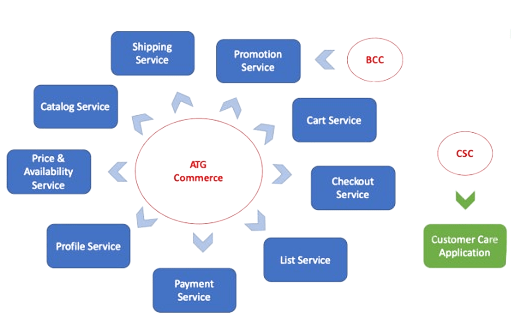
The purpose of developing and overseeing virtual retail spaces, the Art Technology Group (ATG) system is a complete and expandable e-commerce platform. Product catalogue management, content personalization, and order processing are just a few of the many features and tools that Oracle has developed. Businesses can customise their online presence to match specific requirements thanks to ATG’s adaptable and modular architecture. The ATG system gives businesses the ability to offer customised and focused shopping experiences through features like dynamic pricing, promotional campaigns, and customer segmentation. It facilitates easy integration with a range of third-party platforms, payment gateways, and shipping companies, guaranteeing a streamlined e-commerce ecosystem from beginning to end.
1. Describe the ATG Repository.
Ans:
The ATG Repository is a pivotal component within the ATG (Art Technology Group) e-commerce platform, serving as a versatile and extensible data storage system.
2. A description of an item is what?
Ans:
A description of an item is a narrative or set of details providing information about the characteristics, features, and attributes of a specific object, product, or entity.
3. Explain ATG Dynamo.
Ans:
ATG Dynamo, now commonly referred to as Oracle ATG Web Commerce, is an e-commerce platform developed by the Art Technology Group (ATG), which was later acquired by Oracle.
4. What’s the ATG Framework?
Ans:
The ATG (Art Technology Group) Framework, now commonly known as Oracle ATG Web Commerce, is a comprehensive and modular e-commerce framework designed to facilitate the development and management of sophisticated online commerce applications.
5. What is Dynamo Components’ range of use?
Ans:
Dynamo Components, part of the ATG (Art Technology Group) Dynamo framework (now often referred to as Oracle ATG Web Commerce), are versatile building blocks that facilitate the development of dynamic and feature-rich e-commerce applications.
6. What’s in a Nucleus?
Ans:
The Nucleus is a central and core component of the framework responsible for managing the configuration and lifecycle of components in an ATG application.
7. Can you explain the ATG Pipeline?
Ans:
A pipeline is a fundamental concept used to define and carry out a sequence of modular and configurable processing stages in the ATG (Art Technology Group) Dynamo framework, now commonly known as Oracle ATG Web Commerce.
8. What is the ATG Tag Library?
Ans:
Designed for use in web development within ATG applications, the ATG Tag Library is a collection of unique JSP (JavaServer Pages) tags supplied by the ATG platform.
9. When making ATG droplets, which class should you extend?
Ans:
When creating ATG (Art Technology Group) droplets, you typically extend the DropletImpl class or one of its subclasses. The DropletImpl class is part of the ATG Dynamo Server Pages (DSP) framework and serves as a base class for creating custom droplets in ATG applications.
10. Why an Active Directory Back up is important?
Ans:
ATG (Art Technology Group) FormHandler typically extends the DropletFormHandler class or one of its subclasses. The DropletFormHandler is a foundational class in the ATG Dynamo Server Pages (DSP) framework and provides a set of functionalities specifically designed for handling form submissions in ATG applications.
11. What does ATG Formhandlers’ class hierarchy entail?
Ans:
In addition to writing data to and reading data from a database or repository, they also serve the purpose of validating form data before it is submitted and directing the user to different pages based on the submission’s outcome.
12. How is a FormHandler created?
Ans:
Steps to Create an ATG Form Handler:
- Create a Java Class
- Define Properties and Methods
- Define Form Properties
- Configure the FormHandler
- Integrate with JSP
- Configure Success URL
- Handle Form Errors
13. Which two methods are available for use in a component?
Ans:
Two commonly used methods available for use in an ATG component are the doStartService and doStopService methods.
14. What is the difference between a session bean and an entity bean in ATG in a table
Ans:
| Feature | Session Bean | Entity Bean | |
| Purpose |
Used for business logic and transient, client-specific data. |
used in databases to represent persistent data. | |
| State | StateStateful or non-statepossesses a state that can be kept in a database | represents persistent data. | |
| Lifespan | LifespanShort-lived for Stateless (per client request) | long-lasting, usually linked to the life of the database’s underlying data. | |
| Data Storage | Information Storage doesn’t usually keep data in a persistent state. | Represents and works with data that is kept on file in a database. |
15. How does ATG support caching for performance optimization?
Ans:
ATG supports caching at various levels, including page, component, and repository caching, to improve performance by reducing the need to regenerate content
16. What is the purpose of the ATG Content Administration module?
Ans:
The Content Administration module in ATG provides a user interface for managing and updating content in the repository without requiring direct code changes.
17. Explain the role of slots in ATG personalization.
Ans:
Slots in ATG define areas on a page where content can be personalised. Different content can be targeted to different slots based on user behaviour and scenarios.
