
SailPoint is critical in assisting organizations in managing the intricacies of identification and access management. SailPoint’s solutions provide a comprehensive and integrated approach to identity governance, offering the tools needed to secure digital identities, enforce access controls, and maintain compliance in today’s dynamic and interconnected IT environments, whether in the cloud with IdentityNow or on-premise with IdentityIQ. The company’s emphasis on automation, integration, and analytics reflects the changing environment of identity management, where proactive and intelligent solutions are required to maintain a robust and secure infrastructure.
1. What is the purpose of Identity and Access Management (IAM)?
Ans:
Identity and Access Management (IAM) is crucial for ensuring secure and efficient access to resources within an organization. It involves managing user identities, roles, and permissions to control access to sensitive data and systems. IAM solutions like SailPoint play a pivotal role in enforcing policies, minimizing security risks, and maintaining compliance.
2. How does SailPoint handle identity governance?
Ans:
- SailPoint excels in identity governance by providing a comprehensive platform to manage the complete identity lifecycle.
- It orchestrates processes related to onboarding, offboarding, and access reviews.
- Automated workflows and policy enforcement ensure compliance, reducing the risk of security breaches and improving operational efficiency.
3. Discuss the role of IdentityNow in managing user identities.
Ans:
IdentityNow is SailPoint’s identity management platform that centralizes user identities. It offers a user-friendly interface for identity administration, allowing organizations to efficiently manage user access, roles, and entitlements. IdentityNow also provides self-service capabilities, empowering users to handle routine tasks like password resets, reducing administrative burdens.
4. How does SailPoint handle identity governance?
Ans:
SailPoint excels in identity governance by providing a comprehensive platform to manage the complete identity lifecycle. It orchestrates processes related to onboarding, offboarding, and access reviews. Automated workflows and policy enforcement ensure compliance, reducing the risk of security breaches and improving operational efficiency.
5. What role does the IdentityNow Connector play in SailPoint’s architecture?
Ans:
- The IdentityNow Connector is a crucial component in SailPoint’s architecture, facilitating integration with various applications and systems.
- It acts as a bridge between the IdentityNow platform and target systems, allowing seamless data exchange.
- This connector framework enables SailPoint to support a wide range of applications.
6. Examine the significance of Attribute-Based Access Control (ABAC) in SailPoint.
Ans:
SailPoint incorporates ABAC to grant access based on specific attributes associated with user identities. ABAC enhances granularity in access control, considering variables like user roles, attributes, and environmental conditions. This approach provides a more dynamic and context-aware access control mechanism, contributing to a robust security posture.
7. How does SailPoint address the challenges of managing privileged accounts?
Ans:
- SailPoint tackles privileged account management challenges by implementing strict controls on elevated access.
- Through its platform, organizations can enforce segregation of duties, regularly review and certify privileged access.
- This ensures that only authorized individuals have access to critical systems and sensitive data.
8. Discuss the role of policy enforcement in SailPoint.
Ans:
SailPoint’s policy enforcement mechanisms help organizations maintain compliance and security standards. It involves defining policies related to access, password management, and data usage. SailPoint automates the enforcement of these policies, ensuring that users adhere to established rules and that any violations are promptly addressed.
9. What is the purpose of the IdentityNow Connector in SailPoint?
Ans:
- The IdentityNow Connector facilitates integration with various applications and systems.
- Acts as a bridge between the IdentityNow platform and target systems.
- Enables seamless data exchange and synchronization of identity information.
- Supports a wide range of applications, ensuring versatility in identity management.
10. Explain how SailPoint handles user onboarding and offboarding processes.
Ans:
SailPoint streamlines user onboarding and offboarding through automated workflows. During onboarding, it ensures that new users receive the appropriate access privileges swiftly. In offboarding, SailPoint automatically revokes access and initiates the deprovisioning process, reducing the risk of lingering access and enhancing security measures.
