide information in plain sight. Common methods include embedding text within images, audio files, or video files.
31.What’s a “rootkit”?
Ans:
Malicious software with the purpose of gaining unauthorised access to a computer system and concealing its existence from detection tools is called a “rootkit”. It typically targets the system’s root or administrator level, allowing the attacker to maintain control and execute tasks stealthily. Rootkits can be particularly dangerous because they can evade traditional antivirus or malware detection methods.
32.What’s the importance of “sandboxing”?
Ans:
Sandboxing isolates applications or processes, preventing malicious or malfunctioning programs from damaging or snooping on the rest of the system.
Containment: Limits damage from malicious software.
Testing: Safely assess new code without system risks.
Security: Isolates app vulnerabilities to prevent system-wide breaches.
Control: Manages system resource usage by apps.
Analysis: Allows safe study of malware behaviour.
33.Define “Incident Response” in cybersecurity.
Ans:
In cybersecurity, “incidents response” refers to the methodical process used to handle and control the fallout after a security breach or cyberattack. Its main goal is to handle the situation efficiently, minimising damage, reducing recovery time and costs, and preventing similar future incidents.
34.How does “Address Space Layout Randomization (ASLR)” work?.
Ans:
Operating systems use Address Space Layout Randomization as a security measure to stop memory corruption vulnerabilities from being exploited. ASLR randomises the memory addresses used by processes, making it difficult for an attacker to predict the exact location of specific functions or buffers they might target.
35.What’s the principle behind “defence in depth”?
Ans:
The phrase “defence in depth” described the practice of securing data and systems with several tiers of security controls. Instead of relying on a single security measure, multiple redundant measures are used, ensuring that if one layer fails, others are still in place to thwart an attack.
36.Why are “zero trust” models becoming popular?
Ans:
The zero trust model assumes that threats can come from both outside and inside an organisation, so no entity (user or system) is inherently trusted.
- Advanced cyber threats surpassing traditional defences.
- The rise of remote work.
- Increased cloud service adoption.
- Recognition of internal threats.
- Ability to set detailed access controls.
- Minimised attack avenues by verifying all access.
37.What’s a “firewall”?
Ans:
One type of network security tool or software called a “firewall” is used to track, filter, or stop data flow into and out of a system or network. Its primary goal is to build a barrier between a reliable internal network and a dubious external network, such as the internet, in order to stop malicious or unauthorised access.
38.How does “ARP spoofing” work?
Ans:
ARP spoofing is a kind of attack where a malevolent actor uses a local network to send fake ARP (Address Resolution Protocol) messages. This links the attacker’s MAC address to a machine or server that is authorised by its IP address.
- The attacker sends an ARP response, not a request, to trick a device into associating the attacker’s MAC address with an IP of another device (often the gateway).
- The victim updates its ARP table with the false mapping.
- Data intended for that IP now goes to the attacker first.
39.What is a “botnet”?
Ans:
A “botnet” is a compromised computer network that is typically under the control of a single entity or group, usually with malevolent intent. These compromised machines, sometimes referred to as “bots” or “zombies,” have malware on them that gives the attacker remote control over the machine.
40.What is the significance of the “CIA triad” in cybersecurity?
Ans:
Confidentiality:Ensures that data is accessible only to those with proper authorization, preventing unauthorised access.
Integrity: Ensures data remains unaltered and trustworthy, preventing unauthorised changes.
Availability:Ensures systems and data are accessible when needed, preventing service disruptions.
41.What is a “watering hole” attack?
Ans:
A watering hole attack occurs when a hacker gains access to a website that a specific group of people frequently visits. Malware infects the targets when they visit the website. It would be like poisoning an organic watering hole to target a particular species.
42.Define “Session Hijacking.”
Ans:
Session hijacking, or session takeover, involves taking control of a user session after successfully stealing or predicting a valid session ID. It allows unauthorised access to the web server, bypassing user credentials.
43.How does a “buffer overflow” attack work?
