Identity and Access Management (IAM) is a framework of policies and technologies ensuring that the right individuals have the appropriate access to technology resources. It encompasses the processes of identifying, authenticating, and authorizing users to access applications, systems, or networks based on predefined rules. IAM solutions provide centralized control and visibility over user identities and access permissions, enhancing security and compliance by preventing unauthorized access and mitigating risks associated with identity theft or data breaches.
1. What’s Identity and Access Management( IAM) and why is it important?
Ans:
Identity and Access Management( IAM) is the frame of business processes, programs, and technologies that facilitates operation of electronic or digital individualities. With an IAM frame in place, IT directors can ensure that users have access to the technology resources they need to be productive. Security It helps secure an association by ensuring that only authorized individualities can pierce sensitive systems and data.
2. What are the pivotal factors of IAM systems?
Ans:
- Identity repository This is where users credentials and attributes are stored.
- It could be an LDAP directory, a SQL database, or indeed a pall- predicated storage result.
- Access Management This involves authenticating users and authorizing their access to certain resources predicated on predefined programs.
- Single subscribe- On( SSO) SSO lets users authenticate formerly and gain access to multiple systems without demanding to log in again.
3. Difference between authentication and authorization in IAM?
Ans:
| Feature | Authentication | Authorization |
|---|---|---|
| Definition | Verifying the identity of a user | Granting or denying user permissions |
| Purpose | To ensure the user is who they claim to be | To determine what resources the user can access |
| Process | Involves checking credentials like passwords, biometrics, or tokens | Involves setting and enforcing policies or access controls |
| When it occurs | Happens before authorization | Happens after authentication |
4. How does part-predicated Access Control( RBAC) enhance organizational security?
Ans:
part- predicated Access Control( RBAC) enhances organizational security by administering strict programs on what resources users can pierce predicated on their part within the association. It simplifies the operation of users clearances, reduces the trouble of unauthorized access, and ensures that users only have access to the information necessary for their job functions.
5. What are some common challenges in administering an IAM system?
Ans:
- Complexity IAM systems can be complex to design and apply, particularly in large, different associations with multitudinous users and systems.
- Integration Integrating IAM results with IT structure and third- party services can be delicate, if heritage systems are involved.
- users Experience Balancing security measures with users convenience is a constant challenge.
- Excessively strict security protocols may be hamper productivity or lead to users frustration.
6. Describe a situation whereMulti-Factor Authentication( MFA) is particularly useful.
Ans:
Multi-Factor Authentication( MFA) is particularly useful in the scripts where enhanced security is important. For case, in financial institutions managing largely sensitive data or any system accessible over internet, MFA can significantly reduce trouble of unauthorized access. Also, MFA is vital for guarding remote access to networks; as trend of working from home grows, ensuring secure connections to organizational networks is vital.
7. What is the purpose of Single subscribe-On( SSO) and how does it benefit an association?
Ans:
Single subscribe- On( SSO) is a users authentication service that permits users to use one set of login credentials(e.g., name and word) to pierce more operations. The main benefit of SSO is that it improves the users experience by reducing word fatigue from different users name and word combinations. It also decreases time spent dropping out watchwords for same identity across operations, thereby adding productivity.
8. How do Identity Federation and SSO differ?
Ans:
Identity Federation and Single subscribe- On( SSO) are both related to managing users individualities across different systems, but they serve different purposes. Identity Federation is primarily used in scripts where users individualities need to be portable across different organizational boundaries and systems without creating new accounts. This is particularly common in business- to- business( B2B) surroundings.
9. Describe part of Security Assertion Markup Language( SAML) in IAM?
Ans:
- Security Assertion Markup Language( SAML) is open standard that allows an identity providers( IdPs) to pass authorization credentials to service providers( SPs).
- What SAML does in the terrain of IAM is it enables web- predicated confederated single sign- on( SSO), which allows users to log in formerly and gain access to multiple systems withoutre- authenticating.
- SAML handles the exchange of the authentication and authorization data between the service provider and the identity provider, ensuring that users individualities are securely transferred across different systems.
10. What are the implications of IAM in cloud surroundings?
Ans:
IAM in pall surroundings is critically important as it addresses unique security challenges not always present in traditional on- demesne setups. In the pall, resources are dynamic and scalable, and thus IAM programs must adapt accordingly to control access to these resources efficiently. The implications include the necessity for robust authentication and authorization mechanisms, fine- grained access control, and comprehensive examination trails to ensure compliance and security.
11. Explain Privileged Access Management( PAM) and its significance in IAM.
Ans:
Privileged Access Management( PAM) focuses on monitoring and securing access to critical organizational resources and administrative accounts. The primary thing of PAM is to apply security programs that limit access rights for users with elevated boons, thereby reducing the trouble of breaches performing from these accounts being compromised. PAM is vital in preventing data breaches, as privileged accounts are constantly targeted by attackers due to their high position of access.