11. What is the purpose of IdentityNow’s Governance Platform in SailPoint?
Ans:
IdentityNow’s Governance Platform is the backbone of SailPoint’s identity governance solution. It provides a centralized hub for managing and governing identities across the enterprise. This platform streamlines tasks such as access certifications, policy enforcement, and reporting, offering a comprehensive solution for identity lifecycle management and compliance.
12. Explain the difference between roles and entitlements in SailPoint IdentityNow.
Ans:
| Aspect | Roles | Entitlements | |
| Definition |
Logical groupings of entitlements |
Specific access rights or permissions | |
| Purpose | Simplify access management at a higher level | Provide fine-grained control over individual permissions | |
| Composition | Composed of entitlements | Building blocks for roles | |
| Level of Abstraction |
Higher-level abstraction |
Lower-level, granular permissions |
13. What are the key components of SailPoint’s identity management architecture?
Ans:
SailPoint’s identity management architecture comprises key components like IdentityNow, Connectors, and Governance Platform. IdentityNow serves as the user interface and identity repository, Connectors enable integration, and the Governance Platform focuses on policy enforcement and compliance. This modular architecture ensures a scalable and flexible identity management solution.
14. How does SailPoint contribute to a Zero Trust security model?
Ans:
- Implements least privilege principles for access control.
- Enforces continuous monitoring and risk-based access controls.
- Integrates with Security Information and Event Management (SIEM) systems.
- Aligns with the principles of verifying and validating user identities.
- Strengthens security posture by adopting a proactive Zero Trust approach.
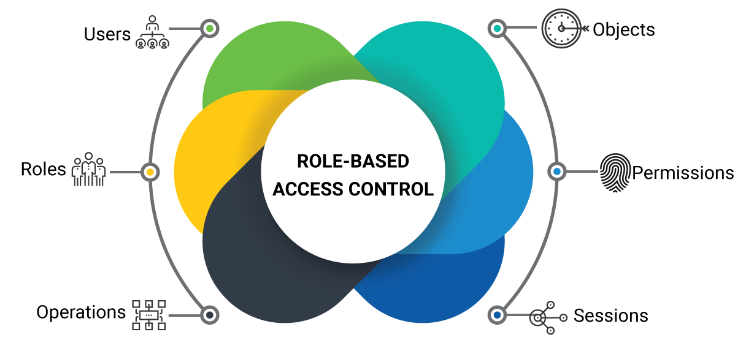
15. Explain the concept of Role-Based Access Control (RBAC) in SailPoint.
Ans:
SailPoint’s RBAC model assigns permissions based on predefined roles, streamlining access management. Users are assigned roles, and these roles determine their access rights. RBAC simplifies administration, enhances security, and ensures that users have the necessary access without unnecessary privileges, reducing the risk of unauthorized actions.
16. Explain the purpose of Attribute-Based Access Control (ABAC) in SailPoint.
Ans:
- Grants access based on specific attributes associated with user identities.
- Enhances granularity in access control by considering user roles and attributes.
- Provides a dynamic and context-aware access control mechanism.
- Supports a more flexible and adaptive access control strategy.
- Contributes to a robust security posture by aligning access with user attributes.
17. How does SailPoint handle identity reconciliation and data synchronization?
Ans:
SailPoint employs identity reconciliation to compare and synchronize identity data across systems. The platform ensures consistency by detecting and rectifying any discrepancies. By automating the reconciliation process, SailPoint minimizes errors, enhances data accuracy, and ensures that user identities are consistently and correctly represented across the organization. .
18. Discuss the role of AI and ML in SailPoint’s identity management.
Ans:
- Leverages AI and ML to analyze user behavior and detect anomalies.
- Enhances access decisions by continuously learning from user activities.
- Contributes to adaptive authentication and proactive risk mitigation.
- Improves the accuracy of access reviews through intelligent analysis.
- Ensures a more dynamic and responsive identity management system.
19. Examine the role of SailPoint in ensuring compliance with regulatory standards.
Ans:
SailPoint plays a vital role in compliance management by automating access certifications and enforcing policies. It helps organizations align with regulatory standards such as GDPR or SOX. Through continuous monitoring and reporting, SailPoint assists in demonstrating compliance, mitigating risks, and avoiding potential legal and financial consequences.