Ans:
A buffer overflow occurs when more information is written to a buffer than it can handle. This can corrupt nearby memory spaces, resulting in erratic programme behaviour, crashes, or the execution of malicious code. Attackers take advantage of this by sending excessive data and, on occasion, malicious code within the overflowed buffer.
44.Why is “wireless network” security important, and how can it be compromised?
Ans:
Wireless networks can be easily accessed as they transmit data over airwaves. Threats include rogue access points, eavesdropping, man-in-the-middle attacks, and more.
Weak Encryption: Outdated methods like WEP are easily cracked.
Sniffing: Intercepting and analyzing data packets.
Rogue Hotspots: Fake Wi-Fi access points trick users.
Dictionary Attacks:Guessing passwords using common words or software.
Man-in-the-Middle: Intercepting communication undetected.
45.Explain the “Heartbleed” vulnerability.
Ans:
“Heartbleed” is a 2014 vulnerability in the OpenSSL cryptography library affecting the TLS protocol. The bug, found in the heartbeat extension, allowed attackers to extract chunks of memory from servers, potentially exposing sensitive data like private keys, usernames, and passwords. The widespread impact was due to OpenSSL’s extensive use. Remediation involved patching OpenSSL and renewing compromised certificates.
46.What is the role of “threat intelligence” in ethical hacking?
Ans:
- Insights into current threat trends.
- Focus on high-priority vulnerabilities.
- Knowledge of latest attack methodologies.
- Improved incident response strategies.
- Ability for proactive defence against emerging threats.
47.How is “machine learning” influencing cybersecurity and ethical hacking?
Ans:
- Enhancing real-time threat detection through pattern recognition.
- Detecting phishing attempts in emails.
- Predicting future threats from historical data.
- Automating responses to detected threats.
- Assisting in vulnerability identification and prioritisation.
- Improving accuracy of vulnerability scanning tools.
48.Explain “DNS spoofing.”
Ans:
The attack known as “DNS spoofing,” or “DNS cache poisoning,” involves inserting bogus DNS data into a DNS resolver’s cache. This causes users who request the address of a specific website to be directed to a potentially malicious site controlled by the attacker, rather than the legitimate site.
49.What are “Logic Bombs” in the context of malware?
Ans:
Logic Bombs” are harmful codes that are implanted into software or systems and stay dormant until they are activated by a particular circumstance or occurrence. Once the set condition is met, the logic bomb activates and executes its malicious payload, which can include data deletion, corruption, or other damaging actions.
50.Why are “insider threats” particularly challenging?
Ans:
- Insiders have legitimate access and trust.
- They know internal systems and practices.
- Malicious activities can resemble regular tasks.
- Threats range from negligence to intentional harm.
- Personal motives can drive unpredictable actions.
51.Describe “red teams” and “blue teams”in cybersecurity.
Ans:
- Red teams simulate cyber-attacks against an organisation to test its defences.
- Blue teams are responsible for defending against the simulated attacks.
- The process helps identify vulnerabilities and weaknesses in an organisation’s security posture.
52.What is “whaling” in the context of phishing attacks?
Ans:
A specific kind of phishing attack known as “whaling” is directed towards high-profile targets within an organisation, such as senior executives. It is frequently more sophisticated, speaks directly to the particular person, and appears credible by utilising pertinent professional or personal information.
53.What’s the concept behind “security by design”?
Ans:
“Security by design” means integrating security measures into the product design and development processes from the outset, rather than adding them to an existing system. It emphasises the importance of security in the initial design, ensuring that the system is inherently secure from the beginning.
54.Explain the “risk assessment” process in ethical hacking.
Ans:
Risk assessment involves identifying vulnerabilities in a system, determining potential threats that could exploit these vulnerabilities, evaluating the potential damages if these vulnerabilities were exploited, and then prioritising the risks in light of their possible significance and propensity to arise. Ethical hackers use this to guide their efforts and provide recommendations.
55.What’s the difference between “active” and “passive” reconnaissance?