12. What is the difference between DAC and MAC in IAM?
Ans:
- Discretionary Access Control( DAC) and obligatory Access Control( MAC) are two different types of access control mechanisms used in managing clearances in an IAM terrain.
- DAC allows the owner of the resource to decide who can pierce that resource, giving them the discretion to set programs on an individual base.
- This strictness makes DAC suitable for lower strict surroundings but can lead to a lack of steady policy enforcement and accidental breaches if not managed precisely.
13. How does an IAM system help in reducing IT costs for an association?
Ans:
IAM systems streamline and automate multitudinous aspects of users operation, which can significantly reduce IT costs. By centralizing the identity operation process, associations can count redundancies and drop the need for manual intervention, which in turn reduces labor costs. IAM systems also reduce the costs associated with word resets, users provisioning, and compliance reporting.
14. What is the generality of least honor and how is it executed in IAM?
Ans:
The principle of least honor requires that users are granted the minimum position of access necessary to perform their job functions. In the terrain of IAM, this is executed through strict access control programs that limit users rights and clearances to the bare minimum demanded. By administering least honor, associations can significantly reduce the trouble of accidental or vicious abuse of sensitive data.
15. What is the impact of IAM on regulatory compliance?
Ans:
- IAM plays a critical part in helping associations act up with various nonsupervisory conditions analogous as GDPR, HIPAA, and SOX.
- By managing and logging all users access and authentication attempts, IAM systems give a clear trail of data access and manipulation, which is necessary for compliance checks.
- These systems also apply security programs that are demanded by these regulations, analogous as ensuring that only authorized individualities can pierce certain types of sensitive or particular data.
16. What is an effective strategy for managing identities in hybrid environments (on-premise and cloud)?
Ans:
Managing users individualities in a cold- thoroughbred terrain requires a harmonious and unified approach to ensure security across all systems. An effective strategy includes using a single identity for each users across all platforms, which can be achieved through identity confederation and single sign- on results. This not only improves users experience but also simplifies the operation of users individualities and access controls.
17. How does IAM handle identity lifecycle operation?
Ans:
IAM handles identity lifecycle operation by overseeing the entire span of a users’s identity from creation to elision. This process involves original identity verification, provisioning of access rights, regular review and updating of those rights as necessary, and eventually, deprovisioning of access upon termination of employment or a change in part. Automated workflows are constantly used to handle routine tasks analogous as users onboarding and offboarding, which ensures that access rights are granted and abandoned in a timely and secure manner.
18. What are some of the arising trends in IAM that IT professionals should be alive of?
Ans:
- One significant trend in IAM is the adding use of artificial intelligence and machine knowledge to enhance security measures and automate identity operation processes.
- These technologies help in detecting anomalous conduct and implicit risks by assaying patterns and users conditioning.
- Another trend is the handover of zero trust architectures, which operate on the principle that no users or device should be trusted by dereliction, anyhow of their position relative to the network border.
19. What part does IAM play in disaster recovery and business continuity planning?
Ans:
IAM is fundamental in disaster recovery and business continuity planning as it ensures that the right users have access to critical systems and data under all circumstances, including during a disaster. Effective IAM practices can grease quick recovery by maintaining a clear, auditable trail of access clearances and authentications, which is essential when systems need to be restored or when there is a need to switch to a provisory terrain.
20. How can IAM results help help bigwig risks?
Ans:
IAM results play a vital part in mollifying bigwig risks by administering strict access controls and covering users conditioning. By administering least honor access programs, associations can ensure that workers only have access to the resources necessary for their job functions, reducing the trouble of purposeful or accidental abuse of data. also, IAM systems constantly include users geste analytics features that descry abnormal access patterns or unauthorized attempts to pierce sensitive information.
21. Describe how a robust IAM policy accommodates changes in users places and arrears.
Ans:
A robust IAM policy is designed to roundly adjust access rights predicated on changes in users places and arrears. This severity is generally achieved through automated provisioning and deprovisioning processes that can contemporize users access rights as soon as a change in part or employment status is detected. This ensures continuous alignment between users boons and their current job conditions.
22. What challenges do associations face when administering IAM results across international surroundings?
Ans:
- Administering IAM results in international surroundings presents unique challenges, analogous as dealing with different nonsupervisory conditions, language walls, and varying technology morals across countries.
- Associations must ensure that their IAM systems act up with original data protection laws, which can vary significantly from one governance to another.
- Also, international IAM prosecutions must support multiple languages and accommodate different organizational societies and practices.