20. What is the significance of Access Certifications in SailPoint’s identity governance?
Ans:
- Involves periodic reviews of user entitlements to ensure compliance.
- Provides a systematic approach to verifying and validating access rights.
- Ensures alignment with business policies and regulatory standards.
- Automates the certification process for efficient and accurate reviews.
- Maintains a clear audit trail and helps demonstrate regulatory compliance.
21. How does SailPoint facilitate identity-based risk management?
Ans:
SailPoint’s risk management capabilities involve assessing and mitigating identity-related risks. The platform analyzes user entitlements and behaviors to identify potential security risks. Through risk-based access reviews and continuous monitoring, SailPoint helps organizations proactively address vulnerabilities and ensure a more secure identity landscape.
22. How does SailPoint handle the integration of identity governance with other security solutions?
Ans:
- Integrates seamlessly with Security Information and Event Management (SIEM) systems.
- Correlates identity-related events with broader security incidents.
- Provides a holistic view of potential threats through integration.
- Enhances overall security posture by collaborating with diverse security solutions.
- Supports a comprehensive and interconnected security ecosystem.
23. What is the purpose of IdentityNow’s Identity Configuration in SailPoint?
Ans:
IdentityNow’s Identity Configuration is the core of SailPoint’s identity management. It defines how identity data is ingested, transformed, and correlated. This configuration enables organizations to customize the handling of attributes, ensuring accurate representation of user identities. It’s crucial for tailoring SailPoint’s functionality to specific enterprise requirements.
24. Explain the concept of Just-In-Time (JIT) provisioning in SailPoint.
Ans:
- JIT provisioning dynamically grants access based on immediate needs.
- Evaluates contextual information to provide temporary access.
- Enhances agility by responding quickly to changing business requirements.
- Maintains granular control over user access during dynamic scenarios.
- Supports a flexible and adaptive approach to access provisioning.
25. Discuss the challenges associated with managing identities in a hybrid IT environment.
Ans:
Managing identities in a hybrid IT environment presents challenges due to diverse systems and cloud platforms. SailPoint addresses these challenges by offering robust connectors that enable seamless integration across on-premises and cloud applications. The platform ensures consistent identity governance, regardless of the IT infrastructure, enhancing overall security.
26. How does SailPoint handle multi-factor authentication (MFA) for enhanced security?
Ans:
- Integrates with various MFA solutions to enforce additional identity verification steps.
- Supports biometrics or one-time passcodes for enhanced authentication.
- Enhances authentication security beyond passwords.
- Reduces the risk of unauthorized access, especially to sensitive systems.
- Contributes to a layered security approach in identity management.
27. How does SailPoint ensure a secure and resilient password management system?
Ans:
SailPoint ensures secure password management by implementing policies for strong passwords and regular password rotations. It facilitates self-service password reset options for users, reducing the burden on IT support. Additionally, SailPoint employs encryption and secure storage mechanisms to safeguard password information, ensuring the confidentiality and integrity of authentication credentials.
28. Discuss the role of Predictive Identity in SailPoint and its impact on risk management.
Ans:
- Predictive Identity uses machine learning to analyze user behavior.
- Proactively identifies anomalies and emerging risks.
- Predicts access needs and potential security risks.
- Enhances risk management with adaptive and preemptive measures.
- Contributes to a more intelligent and responsive identity governance strategy.
29. Examine the role of SailPoint in managing access entitlements for non-human identities.
Ans:
SailPoint extends its identity management capabilities to non-human entities, including service accounts and automated processes. It ensures that access entitlements for these entities are properly defined, monitored, and audited. By managing non-human identities, SailPoint enhances security by reducing the risk associated with uncontrolled access and ensuring accountability for automated processes.
30. How does SailPoint handle the integration of identity governance with cloud-based infrastructure
Ans:
- Provides robust connectors for seamless integration with AWS and Azure.
