
Quicken your Cyberoam professional career with the help of ACTE’s frequently asked Cyberoam Interview Questions and Answers article. Cyberoam technology is best suited for those who know Cyber security services, Wi-Fi troubleshooting, LAN networking, Network engineering, MPLS, IP routing, Router configuration, and IP addressing. Learning Cyberoam interview questions may be a stepping stone to enter into any top company. Along with this article, those who think to start their career as a Cyberoam expert, please visit our website. Let’s begin our journey to learn this beautiful technology;
1. What is Cyberoam?
Ans:
Cyberoam is a network security solution that provides a comprehensive set of security features, including firewall, VPN, anti-virus, anti-spam, content filtering, and intrusion prevention. It is designed to protect networks from various cyber threats and ensure a secure computing environment.
2. Explain the role of a firewall in Cyberoam.
Ans:
In Cyberoam, the firewall acts as a barrier between a trusted internal network and untrusted external networks, monitoring and controlling incoming and outgoing network traffic. It enforces access policies, prevents unauthorized access, and safeguards against cyber threats.
3. What is the significance of VPN in Cyberoam?
Ans:
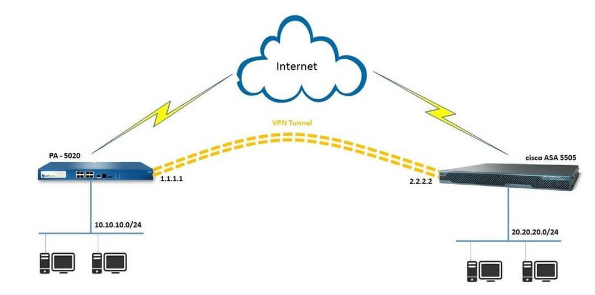
- Virtual Private Network (VPN) in Cyberoam allows secure communication over the internet by creating a private network from a public internet connection.
- It ensures confidentiality and integrity of data transmission, making it a vital component for secure remote access and site-to-site connectivity.
4. How is content filtering handled by Cyberoam?
Ans:
Cyberoam uses content filtering to prevent access to unwanted or dangerous websites in order to control and monitor internet usage. It classifies websites according to their content and gives administrators the ability to set access controls through rules, guaranteeing a safe and effective online environment.
5. Explain the role of anti-virus in Cyberoam.
Ans:
The anti-virus feature in Cyberoam protects networks by scanning files and data for malicious code or malware. It identifies and eliminates viruses, trojans, worms, and other threats, preventing them from infecting the network and compromising data integrity.
6. In what ways does Cyberoam tackle the problem of spam?
Ans:
- Cyberoam uses anti-spam techniques to weed out unsolicited and maybe dangerous emails.
- It employs a number of methods, including content analysis, blacklisting, and heuristics, to detect and prevent spam so that consumers only get secure and authentic emails.
7. What is the purpose of intrusion prevention in Cyberoam?
Ans:
- Intrusion Prevention System (IPS) in Cyberoam detects and prevents network-based attacks by monitoring and analyzing network traffic for malicious activities.
- It adds an extra layer of security by proactively blocking known and unknown threats, enhancing the overall security posture.
8. How does Cyberoam support user authentication?
Ans:
Cyberoam offers multiple authentication methods, including username/password, digital certificates, and two-factor authentication, to verify the identity of users. This ensures that only authorized individuals gain access to the network, enhancing overall security.
9. Describe the idea of Cyberoam’s bandwidth management.
Ans:
Cyberoam’s bandwidth management feature enables administrators to assign and regulate the amount of bandwidth used by various users and apps. By avoiding bandwidth abuse, giving priority to essential applications, and enabling equitable resource distribution, it guarantees optimal network performance.
10. How does Cyberoam integrate with different network architectures?
Ans:
| Aspect of Integration | Description |
|---|---|
| Deployment Modes | Cyberoam supports different deployment modes, including Gateway Mode, Transparent Mode, and Bridge Mode. Organizations can choose the mode that best fits their network architecture and security requirements. |
| Gateway Mode | In Gateway Mode, Cyberoam is deployed as a gateway between the internal network and the external network (Internet). It acts as a security checkpoint for all incoming and outgoing traffic, allowing organizations to implement comprehensive security policies. |
| Transparent Mode | Transparent Mode enables Cyberoam to operate seamlessly within the network without requiring changes to IP addresses. It acts as a transparent bridge, allowing traffic to pass through while applying security policies effectively. |
| Bridge Mode | Cyberoam’s Bridge Mode facilitates inline deployment, where it is placed between network segments. This mode is suitable for scenarios where organizations want to control traffic flow between different parts of their network. |
11. How does Cyberoam handle network traffic logging?
Ans:
Cyberoam maintains detailed logs of network traffic, providing visibility into user activities and potential security incidents. These logs include information on websites visited, applications used, and security events, enabling administrators to analyze and respond to security issues effectively.