23. Explain the significance of identity governance in IAM and how it differs from access operation.
Ans:
Identity governance is a critical element of IAM that focuses on policy operation, compliance, and trouble assessment associated with users individualities and access clearances. While access operation deals with the technical aspects of granting and managing access, identity governance provides a strategic oversight and frame for how access should be controlled and checked. It involves defining and administering programs related to users registration, part description, access rights, compliance reporting, and how individualities are managed throughout their lifecycle.
24. How do IAM systems integrate with other security technologies?
Ans:
IAM systems constantly integrate with a wide range of security technologies to give comprehensive protection and streamlined security operations. For illustration, IAM systems can be integrated with security information and event operation( SIEM) systems to enhance monitoring capabilities and respond to security incidents more effectively. Integration with endpoint protection platforms helps apply access controls directly at the device position.
25. How do IAM systems handle the security risks associated with privileged accounts?
Ans:
- IAM systems specifically address the risks associated with privileged accounts through Privileged Access Management( PAM) results, which are designed to control and cover privileged users conditioning.
- These systems apply strong authentication styles and bear more strict verification processes for piercing sensitive systems or data.
- PAM results also constantly feature session monitoring and recording, which help in auditing and ensuring that privileged conduct are responsible and traceable.
26. What is identity confederation, and why is it important in a modern enterprise terrain?
Ans:
Identity confederation is a system of trust that allows associations to partake identity information across multiple IT systems and enterprises. It’s vital in modern enterprises because it facilitates indefectible collaboration and access between businesses and pall services without compromising security. By using morals like SAML, OpenID Connect, or OAuth, identity confederation provides a users with a single authentication memorial to pierce services across different systems.
27. How can IAM help achieve compliance with data insulation regulations analogous as GDPR or HIPAA?
Ans:
IAM is integral to compliance with data insulation regulations like GDPR and HIPAA by ensuring that only authorized labor force have access to sensitive data, and by furnishing mechanisms to cover users data insulation. IAM systems help apply programs that are aligned with these regulations, analogous as data minimization, where only the necessary data is entered and reused.
28. Discuss the significance ofmulti- factor authentication( MFA) in IAM.
Ans:
- Multi-factor authentication( MFA) is a security system that requires further than one system of authentication from independent orders of credentials to corroborate the users’s identity for a login or other trade.
- MFA is significant in IAM because it dramatically enhances security by adding layers of defense, making it more challenging for unauthorized parties to pierce a users’s bias or online accounts.
- Indeed if one factor( like a word) is compromised, unauthorized users still need to bypass fresh factors( analogous as a point or a mobile app law), which significantly reduces the liability of successful breaches.
29. Explain the generality of a” Zero Trust” security model in relation to IAM.
Ans:
The Zero Trust security model operates under the principle that no bone inside or outside the network is trusted by dereliction. In relation to IAM, Zero Trust enforces rigorous identity verification for every users and device trying to pierce resources on a private network, anyhow of their position. This approach utilizes IAM to continuously authenticate and authorize users predicated on multiple data points, including users identity, position, device health, and service or workload.
30. What are the swish practices for ensuring effective IAM policy enforcement?
Ans:
Effective IAM policy enforcement involves several swish practices, analogous as regular review and updating of access rights to reflect changes in places, continuous trouble assessments to identify and palliate implicit access- related risks, and comprehensive training and awareness programs to ensure all users understand their places and arrears in securing organizational means.
31. How does an IAM system grease secure third- party access?
Ans:
- IAM systems grease secure third- party access by administering strict controls and covering mechanisms adapted for external users.
- analogous systems constantly employ a separate identity repository or a confederated identity approach to manage third- party individualities distinctly from internal users.
- This insulation helps in administering specific access programs, including time- predicated and terrain-alive restrictions.
32. How does IAM contribute to enhancing the user experience?
Ans:
IAM significantly enhances the users experience by streamlining and securing access to resources across a variety of systems and operations. Through single sign- on( SSO) capabilities, users can pierce multiple operations with one set of credentials, reducing word fatigue and minimizing the time spent on login procedures. also, IAM systems offer tone- service capabilities that empower users to manage aspects of their own individualities, analogous as word resets and streamlining particular details, which decreases reliance on IT support and faves up resolution times.
33. What is the part of artificial intelligence( AI) and machine knowledge( ML) in modern IAM systems?
Ans:
AI and ML are increasingly vital in modern IAM systems, enhancing both security and functional effectiveness. These technologies are employed to descry and respond to anomalous behavior by assaying users exertion patterns and relating diversions that could indicate implicit security risks or breaches. AI- driven features can automate complex decision- making processes related to identity verification and access rights assignments predicated on formerly behavior, trouble assessments, and adaptive authentication processes.
34. How does IAM handle the challenge of managing individualities across different bias and platforms?
Ans:
- IAM systems address the challenge of managing individualities across different bias and platforms through comprehensive and adaptable fabrics that ensure harmonious operation of security programs.