- Ensures identity governance extends to cloud environments.
- Maintains consistent policies and controls in the cloud.
- Supports organizations transitioning to cloud-centric IT architectures.
- Upholds strong identity governance practices in cloud-based infrastructure.
31. Explain the concept of Attribute Aggregation in SailPoint and its significance.
Ans:
Attribute Aggregation in SailPoint involves gathering and consolidating identity attributes from various connected systems. This process ensures a unified view of user identities across the organization. Significantly, attribute aggregation forms the basis for effective identity governance, enabling consistent policy enforcement and access management.
32. Discuss the integration capabilities of SailPoint with Privileged Access Management (PAM) solutions.
Ans:
- Seamlessly integrates with Privileged Access Management solutions.
- Extends governance controls to privileged accounts.
- Ensures privileged access is subject to identity governance policies.
- Provides a unified approach to managing standard and privileged access.
- Enhances overall security and compliance in privileged identity management.
33. How does SailPoint address the challenge of managing access in a dynamic environment?
Ans:
SailPoint’s solution lies in its automated Access Review functionality. This feature enables organizations to periodically review and recertify user access, ensuring it aligns with current business needs. Through automated reviews, SailPoint streamlines the process, reducing the administrative burden associated with access management in a dynamic environment.
34. Explain the purpose and significance of SailPoint’s IdentityNow API.
Ans:
- IdentityNow API allows customization and integration of identity management processes.
- Facilitates the development of tailored solutions aligned with business requirements.
- Enhances extensibility, adapting SailPoint to unique workflows and integrations.
- Supports seamless interaction with other systems and applications.
35. Discuss the role of Policy Modeling in SailPoint.
Ans:
Policy Modeling in SailPoint allows organizations to simulate the impact of access policies before enforcement. It provides a proactive approach, identifying potential issues and conflicts. By modeling policies, organizations can refine their access governance strategy, ensuring a robust framework that minimizes risks and complies with regulatory requirements.
36. How does SailPoint ensure compliance with industry-specific regulations?
Ans:
- Utilizes the Compliance Manager to define and enforce policies.
- Aligns with industry-specific regulations like HIPAA or PCI DSS.
- Automates compliance controls to streamline audit processes.
- Demonstrates adherence to regulatory standards through continuous monitoring.
- Mitigates risks associated with non-compliance through proactive measures.
37. What is the purpose of a Risk Model in SailPoint?
Ans:
SailPoint’s Risk Model assesses and quantifies the risk associated with user access. By considering factors like entitlement sensitivity and user behavior, it prioritizes and highlights high-risk access. This information empowers organizations to focus their efforts on mitigating the most critical risks, enhancing the effectiveness of their identity governance program.
38. Discuss the significance of SailPoint’s Integration Modules in connecting with third-party applications
Ans:
- Integration Modules serve as connectors to third-party applications and systems.
- Streamline the integration process for seamless interaction.
- Ensure SailPoint can interact with a wide range of external platforms.
- Enhance the interoperability of the identity management solution.
39. Examine the role of the IdentityNow Mobile Application in SailPoint’s ecosystem.
Ans:
The IdentityNow Mobile Application extends SailPoint’s functionality to mobile devices, allowing users to manage their identities on the go. It provides a secure and user-friendly interface for tasks such as password resets and access requests. The mobile app enhances user convenience without compromising security, contributing to a seamless identity management experience.
40. Discuss the impact of IdentityNow Launchpad on user experience in SailPoint.
Ans:
- Automates the process of access recertification for efficiency.
- Requires periodic reviews to ensure access aligns with business needs.
- Reduces the risk of unauthorized access through systematic reviews.
- Maintains a secure access landscape by addressing potential vulnerabilities.
- Provides a proactive approach to security through continuous recertification.
41. How does SailPoint ensure compliance with industry-specific regulations?
Ans:
SailPoint addresses industry-specific compliance requirements through its Compliance Manager. This module enables organizations to define and enforce policies aligned with regulations like HIPAA or PCI DSS. By automating compliance controls, SailPoint helps organizations streamline audit processes and maintain adherence to industry standards.