Ans:
Active Reconnaissance: Involves sending packets, port scanning, or pinging the target system in order to engage in direct communication with it. Intrusion detection systems are able to identify this strategy because it communicates directly with the target.
Passive Reconnaissance:Gathering information without directly interacting with the target system, such as using search engines, public records, or social media. It’s stealthier, reducing the risk of detection.
56.What is “full-disk encryption”?
Ans:
A security technique called “full-disk encryption” (FDE) encrypts every piece of data on a storage device, including user files, applications, and the operating system. This ensures that if the device is lost or stolen, unauthorized individuals cannot access the data without the appropriate encryption key or password.
57.How does a “cross-site scripting (XSS)” attack work?
Ans:
XSS attacks inject malicious scripts into web pages viewed by users. These scripts can access cookies, session tokens, and other sensitive information from the user’s browser, potentially leading to session hijacking or other malicious actions.
- A web application doesn’t properly validate or escape user input.
- An attacker submits malicious JavaScript code through this input.
58.Explain “endpoint security.”
Ans:
Endpoint security” describes the tactics and fixes used to safeguard computer networks that are accessed remotely by endpoints such as tablets, laptops, cellphones, and other devices. Its purpose is to ensure that these devices follow a set standard of security before granting them access, considering they can be potential entry points for threats.
59.What’s a “SYN flood attack”?
Ans:
Endpoint security” describes the tactics and fixes used to safeguard computer networks that are accessed remotely by endpoints such as tablets, laptops, cell phones, and other devices. Its purpose is to ensure that these devices follow a set standard of security before granting them access, considering they can be potential entry points for threats.
60.Describe the importance of “security awareness training.”
Ans:
Security awareness training educates employees about cyber threats and safe online habits. Since human error is often a significant vulnerability, trained employees can recognize and prevent potential security threats, reducing risk.
61.What are “web application firewalls (WAF)”?
Ans:
A WAF is a specific kind of firewall that filters, monitors, and blocks HTTP traffic to and from web applications. It filters and monitors HTTP traffic between a web application and the Internet to defend against a variety of web-based attacks, including SQL injection and XSS.
62.How does “fileless malware” operate?
Ans:
Fileless malware operates directly in memory, rather than writing files to the disk, making it harder to detect using traditional antivirus solutions. It can exploit legitimate tools and processes on a computer to execute malicious activities.
63.What are the primary principles of “digital forensics”?
Ans:
The preservation, identification, extraction, and documentation of electronic evidence are all part of the field of digital forensics. Principles include ensuring data integrity (unaltered evidence), proper chain of custody, and maintaining a clear and documented methodology.
64.Describe “mobile device management (MDM)” in the context of security.
Ans:
MDM is a security software used by IT departments to monitor, manage, and secure employees’ mobile devices. It can enforce security policies, remotely wipe data, or lock devices, ensuring that lost or stolen devices don’t pose a significant risk to the organisation.
65.How does a “drive-by download” attack work?
Ans:
In a drive-by download attack, a user unknowingly downloads malicious software by visiting a compromised website, viewing an email, or clicking on a deceptive popup window. The download occurs without the user’s knowledge or explicit consent.
66.What is “multi-factor authentication (MFA)”?
Ans:
In order to access an account with MFA, users must present several forms of identification. Generally, this involves something they possess (token or smartphone), something they know (password), and occasionally something they are (facial recognition or fingerprint).
67.How does “network segmentation” improve security?
Ans:
- Restricting attackers’ movement within segments.
- Reducing exposure from vulnerabilities.
- Simplifying traffic monitoring and anomaly detection.
- Allowing segment-specific security policies.
- Localising damage during breaches for easier containment.
68.What’s a “reverse shell”?
Ans:
A “reverse shell” is a kind of shell where the attacking system and the target machine exchange messages. Instead of the attacker sending commands to the target, as in a typical shell, the target system sends its shell session to the attacker, allowing the attacker to control it.
69.Why is “patching” important in cybersecurity?
Ans:
Patching is the process of updating software, such as operating systems and applications. Patches frequently fix vulnerabilities, and failing to apply them on time exposes organisations’ systems to known threats.