- By employing centralized operation tools, IAM provides steady security controls across all bias and platforms, whether they are mobile bias, desktops, or pall- predicated services.
- Also, IAM results constantly incorporate device operation capabilities that assess the security posture of each device before allowing access to marketable resources.
35. What strategies should be employed to ensure the scalability of IAM systems?
Ans:
To ensure the scalability of IAM systems, associations should adopt flexible and modular architectures that can accommodate growing numbers of users, bias, and operations without declination in performance or security. This involves using pall- predicated IAM results that can roundly gauge resources according to demand. also, it’s important to apply morals- predicated protocols and open APIs to grease integration with new technologies and platforms as they are espoused.
36. Discuss the significance of examination trails in IAM and how they support compliance and security.
Ans:
Examination trails are vital in IAM as they give a detailed, inflexible record of all identity- related exertion, analogous as users authentication, authorization changes, and access requests. These logs are essential for monitoring and assaying how individualities are used and can be vital in detecting security incidents or breaches. From a compliance perspective, examination trails help associations demonstrate adherence to various nonsupervisory conditions by furnishing validation of proper access controls and data operation practices.
37. How do IAM systems contribute to cost reduction in associations?
Ans:
- IAM systems contribute significantly to bring reduction by streamlining and automating pivotal identity operation processes analogous as users provisioning, word operation, and access rights enforcement.
- This automation reduces the administrative burden on IT staff, allowing them to concentrate on farther strategic enterprise rather than manual account operation tasks.
- Also, effective IAM results minimize the trouble of security breaches, which can be extremely precious in terms of both financial impact and damage to character.
38. Explain the generality of” Identity as a Service”( IDaaS). How does it differ from traditional IAM results?
Ans:
“Identity as a Service”( IDaaS) is a pall- predicated service that manages individualities and access controls for users across various platforms and operations. Unlike traditional IAM results that are generally posted on- demesne and managed by an association’s IT department, IDaaS offers IAM functionalities as a service handed by a third- party dealer over the internet.
39. What are the challenges of administering an IAM result in a cold- thoroughbred IT terrain?
Ans:
Administering IAM in a cold- thoroughbred IT terrain poses several challenges, primarily related to the integration and harmonious operation of distant systems that live both on- demesne and in the pall. ensuring that security programs and access controls are slightly applied across all surroundings can be complex, especially when dealing with multiple platforms that may have their own unique security fabrics and morals.
40. How does IAM integrate with other security technologies like SIEM systems?
Ans:
- IAM systems constantly integrate with Security Information and Event Management( SIEM) systems to enhance organizational security by furnishing a holistic view of security- related data across multiple platforms.
- This integration allows SIEM systems to collect and anatomize log and event data generated by IAM tools, analogous as login attempts, access denials, and changes in users boons.
- By relating this information with other security data, SIEM tools can identify patterns that may indicate a security trouble or breach, enabling quicker discovery and response.
41. What are the pivotal considerations when choosing an IAM dealer or product?
Ans:
When concluding an IAM dealer or product, several pivotal considerations should be addressed to ensure the result meets the specific conditions of an association. First, harmony with being IT structure is vital to ensure indefectible integration and operation. Security features analogous as support formulti- factor authentication and robust encryption styles are essential to cover sensitive information.
42. How does IAM support remote pool operation?
Ans:
IAM plays a vital part in managing remote workforces by enabling secure and effective access to organizational resources from any position. pivotal IAM features that support remote workers include robust authentication mechanisms, analogous asmulti- factor authentication, which ensures that access requests are legit. Additionally, IAM solutions can facilitate seamless access management across various devices and platforms, enhancing user experience while maintaining security.
43. What methods are used to measure the effectiveness of an IAM program?
Ans:
Measuring the effectiveness of an IAM program involves several criteria and pointers that assess both functional effectiveness and security posture. pivotal performance pointers( KPIs) analogous as the time taken to provision and deprovision users accounts, the rate of successful versus failed logins, and the number of unauthorized access attempts are critical for assessing functional aspects.
44. What is an identity directory service?
Ans:
- An identity directory service is a centralized system that stores and manages identity information for users and entities within an organization. It supports authentication and authorization processes by maintaining a repository of user attributes, including usernames, passwords, and roles.
- This service allows organizations to implement access control policies, simplify user management, and enhance security measures. Identity directory services can utilize various protocols, such as LDAP (Lightweight Directory Access Protocol) and Active Directory.
45. What is the definition of cryptography?
Ans:
Cryptography is the discipline that focuses on securing communication and information by converting it into a form that is inaccessible to unauthorized individuals. It employs algorithms and keys to encrypt and decrypt data, ensuring confidentiality, integrity, and authenticity. Cryptography is crucial for various purposes, including secure communications, digital signatures, and data protection.