42. Discuss the scalability features of SailPoint for small to medium-sized enterprises.
Ans:
SailPoint is designed to scale efficiently for small to medium-sized enterprises. Its modular architecture allows organizations to implement components based on their specific needs, ensuring a tailored and scalable identity management solution. Whether dealing with a growing user base or expanding IT requirements, SailPoint’s scalability features provide flexibility for smaller enterprises to evolve their identity governance capabilities.
43. Explain how SailPoint addresses the issue of “Access Creep”.
Ans:
Access Creep refers to the gradual accumulation of unnecessary access rights over time. SailPoint addresses this by regularly conducting access certification campaigns where data owners review and validate user access. To prevent access creep, organizations should implement policies that automatically revoke unused or unnecessary access, ensuring that users only have the access they genuinely need based on their roles.
44. In the context of SailPoint, what is “Role Mining”?
Ans:
- Role Mining in SailPoint involves analyzing user access patterns and creating roles based on observed access similarities.
- It contributes to the role definition process by identifying common access patterns across user groups, helping organizations create roles that accurately reflect job functions.
45. How does SailPoint facilitate integration with ticketing systems?
Ans:
SailPoint allows integration with ticketing systems to automate the resolution of access-related issues and streamline the identity governance process. When policy violations or access requests trigger tickets, integration ensures that remediation actions are taken promptly.
46. What role does “Behavior Analytics” play in SailPoint.
Ans:
Behavior Analytics in SailPoint involves analyzing user behavior patterns to detect anomalous activities that may indicate security risks. It contributes to risk mitigation by providing insights into user behavior deviations from normal patterns. By detecting potential security threats, organizations can take proactive measures to mitigate risks and ensure the integrity of their identity management environment.
47. Explain the concept of “Access Fulfillment” in SailPoint.
Ans:
Access Fulfillment in SailPoint involves the automated process of fulfilling user access requests by provisioning the necessary entitlements. It streamlines the access request and provisioning process by automating the fulfillment of approved access requests, reducing manual intervention, and ensuring timely access to resources.
48. Discuss the scalability features of SailPoint for large enterprises.
Ans:
SailPoint is designed with scalability in mind, making it suitable for large enterprises. It offers a modular architecture that allows organizations to scale components based on their needs. Whether dealing with a growing user base or expanding IT infrastructure, SailPoint’s scalability features ensure that identity management processes remain efficient and effective.
49. What role does Governance Automation play in SailPoint’s identity governance framework?
Ans:
- Governance Automation in SailPoint automates routine identity governance tasks, such as access certifications and policy enforcement.
- This accelerates processes, reduces manual effort, and ensures a proactive approach to identity governance.
- By automating repetitive tasks, organizations can maintain a high level of governance efficiency.
50. How does SailPoint handle the complexities of managing identities in a distributed organization?
Ans:
SailPoint’s solution lies in its Global Deployment capabilities. It supports the implementation of distributed identity governance processes across multiple locations. By providing a centralized view of identities and policies, SailPoint ensures consistency and compliance, overcoming the challenges associated with managing identities in geographically dispersed organizations.
51. Examine the role of the SailPoint IdentityNow Identity Warehouse in the overall architecture.
Ans:
The IdentityNow Identity Warehouse serves as the central repository for identity data in SailPoint’s architecture. It consolidates information from connected systems, creating a unified identity dataset. This warehouse is essential for providing a comprehensive view of user identities, enabling organizations to make informed decisions regarding access, roles, and policies.
52. Discuss the concept of Separation of Duties (SoD) in SailPoint
Ans:
- Separation of Duties in SailPoint involves preventing users from having conflicting access that could lead to security risks.
- It ensures that no single user has both the ability to request and approve access.
- By enforcing SoD policies, SailPoint enhances access governance, reducing the likelihood of unauthorized activities and complying with regulatory requirements.