70.What is “payload” in the context of cyber attacks?
Ans:
In cyberattacks, the payload refers to the part of the malware that performs the malicious action after the malware is delivered to the target. It’s the ‘active’ part of the malware that causes harm or unauthorised access.
71.What is “data exfiltration”?
Ans:
The term “data exfiltration” describes the unapproved removal of data from a computer. It can be manual by a person using data storage or automated, as seen with malware or advanced persistent threats that transmit data to a hacker’s domain.
72.How do “ransomware” attacks operate?
Ans:
Ransomware is a form of malware that encrypts the files of a victim. Following that, the attacker requests that the victim pay a ransom in order to regain access to the data. To maintain the attacker’s anonymity, payment is usually requested in cryptocurrency.
73.What are “heuristic” methods in virus detection?
Ans:
Many antivirus programmes use heuristic analysis as a technique to find new virus variants and previously unidentified computer viruses that are already in the wild. To find questionable activity, it examines the behaviours of codes.
74.What is “IoT security”?
Ans:
The protection of linked devices and networks inside the Internet of Things is known as IoT security. Given the vast number of devices and their integration into various facets of life, ensuring their security is paramount to prevent potential breaches or misuse.
75.What is a “security policy”?
Ans:
A “security policy” is a formalised document or set of guidelines within an organisation that outlines how to identify, prevent, and respond to various types of security threats and incidents. It covers areas like access controls, user authentication, password requirements, incident response procedures, and more.
76.Why is “data sanitization” essential?
Ans:
Data sanitization ensures that sensitive information is irrevocably destroyed or removed from storage media before disposal or reuse. It prevents unauthorized access to the data later.
- Blocking data retrieval by unauthorized users.
- Preventing data leaks from old devices.
- Meeting regulatory requirements.
- Maintaining trust.
- Reducing exposure risks.
77.What’s the difference between “threat,” “vulnerability,” and “risk”?
Ans:
Threat: Potential cause of harm (e.g., hackers).
Vulnerability: System weakness that can be exploited.
Risk: Likelihood and impact of a threat exploiting a vulnerability.
78.Explain the importance of “incident response plans.”
Ans:
Incident response plans provide a structured approach for handling cybersecurity breaches. A well-laid-out plan ensures quick, effective, and orderly response to incidents, minimising damage and recovery time.
79.What’s a “Trojan horse” in cybersecurity?
Ans:
A “Trojan horse,” also known as a “Trojan,” is a type of malicious software that conceals itself within or is disguised as legitimate software. Trojans function as carriers of malware to a host system, as opposed to viruses and worms, which replicate themselves.
80.Why is “data masking” important?
Ans:
Data masking, or data obfuscation, is used to protect sensitive information in non-production environments. It allows realistic data sets to be used for testing or development without exposing the actual sensitive data.
81.How does “network topology” affect security?
Ans:
The arrangement or layout of various elements in a network, known as network topology, affects security by determining the data flow, accessibility, and control points. Some topologies may inherently offer more security by limiting direct access points or controlling data flow paths.
82. Difference between “intrusion detection systems (IDS)” and “intrusion prevention systems (IPS)”?
Ans:
IDS (Intrusion Detection System): Detects suspicious activities or violations on the network.
IPS (Intrusion Prevention System): Detects and Prevents malicious activity in real-time.
83.Why are “rootkits” particularly dangerous forms of malware?
Ans:
Rootkits are designed to gain administrator-level control over a system without detection.
Stealth: They can hide their presence, making detection difficult.
Deep Access: Often operate at the kernel level, giving them extensive system control.
Persistence: Can embed themselves to automatically run at system startup.
Bypass Protections: Can disable or circumvent security software.
Data Theft: Capable of capturing sensitive data without detection.
84.What’s “fuzz testing” or “fuzzing”?
Ans:
Fuzz testing, also known as “fuzzing,” is a software testing technique in which a software application is given random or malformed data as input in order to find security flaws and coding errors.