46. Describe the challenges and results for IAM in amulti- pall terrain.
Ans:
Managing IAM in amulti- pall terrain presents unique challenges, primarily due to the complexity of operating across different platforms with potentially varying security models and capabilities. One of the main issues is ensuring harmonious identity and access programs across all pall surroundings, which requires a centralized operation approach.
47. What is a key management system?
Ans:
- Definition: A Key Management System (KMS) is a system designed to generate, store, manage, and securely distribute cryptographic keys throughout their entire lifecycle.
- Lifecycle Management: KMS oversees key processes, including generation, rotation, expiration, and deletion, ensuring keys are regularly updated to maintain their security.
- Compliance: It assists organizations in adhering to security standards and regulations by enforcing stringent access controls and providing audit capabilities for key usage.
48. What part does IAM play in disaster recovery planning?
Ans:
IAM is an integral part of disaster recovery planning because it ensures that access to critical systems and data can be snappily restored after a disturbance. A well- designed IAM system includes vittles for rapid-fire- firere- provisioning of access rights in a new or provisory terrain, which is vital when primary systems fail. Also, IAM helps maintain security during a disaster by ensuring that only authorized users can pierce sensitive systems and data, indeed in a compromised functional terrain.
49. What is the part of IAM in guarding systems from attacks?
Ans:
IAM plays a vital part in guarding systems from attacks by managing and securing users individualities and their access to resources. By ensuring that only authorized users can pierce certain data or systems, IAM reduces the trouble of vicious access and data breaches. It employs strong authentication mechanisms, enforces access programs, and spectators and logs access events for any suspicious exertion.
50. How does IAM work to cover against attacks?
Ans:
IAM protects against attacks by controlling who can pierce what resources within an association and under what conditions. It uses various security controls analogous asmulti- factor authentication( MFA), part- predicated access control( RBAC), and particularity- predicated access control( ABAC) to corroborate and validate the individualities of users requesting access to resources. IAM systems also continuously cover for abnormal access patterns or conduct that might indicate a implicit security trouble, enabling timely intervention to help or palliate attacks.
51. What is the difference between authentication, authorisation, and account in IAM?
Ans:
- In IAM, authentication verifies a users’s identity to ensure they are who they claim to be, generally through watchwords, biometrics, or security commemoratives.
- Authorization occurs after authentication and determines the resources and operations the users is permitted to pierce predicated on predefined programs.
- Account, on the other hand, involves shadowing and recording users conditioning for auditing and compliance purposes.
52. What are some standard styles of authentication used in IAM?
Ans:
Standard styles of authentication used in IAM include word- predicated authentication, biometric authentication, and token- predicated authentication systems. watchwords are the most common form, though they constantly bear fresh security measures analogous as complexity conditions. Biometric authentication uses unique natural traits like fingerprints or facial recognition, offering a advanced security position.
53. What are the strengths of using account in IAM?
Ans:
The strengths of using account in IAM include enhanced security monitoring, bettered compliance with nonsupervisory morals, and better resource operation. By keeping detailed logs of users conditioning, account helps descry unauthorized access or anomalous behavior patterns, enabling rapid-fire- fire response to implicit security risks. It also supports compliance by furnishing examination trails that validate who entered what information and when, which is essential for meeting multitudinous nonsupervisory conditions.
54. What is the significance of access controls and the highest- position privileged groups?
Ans:
- Access controls are essential for guarding sensitive information from unauthorized access and ensuring that users only have the rights necessary to perform their job functions.
- The operation of the topmost- position privileged groups, analogous as system directors, is particularly critical because these accounts have the power to make significant changes to IT systems and access sensitive data.
- Strict controls and monitoring of these privileged accounts help help and reduce the trouble of bigwig risks or external attacks exploiting these high- position clearances.
55. What is a pivotal operation system?
Ans:
A pivotal operation system( KMS) is a tool or frame used for managing cryptographic keys in a secure manner throughout their lifecycle, including generation, distribution, storage, rotation, and elision. It ensures that encryption keys are defended against unauthorized access and abuse, thereby securing sensitive data that the keys cipher. Additionally, KMS facilitates compliance with security standards and regulatory requirements by enforcing strict access controls and audit capabilities.
56. What is Kerbs?
Ans:
Kerberos is a network authentication protocol designed to give strong authentication for client/ garçon operations by using secret- pivotal cryptography. Developed at the Massachusetts Institute of Technology( MIT), Kerberos uses tickets to allow bumps communicating over anon-secure network to prove their identity to one another in a secure manner.
57. Why are watchwords largely compressed and restated?
Ans:
- Watchwords are largely compressed and restated to cover sensitive users information and ensure data security.