12. Explain the concept of SSL VPN in Cyberoam.
Ans:
SSL VPN in Cyberoam enables secure remote access to the network for users through encrypted connections. It ensures the confidentiality of data during transmission, allowing remote users to access internal resources securely without compromising sensitive information.
13. What role does Identity-based Security play in Cyberoam?
Ans:
- Identity-based Security in Cyberoam associates security policies and controls with specific user identities rather than IP addresses.
- This approach enhances security by allowing administrators to create more granular and personalized policies based on individual user profiles.
14. How does Cyberoam address the challenge of application control?
Ans:
Cyberoam’s application control feature allows administrators to regulate and monitor the use of specific applications within the network. By categorizing and controlling applications, organizations can mitigate security risks and ensure the appropriate use of network resources.
15. What is the purpose of Data Loss Prevention (DLP) in Cyberoam?
Ans:
- Cyberoam’s Data Loss Prevention (DLP) feature prevents unauthorized access and transmission of sensitive data.
- It monitors and controls the movement of sensitive information, reducing the risk of data breaches and ensuring compliance with regulatory requirements.
16. How does Cyberoam handle network monitoring and reporting?
Ans:
Cyberoam provides robust network monitoring and reporting capabilities, offering real-time visibility into network activities. Administrators can generate detailed reports on user behavior, security events, and network performance, facilitating informed decision-making and proactive security measures.
17. Explain the concept of High Availability in Cyberoam.
Ans:
High Availability in Cyberoam ensures uninterrupted network operation by deploying redundant systems. In the event of a hardware failure or other disruptions, the backup system takes over seamlessly, minimizing downtime and ensuring continuous availability of network services.
18. How does Cyberoam support centralized management?
Ans:
Cyberoam offers centralized management through tools like Cyberoam Central Console (CCC), allowing administrators to manage multiple Cyberoam devices from a single console. This centralized approach simplifies configuration, monitoring, and maintenance tasks across distributed networks.
19. What role does Threat Intelligence play in Cyberoam?
Ans:
- Cyberoam leverages Threat Intelligence to enhance its ability to detect and prevent emerging threats.
- By incorporating real-time threat intelligence feeds, Cyberoam stays updated on the latest security threats, ensuring a proactive defense against evolving cyber threats.
20. How does Cyberoam contribute to regulatory compliance?
Ans:
Cyberoam aids in regulatory compliance by offering features like content filtering, data loss prevention, and logging capabilities. These help organizations adhere to industry-specific regulations and standards, ensuring that their network security measures align with legal and compliance requirements.
21. What is the significance of Network Address Translation (NAT) in Cyberoam?
Ans:
Cyberoam uses Network Address Translation to map private IP addresses to a single public IP address, enhancing the security and privacy of internal networks. NAT allows multiple devices to share a common public IP, acting as a barrier between the internal network and external threats.
22. Explain the role of Botnet Protection in Cyberoam.
Ans:
- Cyberoam’s Botnet Protection detects and blocks communication between network devices and known botnet command and control servers.
- This prevents devices from becoming part of a botnet, enhancing network security and reducing the risk of malicious activities.
23. How does Cyberoam handle Secure Sockets Layer (SSL) inspection?
Ans:
Cyberoam performs SSL inspection by decrypting and inspecting SSL-encrypted traffic, ensuring that malicious content is not concealed within encrypted connections. This adds an additional layer of security, as threats hidden within SSL-encrypted traffic can be identified and blocked.
24. What role does Intrusion Detection System (IDS) play in Cyberoam?
Ans:
- Cyberoam’s Intrusion Detection System monitors network and/or system activities for malicious exploits or security policy violations.
- It analyzes traffic patterns and identifies potential threats, providing alerts to administrators and helping to prevent security breaches.