85.Why is “user behaviour analytics (UBA)” becoming significant in cybersecurity?
Ans:
UBA uses machine learning, algorithms, and statistical analyses to recognize when user behaviour deviates from established patterns, indicating potential security threats, making it easier to detect insider threats or compromised accounts.
86.What is a “zero trust architecture”?
Ans:
Zero trust architecture operates on the principle that no one, whether inside or outside the organisation, is implicitly trusted. Every access request is authenticated, authorised, and encrypted regardless of its origin.
87.How do “malvertising” attacks work?
Ans:
Malvertising involves injecting malicious ads into legitimate advertising networks and webpages. When users click on these ads or sometimes just view them, they can download malicious code or be redirected to malicious sites.
88.What is a “firewall pinhole”?
Ans:
A firewall pinhole allows a specific form of traffic to bypass the firewall, enabling specific trusted external users or applications to connect to an internal system directly.
89.Describe the role of “threat hunting” in cybersecurity.
Ans:
Threat hunting” is a proactive cybersecurity technique in which professionals actively look for indicators of system and network penetration. Instead of waiting for automated alerts, threat hunters seek out anomalies using advanced tools, analytics, and threat intelligence.
90.What’s “code obfuscation”?
Ans:
Code obfuscation” is the practice of modifying software source code or binary code to make it difficult to understand and reverse engineer, while retaining its original functionality. The aim is to protect intellectual property, hide vulnerabilities, or prevent tampering.
91.Explain the “principle of separation of duties (SoD)” in cybersecurity.
Ans:
The “principle of separation of duties (SoD)” divides responsibilities to ensure no one person has unchecked power. Benefits include:
- Reducing fraud and errors.
- Enhancing accountability.
- Lowering insider threat risks.
92.What’s a “dictionary attack”?
Ans:
A “dictionary attack” refers to a technique wherein an individual attempts to obtain unapproved access to a system or account by methodically using each word in a dictionary as a passphrase or password. Rather than attempting to break into a system by guessing passwords at random, attackers use dictionaries or lists of frequently used passwords, including variations and combinations.
93.What’s the difference between “authentication” and “authorization”?
Ans:
“Authentication” is the procedure of verifying a user’s identity (for example, through the use of passwords). “Authorization” governs what an authenticated user is permitted to do (for example, access permissions).
94.Why is “regular auditing” important in cybersecurity?
Ans:
Regular auditing” in cybersecurity is vital to:
- Detect vulnerabilities and misconfigurations.
- Ensure policy adherence and user accountability.
- Provide investigation records.
- Refine security measures through feedback.
- Comply with industry or governmental regulations.
95.What is “cyber threat intelligence”?
Ans:
Cyber threat intelligence entails gathering and analysing information about potential security threats. It provides insight into potential attacks, their methodologies, and tools, allowing organisations to stay one step ahead.
96.How do “web shells” operate in cyber attacks?
Ans:
A web shell is a script that is used to run on a web server and control the machine remotely. Attackers use it to execute orders, steal data, or compromise the security header system further.
97.What are “security headers” in web security?
Ans:
Security headers” in web security are directives sent from the server in the HTTP response headers to instruct the browser on how to behave when handling the site’s content. These headers can mitigate various types of attacks and ensure safe interactions with websites.
98.What distinguishes “gray box,” “white box,” and “black box” testing?
Ans:
Black box testing examines the functionality without any knowledge of internal workings. White box testing involves a complete understanding of the internal mechanisms. Gray box is a hybrid approach with partial knowledge of the internals.
99.What is Zeea “time-based blind SQL injection”?
Ans:
A “time-based blind SQL injection” involves attackers deducing database information by noting response delays. Attackers inject SQL queries making the database wait (using commands like SLEEP).
100.Why are “security misconfigurations” a common risk?
Ans:
Security misconfigurations happen when security settings are defined, implemented, and maintained improperly. It’s common because of the complexity of certain applications and lack of knowledge or oversight in securely configuring every aspect of an application or system.