- Compression reduces the size of the word data, making it hastily and further effective to exercise and store, while encryption transforms the word into a format that can’t be easily understood or used by anyone who intercepts it.
- This double process of compressing and cracking watchwords is critical in securing against unauthorized access and data breaches.
58. What are digital vestiges?
Ans:
Digital vestiges are any data or residuals left by digital processes, exertion, or dispatches that can be used to reconstruct or anatomize these conduct. In the terrain of cybersecurity and digital forensics, digital vestiges include lines, logs, cybersurfer histories, metadata, and indeed changes in train structures. These vestiges are vital for examinations as they give validation that can help track the source of cyber attacks, understand the behavior of vicious software, or corroborate the conduct taken by a users on a network.
59. What are time constraints in authorisation control?
Ans:
Time constraints in authorization control are security programs that circumscribe users access to resources predicated on specific time conditions. These constraints can limit access to sensitive data or systems to certain hours of the day or days of the week, aligning access clearances with business hours or periods of high alert. administering time constraints helps minimize the trouble of unauthorized access during off- hours and reduces the overall exposure of critical systems.
60. What is users access in authorisation control?
Ans:
User access in authorization control refers to the process by which a system determines what resources a user can access and what operations they can perform. This involves authenticating the user’s identity and authorizing access rights based on predefined roles or attributes. Effective user access control is critical for maintaining system security, ensuring that individuals have only the necessary permissions to perform their job functions, thereby adhering to the principle of least privilege and reducing the risk of data breaches.
61. How multitudinous logs are generated during system operations in authorisation control?
Ans:
- The number of logs generated during system operations in authorization control can vary considerably depending on the scale of the system, the number of users, the complexity of the operations, and the position of auditing enabled.
- Each login attempt, access request, and system response might be logged, creating a substantial volume of data over time.
- These logs are critical for security as they give a record of all access deals and can be used to descry unauthorized access, understand users geste, and aid in compliance with nonsupervisory conditions.
62. What are the risks associated with single- factor authentication?
Ans:
Single- factor authentication, which generally involves only a word, poses several risks due to its reliance on one form of evidence. This system is vulnerable to a variety of attacks, including phishing, brute force, and social engineering, where an attacker only needs to know or guess the word to gain access. Single- factor authentication does not give sufficient protection in surroundings where security is critical, as compromised watchwords can lead to unauthorized access and implicit data breaches.
63. What are the benefits ofmulti- factor authentication?
Ans:
Multi-factor authentication( MFA) significantly enhances security by taking users to give two or farther verification factors to gain access to a resource, analogous as a system, operation, or data. This system reduces the trouble of unauthorized access, as compromising multiple authentication factors is extensively more delicate for attackers compared to single- factor styles, generally just a word.
64. How can word exposure be eased inmulti- factor authentication?
Ans:
- Word exposure inmulti- factor authentication can be eased by using fresh factors that do not calculate on shared secrets, analogous as watchwords.
- administering biometric verification( like fingerprints or facial recognition), attack commemoratives, or push adverts to a trusted device are effective styles.
- These styles ensure that indeed if a word is compromised, unauthorized users can’t gain access without the fresh authentication factor.
65. What is the critical object or service inmulti- factor authentication?
Ans:
The critical object or service inmulti- factor authentication is the authentication garçon or service that verifies the multiple factors handed by the users. This garçon acts as the central point where all the different authentication styles meet and are validated. It manages the authentication protocols, verifies the legitimacy of the authentication factors, and ensures that each element of the MFA setup communicates securely.
66. What is the insulation of duties, and why is it essential in authorisation?
Ans:
Insulation of duties( SoD) is a fundamental control in both financial and IT operations that prevents a single existent from executing two or further nonconcurring sensitive tasks. In authorization, SoD is vital because it helps help fraud, crimes, and abuse of boons. By taking that no single existent has complete control over critical processes, SoD reduces the trouble of vicious exertion going undetected.
67. What is the principle of least honor, and how is it applied in authorisation?
Ans:
The principle of least honor( PoLP) requires that users and processes are granted only those access rights essential for their legit purposes. In authorization, this principle is applied by assigning users rights and clearances that are strictly necessary for the performance of their job or function. This minimizes the attack face by limiting access to information and resources, reducing the implicit damage from accidents, crimes, or unauthorized use.
68. What is a advertisement of system operation in a marketable terrain?
Ans:
- A advertisement of system operation in a marketable terrain is a communication or alert that informs users of their scores and arrears when using organizational IT resources.
- This generally includes monuments about the respectable use policy, insulation considerations, and security protocols. The advertisement might appear upon login, detailing the monitoring practices and the consequences of policy violations.
- This practice helps support security awareness among users, ensures compliance with marketable programs, and serves as a legal safeguard by informing users that their exertion may be covered and recorded.