25. How does Cyberoam facilitate User and Role-based Access Control?
Ans:
Cyberoam allows administrators to define access policies based on user identities and roles. This ensures that users have appropriate access privileges according to their roles within the organization, minimizing the risk of unauthorized access to sensitive resources.
26. Explain the concept of Sandbox Protection in Cyberoam.
Ans:
Cyberoam employs Sandbox Protection to analyze and detect threats in a virtual environment before allowing potentially malicious files to enter the network. This proactive approach helps in identifying and blocking new and unknown malware that may bypass traditional security measures.
27. What is the purpose of SSL VPN Portal in Cyberoam?
Ans:
Cyberoam’s SSL VPN Portal provides a secure web-based interface for remote users to access internal resources. It offers a user-friendly experience while ensuring the confidentiality and integrity of data during remote access sessions.
28. How does Cyberoam handle Denial of Service (DoS) attacks?
Ans:
- Cyberoam employs various mechanisms, such as rate limiting and traffic prioritization, to mitigate the impact of Denial of Service attacks.
- By identifying and blocking malicious traffic, Cyberoam helps maintain network availability and prevent disruptions caused by DoS attacks.
29. Explain the concept of WAF Profiling in Cyberoam.
Ans:
WAF Profiling in Cyberoam involves creating and customizing security profiles for web applications. This allows administrators to define specific security policies and controls tailored to the unique requirements of each web application, enhancing protection against web-based threats.
30. What is the role of SSL Inspection Bypass in Cyberoam?
Ans:
- SSL Inspection Bypass in Cyberoam allows certain traffic to bypass SSL inspection for privacy or compliance reasons.
- This feature ensures flexibility in handling encrypted traffic, allowing organizations to balance security needs with privacy considerations.
31. How does Cyberoam support Multi-WAN Link Load Balancing?
Ans:
Cyberoam’s Multi-WAN Link Load Balancing optimizes network performance by distributing traffic across multiple internet connections. This not only improves bandwidth utilization but also enhances network reliability and availability.
32. Explain the concept of Application Risk Classification in Cyberoam.
Ans:
- Cyberoam classifies applications based on their associated risks, allowing administrators to prioritize and control them accordingly.
- By understanding the risk levels of different applications, organizations can enforce policies that align with their security objectives.
33. What is the role of Reverse Proxy in Cyberoam’s Web Application Firewall?
Ans:
Cyberoam’s Web Application Firewall uses Reverse Proxy to act as an intermediary between external users and web servers. This enhances security by masking the identity of internal servers and providing an additional layer of protection against web-based attacks.
34. How does Cyberoam handle Threat Correlation?
Ans:
Cyberoam employs Threat Correlation to analyze multiple security events and incidents collectively. By correlating information from various sources, it enhances the accuracy of threat detection and provides a more comprehensive view of potential security risks.
35. What role does Captive Portal play in Cyberoam?
Ans:
- Cyberoam’s Captive Portal ensures that users authenticate themselves before accessing the network.
- This adds an extra layer of security by preventing unauthorized access and enabling organizations to control and monitor user logins effectively.
36. How does Cyberoam address the challenge of Shadow IT?
Ans:
Cyberoam helps organizations manage Shadow IT by providing visibility into all network activities. By monitoring and controlling application usage, administrators can identify and address unauthorized or unapproved applications, reducing the risks associated with Shadow IT.
37. Explain the concept of Policy-based Routing in Cyberoam.
Ans:
Policy-based Routing in Cyberoam allows administrators to define routing policies based on specific criteria, such as source IP addresses or application types. This enables organizations to optimize network traffic flow and implement routing strategies aligned with their security and performance objectives.
38. How does Cyberoam support Customizable Reporting?
Ans:
Cyberoam’s reporting features allow administrators to generate customized reports based on specific criteria. This flexibility in reporting ensures that organizations can focus on the information most relevant to their security and compliance needs.
39. Why is Geo-location Filtering Used in Cyberoam?
Ans:
- Organizations may manage access based on users’ geographical locations with Cyberoam’s Geo-location Filtering.
- By blocking access from locations that can provide a greater security risk, this feature raises the bar for security.
40. Explain the role of Endpoint Data Protection in Cyberoam.
Ans:
Cyberoam’s Endpoint Data Protection feature helps organizations secure sensitive data on endpoint devices. It includes capabilities such as data encryption, device control, and data loss prevention, providing comprehensive protection against data breaches and unauthorized access.