53. What challenges does SailPoint address in managing identities in a DevOps environment?
Ans:
SailPoint adapts to DevOps environments by integrating with DevOps tools and providing a streamlined approach to managing identities in agile workflows. It addresses challenges such as rapid provisioning and deprovisioning of access for development teams. By aligning identity management with DevOps practices, SailPoint ensures security and compliance without impeding the speed of development processes.
54. How does SailPoint facilitate the automation of access request approvals?
Ans:
SailPoint automates access request approvals through configurable workflows. These workflows include multi-level approval processes and policy enforcement checks. By automating approvals, SailPoint accelerates access provisioning while ensuring that each request adheres to predefined security controls. This automation strikes a balance between efficiency and security in the access request lifecycle.
55. How does SailPoint handle the periodic recertification of user access?
Ans:
- SailPoint automates the process of access recertification, requiring periodic reviews of user entitlements.
- This ensures that access remains aligned with current business needs and reduces the risk of unauthorized access.
- Periodic recertification is crucial for maintaining a secure access landscape, as it provides a systematic approach to identifying and addressing potential security vulnerabilities.
56. Examine the role of SailPoint’s Integration Modules in connecting with third-party applications.
Ans:
SailPoint’s Integration Modules serve as connectors to third-party applications and systems. These modules streamline the integration process, ensuring that SailPoint can interact seamlessly with a wide range of external platforms. By providing a modular and extensible framework, SailPoint’s Integration Modules enhance the interoperability of the identity management solution.
57. What is the purpose of the IdentityNow Identity Cube?
Ans:
The IdentityNow Identity Cube is a centralized data store within SailPoint that holds identity-related information. It serves as a unified repository for user identity attributes, allowing for efficient and consistent identity management. The Identity Cube consolidates data from various connected systems, providing a comprehensive view of user identities and their attributes across the organization.
58. Explain the concept of “Joiner,” “Mover,” and “Leaver” in SailPoint IdentityNow.
Ans:
Joiner: Represents the onboarding of a new user. During the joiner process, the user is provisioned with the necessary access and roles to perform their job functions.
Mover: Signifies a change in the user’s role or responsibilities within the organization. The mover process involves adjusting the user’s access and roles accordingly to reflect their new position.
Leaver: Involves the offboarding or departure of a user from the organization. During the leaver process, access and roles are de-provisioned to ensure that the departing user no longer has unnecessary privileges.
59. How does SailPoint support RBAC in identity management?
Ans:
Role-Based Access Control (RBAC) is a method of managing access permissions by assigning roles to users based on their job responsibilities. SailPoint supports RBAC by allowing organizations to define roles that represent specific job functions and responsibilities. Users are then assigned these roles, inheriting the associated access rights and permissions.
60. Can you explain the purpose of connectors in SailPoint IdentityNow?
Ans:
Connectors in SailPoint IdentityNow are used to establish and maintain connections between the IdentityNow platform and external systems or applications.
These connectors facilitate the exchange of identity-related data, including user attributes, roles, and entitlements, between SailPoint and connected systems.
61. What is the role of “Rules” in SailPoint IdentityNow?
Ans:
Rules in SailPoint IdentityNow are used to define logic and conditions for various identity management processes. They play a crucial role in automating tasks, such as access approvals, role assignments, and policy enforcement. Rules help customize and extend the functionality of IdentityNow, allowing organizations to tailor the system to their specific requirements.
62. How does SailPoint address the challenge of managing privileged access?
Ans:
SailPoint provides features like role-based access control (RBAC) and access certifications to manage privileged access. RBAC allows organizations to define and control access to sensitive resources, while access certifications ensure regular reviews of privileged access, enhancing security and compliance.
63. What is the purpose of the “IdentityNow Password Management” module?
Ans:
The Password Management module in SailPoint IdentityNow allows organizations to enforce password policies, automate password resets, and provide self-service capabilities for users to manage their passwords.
It enhances security by reducing the risk of weak passwords and ensuring that users have a convenient way to reset and manage their credentials securely.