69. What are the four types of access control?
Ans:
The four primary types of access control are obligatory Access Control( MAC), Discretionary Access Control( DAC), part- predicated Access Control( RBAC), and trait- predicated Access Control( ABAC). MAC restricts access predicated on fixed security attributes determined by a central authority. DAC allows users to control access to their own resources, generally executed at the train system position. RBAC assigns clearances predicated on places within an association, simplifying the administration of security clearances.
70. What is obligatory access control?
Ans:
Obligatory Access Control( MAC) is a strict access control model that enforces security programs predicated on information concurrence and groups. Under MAC, access rights are assigned predicated on regulations set by a central authority and can’t be altered by users. The system defines what resources or data users can pierce predicated on their security concurrence, and every resource has a type marker.
71. What is voluntary access control?
Ans:
- Discretionary Access Control( DAC) is an access control model where the access rights to resources are decided by the resource owner or by the users who have control over the resources.
- This control type is predicated on the identity of the users and/ or group registrations.
- In a DAC model, the owner of the resource can grant or circumscribe access to others as they see fit, making it more flexible but potentially less secure than MAC, as it can lead to misconfigurations or security breaches if users do not manage clearances precisely.
72. What is part- predicated access control?
Ans:
part- predicated Access Control( RBAC) is a system of confining system access to authorized users predicated on their places within an association. In RBAC, clearances to perform certain operations are assigned to specific places, and users are assigned places predicated on their arrears and qualifications. This approach simplifies operation and ensures that users only have access to the information necessary to perform their duties, reducing the trouble of accidental or vicious access to sensitive data.
73. What is provisioning?
Ans:
Provisioning in the terrain of IAM refers to the process of setting up and managing accounts and access rights for users within an information system. This process includes creating, streamlining, and deleting users accounts along with configuring their access clearances to various resources predicated on predefined programs, constantly corresponding to the users’s part in the association.
74. How is access termination necessary?
Ans:
- Access termination is a critical element of identity and access operation that involves killing a users’s access rights when they are no longer authorized to use specific systems or data.
- This could be due to a number of reasons analogous as employment termination, a change in part, or the end of a contract.
- Timely access termination is necessary to cover sensitive information and maintain security by ensuring that only current, authorized users have access to organizational resources.
75. What happens to a users regard when it’s deleted?
Ans:
When a users regard is deleted in an IAM system, it’s generally removed from the active directory or database, and the users loses access to any systems or data linked to that account. This process is vital to maintaining security and ensuring that only current authorized users have access to sensitive resources. Before elision, a backup or library of the users’s data may be created for compliance and examination purposes.
76. How long should logs be kept for exploration purposes?
Ans:
When a users regard is deleted in an IAM system, it’s generally removed from the active directory or database, and the users loses access to any systems or data linked to that account. This process is vital to maintaining security and ensuring that only current authorized users have access to sensitive resources. Before elision, a backup or library of the users’s data may be created for compliance and examination purposes.
77. What is the life cycle of IDAM?
Ans:
- The life cycle of Identity and Access Management( IDAM) includes several pivotal phases identification, authentication, authorization, and operation.
- Identification involves recognizing a users within a system.
- Authentication verifies a users’s identity using credentials.
- Authorization grants or denies users access to resources predicated on programs.
- operation involves maintaining and covering these individualities and access boons over time, ensuring delicacy and compliance with programs.
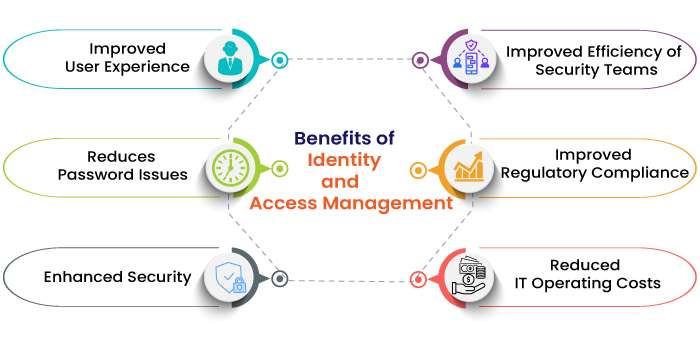
78. What are the benefits of IDAM?
Ans:
Identity and Access Management( IDAM) offers multiple benefits it enhances security by ensuring that only authorized individualities can pierce resources, reducing the trouble of data breaches. It improves users witness through streamlined login processes like single sign- on, reducing word fatigue. IDAM also increases effectiveness by automating tasks analogous as users provisioning and deprovisioning.