41. What role does Network Forensics play in Cyberoam?
Ans:
- Cyberoam’s Network Forensics capabilities enable organizations to investigate and analyze security incidents by capturing and inspecting network traffic.
- This aids in identifying the source and impact of security breaches, facilitating effective incident response.
42. How does Cyberoam handle Virtual Private LAN Service (VPLS)?
Ans:
Cyberoam supports Virtual Private LAN Service (VPLS), allowing organizations to extend their LAN across multiple sites securely. This feature enhances connectivity and collaboration between geographically distributed offices while maintaining a secure network environment.
43. Explain the concept of Threat Emulation in Cyberoam.
Ans:
Threat Emulation in Cyberoam involves simulating the execution of potentially malicious files in a controlled environment. By observing the behavior of these files, Cyberoam can detect and block unknown threats that may evade traditional security measures.
44. What is the purpose of Network Behavior Analysis in Cyberoam?
Ans:
- Cyberoam’s Network Behavior Analysis monitors and analyzes patterns of network traffic to detect abnormal behavior indicative of a security threat.
- This proactive approach helps in identifying and mitigating potential security incidents before they escalate.
45. How does Cyberoam support Virtual Security Appliances?
Ans:
Cyberoam offers Virtual Security Appliances, allowing organizations to deploy security measures in virtualized environments. This ensures that virtualized infrastructure is as secure as physical infrastructure, addressing the unique security challenges of virtualization.
46. Explain the concept of Threat Intelligence Feeds in Cyberoam.
Ans:
- Cyberoam integrates Threat Intelligence Feeds to continuously update its database with information on the latest threats.
- This real-time threat intelligence enhances the effectiveness of Cyberoam’s security measures against emerging cyber threats.
47. What is the role of Application Visibility and Control in Cyberoam?
Ans:
Cyberoam’s Application Visibility and Control provide insights into the applications running on the network. Administrators can use this information to enforce policies that regulate the use of specific applications, enhancing security and network performance.
48. How does Cyberoam contribute to Security Information Sharing?
Ans:
Cyberoam promotes Security Information Sharing by enabling the exchange of threat intelligence data between security devices. This collaborative approach enhances the overall security posture by leveraging shared insights and intelligence.
49. What is the significance of Stateful Inspection in Cyberoam?
Ans:
- Cyberoam employs Stateful Inspection to monitor the state of active connections and make decisions based on the context of the traffic.
- This deep packet inspection method enhances the accuracy of threat detection and improves overall network security.
50. How does Cyberoam address the challenge of Ransomware?
Ans:
Cyberoam employs anti-ransomware measures, including behavior analysis and signature-based detection, to identify and block ransomware threats. By proactively preventing ransomware attacks, Cyberoam helps organizations safeguard their data and prevent financial losses.
51. Explain the role of Machine Learning in Cyberoam’s security approach.
Ans:
- Cyberoam utilizes Machine Learning to analyze patterns, detect anomalies, and identify potential security threats.
- This adaptive approach enhances the accuracy of threat detection, allowing Cyberoam to stay ahead of evolving cyber threats.
52. How does Cyberoam handle Dynamic IP Address Management?
Ans:
- Cyberoam supports Dynamic IP Address Management by allowing organizations to efficiently allocate and manage IP addresses.
- This flexibility in IP address management ensures optimal network performance and resource utilization.
53. What is the purpose of Anti-Phishing measures in Cyberoam?
Ans:
Cyberoam’s Anti-Phishing measures identify and block phishing attempts, protecting users from deceptive websites and email attacks. This helps in preventing the theft of sensitive information and ensures a secure online experience.
54. Explain the concept of Threat Intelligence Integration in Cyberoam.
Ans:
Cyberoam integrates Threat Intelligence from various sources to enhance its understanding of the threat landscape. This integration ensures that Cyberoam is well-informed about the latest threats, allowing for more effective threat detection and prevention.
55. How does Cyberoam handle Security Policy Versioning?
Ans:
- Cyberoam supports Security Policy Versioning, allowing administrators to manage and track changes to security policies over time.
- This feature enhances accountability and makes it easier to revert to previous configurations if needed.
56. What is the role of File Type Filtering in Cyberoam?
Ans:
Cyberoam’s File Type Filtering allows administrators to control the types of files that can be uploaded or downloaded from the network. This adds an extra layer of security by preventing the transfer of potentially malicious or unauthorized file types.