64. What role does “IdentityNow Reporting” play in SailPoint?
Ans:
- IdentityNow Reporting provides insights into identity-related data, access patterns, and compliance status.
- It helps organizations generate customized reports for auditing, compliance monitoring, and decision-making.
65. Explain the concept of “Entitlement Catalog” in SailPoint.
Ans:
The Entitlement Catalog in SailPoint is a centralized repository that defines and organizes the entitlements available across connected systems. It provides a standardized view of access rights, making it easier to manage and govern entitlements consistently. The Entitlement Catalog plays a key role in simplifying the process of defining roles.
66. What is “Access Certification” in SailPoint?
Ans:
Access Certification in SailPoint involves periodic reviews of user access to ensure that it aligns with business needs and compliance requirements.
It is crucial for maintaining a secure identity environment by providing a systematic process for reviewing and validating access rights.
67. How does SailPoint handle the synchronization of identity data across different systems?
Ans:
SailPoint uses connectors to synchronize identity data across different systems. These connectors establish a connection with each system, allowing for the bi-directional flow of identity information. This synchronization addresses challenges such as data inconsistency, outdated information, and manual errors, ensuring that identity data remains accurate and up-to-date across the entire IT infrastructure.
68. What is the purpose of “Role Mining” in SailPoint?
Ans:
- Role Mining in SailPoint involves the automated discovery of roles based on user access patterns and entitlements.
- It assists in identity governance by helping organizations identify and define roles more efficiently, ensuring that access is aligned with job responsibilities.
69. Explain the concept of “Policy Enforcement” in SailPoint.
Ans:
Policy Enforcement in SailPoint involves defining and enforcing access policies to ensure that user access aligns with organizational requirements and compliance standards. It plays a critical role in maintaining a secure and compliant environment by automatically applying policies related to access controls, segregation of duties, and other security measures.
70. What are the benefits of implementing “Automated Provisioning” in SailPoint IdentityNow?
Ans:
- Efficiency
- Accuracy
- Timeliness
- Compliance
71. Can you explain the concept of “Identity Correlation” in SailPoint?
Ans:
Identity Correlation in SailPoint involves linking and reconciling identities across different systems to create a unified view of a user. It is crucial in identity management as it allows organizations to avoid duplicate or conflicting identity records, ensuring accuracy and consistency in identity data across the enterprise.
72. How does SailPoint support the integration of external data sources?
Ans:
SailPoint provides connectors and integration capabilities to connect with external data sources, allowing organizations to import and synchronize additional identity information. This supports a comprehensive view of user identities, incorporating data from HR systems, directories, and other authoritative sources.
73. What role does “Access Review” play in SailPoint?
Ans:
Access Review in SailPoint involves periodic reviews of user access to validate its appropriateness. It contributes to compliance efforts by providing a systematic process for organizations to regularly assess and certify that user access aligns with business policies and regulatory requirements. This helps demonstrate adherence to compliance standards.
74. What is the purpose of “Policy Violation Alerts” in SailPoint?
Ans:
- Policy Violation Alerts in SailPoint are notifications triggered when a user’s access violates defined policies.
- These alerts play a crucial role in enhancing security and compliance by providing real-time notifications about potential risks or policy breaches.
75. Can you explain the concept of “Entitlement Aggregation” in SailPoint?
Ans:
Entitlement Aggregation in SailPoint involves consolidating entitlements from various applications into roles. This process simplifies access management by grouping similar entitlements across different systems into roles, making it easier to manage and assign access based on job responsibilities.
76. How does SailPoint handle the integration of identity data from external HR systems?
Ans:
- SailPoint integrates with external HR systems through connectors, allowing organizations to import and synchronize employee identity data.
- This integration is vital for ensuring that identity information, such as employee roles and attributes, is up-to-date and accurate.
77. What role does “Continuous Access Certification” play in SailPoint?
Ans:
Continuous Access Certification in SailPoint involves ongoing monitoring and validation of user access in real-time. Unlike periodic certifications, which occur at set intervals, continuous access certification provides a more dynamic and responsive approach to access governance.