79. What is the confederation generality in IDAM?
Ans:
The confederation in Identity and Access Management( IDAM) refers to the practice of linking and managing individualities across multiple systems or associations to simplify access operation and enhance security. This approach allows users to authenticate their identity formerly( single sign- on) and gain access to resources across different systems without demanding to log in singly to each one.
80. What is the firewall generality, and how does it process rules?
Ans:
- A firewall is a network security device that monitors incoming and gregarious network business and decides whether to allow or block specific business predicated on a defined set of security rules.
- Firewalls can be attack- predicated, software- predicated, or a combination of both.
- These rules are vital for guarding networks from unauthorized access and risks analogous as contagions and worms.
- Firewalls work by examining data packets and determining whether they meet the criteria set in the rules, analogous as allowed IP addresses, harborage numbers, and protocols.
81. What is spamming?
Ans:
Spamming refers to the practice of transferring unsolicited dispatches, particularly advertising, in large quantities and constantly, across a network. generally, spam is transferred via dispatch, but it can also do through other digital communication means analogous as instant messaging, social media, and mobile handbooks. Spam dispatches are not only annoying for users but can also involve scams and vicious links leading to malware installation, phishing attacks, or other security breaches.
82. What is spyware?
Ans:
Spyware is a type of vicious software that is installed on a computer without the users’s knowledge and is designed to collect particular information, monitor users conditioning, and potentially control the computer’s operation. Spyware can capture a wide range of data, from internet browsing habits to keystrokes, and can also include functionality to block emails and instant dispatches. It’s constantly used for financial theft, identity theft, or targeted marketable espionage.
83. What is dumpster diving?
Ans:
- Dumpster diving refers to the practice of sifting through marketable or domestic trash to find particulars that can be used, repurposed, or sold.
- In the terrain of information security, it involves searching through a company’s scrap to find sensitive information that has been discarded erroneously.
- This can include documents with particular information, business records, or any data that can be used in fraudulent exertion or identity theft.
84. What is Netcraft?
Ans:
Netcraft is an internet services company predicated in the United Kingdom that provides cybercrime disturbance and a range of security services including phishing discovery, operation testing, and automated penetration testing. also, Netcraft offers a well- known cybersurfer extension that helps users descry and avoid vicious websites by furnishing data on the spots they visit, including point age, hosting country, and trouble conditions.
85. What IAM tools are most comfortable using and why?
Ans:
The IAM tools most comfortable using include AWS IAM, Microsoft Azure Active Directory, and Okta, mainly due to their comprehensive features and wide handover in the sedulity. AWS IAM offers detailed and coarse access controls for AWS resources, making it ideal for managing large- scale pall surroundings. Azure Active Directory provides excellent integration with other Microsoft services, which is salutary in surroundings heavily using Microsoft products.
86. Explain the difference between an IAM policy and an IAM policy document?
Ans:
An IAM policy is a broader term that refers to a medium for specifying authorization, which can be attached to users, groups, or places in an IAM system. It defines clearances and can be managed as individual objects within IAM. An IAM policy document, on the other hand, is the JSON format representation of the policy itself, which details the specific clearances granted. This document states the conduct that are allowed or denied, the resources to which these conduct apply, and conditions under which the clearances are valid.
87. Explain the process of setting upcross- account access using IAM places?
Ans:
- Setting upcross- account access using IAM places involves creating a part within one AWS account( the trusting account) and allowing another account( the trusted account) to assume this part.
- This part includes clearances that specify what conduct are allowed and on which resources.
- The trusting account creates a part and attaches a policy that defines the allowed conduct from the trusted account. The trusted account also needs to produce a policy that allows it to assume the previously created part.
88. What is IAM access pivotal rotation, and why is it important for security?
Ans:
IAM access pivotal rotation refers to the practice of regularly changing the access keys used to interact with pall services securely. This is an essential security practice that minimizes the trouble of an access key being compromised. Regularly rotating keys ensures that indeed if a key is ever blurted or stolen, its useful life is limited, thereby reducing the implicit damage.
89. What is IAM policy evaluation, and how does it determine action permissions?
Ans:
IAM policy evaluation sense is a regular approach used by IAM systems to determine whether to allow or deny a particular request. The process starts by assessing all applicable programs( identity- predicated programs, resource- predicated programs,etc.) and collecting all the allow and denystatements.However,” the action is denied, If there is an unambiguous”deny.However,” the action is permitted, If there is no” deny” but an unambiguous”allow.
90. Explain the “ condition ” element in IAM programs and give an illustration use case?
Ans:
The” condition” element in IAM programs allows specifying conditions under which a policy grants or denies authorization. This element adds a caste of security by ensuring that clearances are not just predicated on” who” but also predicated on” under what circumstances.” For illustration, a condition might circumscribe access to a resource only if the request comes from a specific IP range or during certain times of the day. A practical use case could be allowing access to a sensitive database