57. Describe the idea behind Cyberoam’s Threat Intelligence Sharing Communities.
Ans:
In order to facilitate collaboration and the exchange of threat intelligence data with the larger cybersecurity community, Cyberoam promotes involvement in Threat Intelligence Sharing Communities. The cybersecurity ecosystem as a whole is improved by this coordinated effort.
58. What does Cyberoam’s Security Incident Response aim to achieve?
Ans:
By offering resources and processes for looking into and handling security events, Cyberoam makes Security Incident Response easier. This guarantees that dealing and mitigating security breaches will be done in a methodical and coordinated manner.
59. How does Cyberoam support Customizable Alerts and Notifications?
Ans:
Cyberoam allows administrators to configure customized alerts and notifications based on specific security events. This proactive approach ensures that administrators are promptly informed of potential security incidents, enabling quick response and mitigation.
60. How does Cyberoam handle Security Policy Orchestration?
Ans:
- Cyberoam supports Security Policy Orchestration, allowing administrators to automate and streamline the management of security policies across the network.
- This automation ensures consistency and reduces the likelihood of human errors in policy configurations.
61. Explain the concept of Security Policy Compliance in Cyberoam.
Ans:
Cyberoam’s Security Policy Compliance features assess and ensure that security policies align with regulatory requirements and industry standards. This helps organizations maintain a compliant and secure network environment.
62. What is the purpose of Threat Intelligence Correlation in Cyberoam?
Ans:
- Cyberoam employs Threat Intelligence Correlation to analyze and correlate information from multiple threat intelligence sources.
- This integrated approach enhances the accuracy of threat detection and provides a more comprehensive understanding of the threat landscape.
63. How does Cyberoam handle Security Policy Change Tracking?
Ans:
- Cyberoam’s Security Policy Change Tracking records and monitors changes made to security policies.
- This feature enhances visibility into policy modifications, allowing administrators to track and audit changes for security and compliance purposes.
64. What role does URL Filtering play in Cyberoam?
Ans:
Cyberoam’s URL Filtering allows administrators to control and monitor access to websites based on predefined categories. This adds an extra layer of security by preventing access to malicious or inappropriate websites and ensuring a productive online environment.
65. How does Cyberoam address the challenge of Man-in-the-Middle (MitM) attacks?
Ans:
Cyberoam employs encryption and certificate validation mechanisms to detect and prevent Man-in-the-Middle attacks. By ensuring the integrity of encrypted communications, Cyberoam safeguards against unauthorized interception and tampering.
67. Explain the concept of Security Analytics in Cyberoam.
Ans:
- Cyberoam’s Security Analytics involves the analysis of security data and logs to extract meaningful insights into network activities and potential security threats.
- This proactive approach enhances the ability to detect and respond to security incidents effectively.
68. What is the purpose of Advanced Threat Protection in Cyberoam?
Ans:
Cyberoam’s Advanced Threat Protection features go beyond traditional security measures to detect and mitigate sophisticated and evolving cyber threats. This includes advanced malware, zero-day exploits, and other high-risk threats.
69. How does Cyberoam handle Security Policy Granularity?
Ans:
- Cyberoam provides granular control over security policies, allowing administrators to define policies based on specific criteria such as user roles, applications, and content types.
- This fine-tuned approach ensures that security measures align with organizational requirements.
70. Explain the concept of Cloud Application Security Broker (CASB) integration in Cyberoam.
Ans:
Cyberoam integrates with CASB solutions to extend security controls to cloud applications. This integration ensures that organizations maintain consistent security policies across on-premises and cloud environments.
71. What is the significance of Threat Hunting in Cyberoam’s security strategy?
Ans:
Cyberoam’s Threat Hunting strategy involves actively searching for indicators of compromise and potential security threats within the network. This proactive approach enhances the overall security posture by identifying and mitigating threats before they escalate.
72. How does Cyberoam handle Security Policy Simulation?
Ans:
Cyberoam supports Security Policy Simulation, allowing administrators to simulate the impact of proposed security policy changes before implementation. This helps in assessing the potential consequences and ensuring that changes align with security objectives.
73. Explain the concept of Security Automation in Cyberoam.
Ans:
- Cyberoam incorporates Security Automation to automate routine security tasks and responses.
- This reduces the time to detect and respond to security incidents, improving overall security efficiency.