78. Can you explain the concept of “IdentityNow Policies”?
Ans:
IdentityNow Policies in SailPoint are rules that define conditions and actions related to identity management processes.
They play a significant role in enforcing access controls, defining approval workflows, and automating various aspects of identity governance.
79. How does SailPoint support the concept of “Dynamic Groups” in role assignments?
Ans:
SailPoint allows the creation of Dynamic Groups, which automatically include users based on specified criteria, such as attributes or entitlements. This dynamic nature ensures that group memberships are automatically adjusted as user attributes change.
80. What is “IdentityNow Governance Platform”?
Ans:
The IdentityNow Governance Platform in SailPoint is a comprehensive solution that combines various modules and features to provide a holistic approach to identity governance.
It includes capabilities such as access certifications, policy enforcement, role management, and analytics. This platform ensures that organizations can govern and secure identities effectively across their entire IT ecosystem.
81. Explain the concept of “Role Lifecycle Management” in SailPoint.
Ans:
- Role Lifecycle Management in SailPoint involves the dynamic adaptation of roles to changing business requirements.
- It ensures that roles evolve alongside organizational changes, such as new job functions or responsibilities.
82. How does IdentityNow Risk Analytics contribute to risk management in identity governance?
Ans:
IdentityNow Risk Analytics in SailPoint involves the analysis of user access patterns and behaviors to identify potential risks. It leverages machine learning and analytics to detect anomalies or deviations from normal behavior, helping organizations proactively address security threats.
83. How does SailPoint handle the challenge of managing identities in a highly regulated industry?
Ans:
- SailPoint addresses regulatory challenges by providing robust access controls, audit trails, and compliance features.
- The platform allows organizations in highly regulated industries to define and enforce access policies that align with industry-specific regulations.
84. How does SailPoint support user self-service capabilities?
Ans:
SailPoint provides a self-service portal that allows users to perform certain identity-related tasks independently, such as password resets or access requests. This feature enhances user satisfaction, reduces IT support overhead, and contributes to overall operational efficiency.
85. What is the purpose of “IdentityNow Dashboards” in SailPoint?
Ans:
IdentityNow Dashboards in SailPoint offer visual insights into identity-related data, access trends, and compliance status. They serve as a centralized hub for monitoring and managing identity governance activities, providing a real-time view of the organization’s identity landscape.
86. Explain the concept of “Entitlement Catalog Management” in SailPoint.
Ans:
- Entitlement Catalog Management in SailPoint involves the organized and structured management of entitlements available in connected systems.
- It plays a critical role in access governance by providing a standardized and unified view of access rights.
- This helps organizations efficiently manage entitlements, create roles, and ensure consistency in access assignments.
87. Can you discuss the significance of “Attribute Mapping” in SailPoint.
Ans:
Attribute Mapping in SailPoint involves defining how identity attributes are mapped between the IdentityNow platform and connected systems. It is crucial for ensuring accurate and consistent identity data synchronization.
88. Can you discuss the role of “IdentityNow Integration Modules” in SailPoint.
Ans:
IdentityNow Integration Modules in SailPoint are pre-built connectors and modules designed to extend the platform’s capabilities. They enhance extensibility by providing out-of-the-box integrations with popular applications, systems, and services, reducing the time and effort required for custom integrations and ensuring broader compatibility.
89. How does SailPoint address the challenge of managing identities in a BYOD environment?
Ans:
- SailPoint addresses BYOD challenges by integrating with mobile device management (MDM) solutions and enforcing policies based on device attributes.
- This ensures that access and entitlements are managed securely, even in scenarios where users bring their own devices into the corporate environment.
90. What role does “IdentityNow Analytics” play in SailPoint?
Ans:
IdentityNow Analytics in SailPoint involves the use of advanced analytics and reporting tools to gain insights into identity-related data. It contributes to the overall effectiveness of identity governance by providing actionable intelligence, identifying trends, and facilitating informed decision-making in areas such as access management, compliance, and risk mitigation.