74. What is the purpose of Security Policy Enforcement in Cyberoam?
Ans:
Cyberoam’s Security Policy Enforcement ensures that defined security policies are actively applied and enforced throughout the network. This proactive measure helps in maintaining a consistent and robust security posture.
75. How does Cyberoam handle Security Policy Optimization?
Ans:
- Cyberoam supports Security Policy Optimization, allowing administrators to fine-tune security policies for optimal performance and effectiveness.
- This ensures that security measures are aligned with the evolving needs of the organization.
76. What role does Behavioral Analysis play in Cyberoam’s threat detection?
Ans:
- Cyberoam employs Behavioral Analysis to monitor and analyze patterns of user and network behavior.
- This proactive approach enhances the ability to detect anomalies and potential security threats based on deviations from normal behavior.
77. What is the primary purpose of Cyberoam in a network security context?
Ans:
Cyberoam serves as a comprehensive network security solution, encompassing features such as firewall, VPN, anti-virus, and content filtering. It aims to safeguard networks from various cyber threats, ensuring a secure computing environment.
78. How does Cyberoam’s firewall contribute to network security?
Ans:
- Cyberoam’s firewall acts as a protective barrier between trusted internal networks and untrusted external networks.
- It monitors and controls incoming and outgoing traffic, enforcing access policies and preventing unauthorized access to enhance overall security.
79. Can you explain the role of VPN in Cyberoam?
Ans:
Cyberoam’s VPN (Virtual Private Network) functionality enables secure communication over the internet. It establishes encrypted connections, ensuring data confidentiality and integrity, making it crucial for secure remote access and site-to-site connectivity.
80. What measures does Cyberoam employ for content filtering?
Ans:
Cyberoam employs content filtering to regulate internet usage by categorizing websites and blocking inappropriate content. This feature enables administrators to create policies, controlling access and ensuring a secure online environment.
81. How does Cyberoam address the challenge of spam in email communication?
Ans:
Cyberoam tackles spam through anti-spam mechanisms like content analysis and blacklisting. It filters out unwanted emails, ensuring that users receive only legitimate and safe communications while protecting against potential security threats.
82. Explain the significance of intrusion prevention in Cyberoam.
Ans:
Intrusion Prevention in Cyberoam involves monitoring and blocking network-based attacks. By proactively identifying and preventing security threats, it adds an extra layer of defense, safeguarding the network from potential exploits and vulnerabilities.
83. What authentication methods does Cyberoam support for user verification?
Ans:
- Cyberoam supports multiple authentication methods, including username/password, digital certificates, and two-factor authentication.
- This diverse range enhances user verification, ensuring that only authorized individuals gain access to the network.
84. How does Cyberoam handle bandwidth management?
Ans:
Cyberoam’s Bandwidth Management allows administrators to allocate and control bandwidth usage for different applications and users. This ensures optimal network performance, prevents abuse, and facilitates fair resource distribution.
85. What part does Cyberoam’s Web Application Firewall (WAF) play?
Ans:
- Web applications are shielded from a variety of threats by Cyberoam’s WAF, including SQL injection and cross-site scripting.
- It improves overall online security by functioning as a barrier between web apps and the internet, stopping unwanted access.
86. What kind of network traffic recording does Cyberoam use?
Ans:
Cyberoam keeps thorough records of all network activity, including security incidents and user activity. Administrators may view network activity using these logs, which helps with analyzing and responding to security problems.
87. What is the purpose of High Availability in Cyberoam?
Ans:
- High Availability in Cyberoam ensures uninterrupted network operation by deploying redundant systems.
- This backup system takes over seamlessly in case of failures, minimizing downtime and ensuring continuous availability of network services.
88. How does Cyberoam support centralized management?
Ans:
Cyberoam offers centralized management through tools like Cyberoam Central Console (CCC). This allows administrators to efficiently manage multiple Cyberoam devices from a single console, streamlining configuration and monitoring tasks.
89. What is the concept behind Identity-based Security in Cyberoam?
Ans:
Identity-based Security in Cyberoam associates security policies with specific user identities rather than IP addresses. This approach allows for more personalized and granular security controls based on individual user profiles.
90. How does Cyberoam address the challenge of application control?
Ans:
- Cyberoam’s application control feature enables administrators to regulate and monitor the use of specific applications within the network.
- This helps in mitigating security risks and ensuring responsible use of network resources.