18. What is the purpose of the ATG Multisite module?
Ans:
The Multisite module in ATG supports the management of multiple sites within a single ATG instance, allowing different configurations, catalogues, and content for each site.
19. What is the role of a droplet in ATG?
Ans:
A droplet is a reusable, self-contained module in ATG used to process and render content. It can perform various tasks such as retrieving data from a repository or invoking a service.
20. What is a repository in ATG, and how is it different from a relational database?
Ans:
A repository is a data storage system in ATG. It is different from a relational database in that it is more flexible, supports complex data structures, and doesn’t strictly enforce a fixed schema.
21. Explain the concept of slots in ATG personalization.
Ans:
Slots in ATG define areas on a page where personalised content can be displayed. Different content can be targeted to different slots based on user behaviour and scenarios.
22. Explain how ATG handles request processing through the pipeline.
Ans:
ATG uses a processing pipeline to handle requests. Each processor in the pipeline performs a specific task, and the request is passed through these processors, allowing for modular and extensible processing.
23. How does ATG support integration with external systems and services?
Ans:
ATG supports integration through services, which are components that encapsulate functionality and can be exposed to other systems. It also supports integration with REST and SOAP web services.
24. What is the ATG B2B Commerce module, and how does it differ from B2C Commerce?
Ans:
The B2B Commerce module in ATG is designed for business-to-business transactions, supporting features like account hierarchies, negotiated pricing, and bulk ordering, which are specific to B2B scenarios.
25. Explain the purpose of the ATG Content Administration module.
Ans:
The ATG Content Administration module provides a web-based interface for non-technical users to manage and update content in the repository, reducing the need for direct code changes.
26. Explain the purpose of the ATG Content Administration module.
Ans:
The ATG Content Administration module provides a web-based interface for non-technical users to manage and update content in the repository, reducing the need for direct code changes.
27. Describe the significance of slots in ATG personalization.
Ans:
Slots define areas on a page where personalised content can be displayed. Personalization engines can target specific content to different slots based on user behaviour and scenarios.
28. What is the role of the ATG FormTagLibrary in the user interface layer of an ATG application?
Ans:
The ATG FormTagLibrary provides custom JSP tags for form handling in ATG. It simplifies the creation and processing of HTML forms in JSP pages.
29. What is the purpose of the ATG Control Center?
Ans:
The ATG Control Center is a web-based tool for managing and monitoring ATG applications. It provides a graphical interface for tasks such as configuration, deployment, and monitoring.
30. How does ATG support internationalisation and localization?
Ans:
ATG provides features for internationalisation and localization through resource bundles, which allow for the translation of text and other content into different languages.
31. What is the purpose of the ATG User Profile Repository?
Ans:
The User Profile Repository in ATG stores user-specific information, including login credentials, preferences, and other relevant data.
32. Explain the purpose of the ATG Merchandising module in an e-commerce application.
Ans:
The Merchandising module in ATG provides features for managing product assortments, promotions, and pricing strategies to optimise the presentation and sale of products.
33. How does ATG support A/B testing for personalised content?
Ans:
ATG supports A/B testing through its Targeting module, allowing developers to create and run experiments to test different versions of content and determine the most effective variant.
34. What is the ATG Service Map, and how is it used in component
Ans:
The Service Map is a key-value store in ATG that allows components to share information. It is often used to store and retrieve references to shared services in a distributed environment.
35. How does ATG handle security in an application?
Ans:
Role-based access control, authorization, and user authentication are all included in the security framework that ATG offers. It supports customised security configurations and integrates with Java EE security features.
36. Explain the role of the ATG Order Fulfilment module in an e-commerce ecosystem.
Ans:
Order fulfilment, including order shipment, inventory control, and order processing, is managed by ATG’s Order Fulfilment module.
37. Identify two different table types.
Ans:
The two distinct categories of tables intended for particular uses are:
Relational Tables: In a relational database management system (RDBMS), relational tables are the most prevalent kind of tables.
NoSQL Tables (Document Store): Many table types that correspond to their data models are commonly used by non-relational databases, or NoSQL databases.
38. Explain the role of the ATG FormHandler class in handling form submissions.
Ans:
The FormHandler class in ATG handles form submissions by processing form data, performing validation, and updating the repository or taking other actions based on the form’s content.
39. What is the purpose of the ATG Targeting module, and how is it used in personalization?
Ans:
The ATG Targeting module provides features for personalization by allowing the targeting of content and promotions to specific user segments based on their behaviour, preferences, or other criteria.
40. What is the purpose of the ATG CartModifierFormHandler in an e-commerce application?
Ans:
The CartModifierFormHandler is used to modify the contents of a shopping cart. It handles actions such as adding items to the cart, updating quantities, and removing items.
41. How does ATG support the creation and management of user accounts in an e-commerce scenario?
Ans:
ATG provides a User Profile Repository to store and manage user account information. It includes features for user registration, login, and account maintenance.
42. What is the purpose of the ATG PipelineManager, and how is it used in request processing?
Ans:
The PipelineManager is responsible for managing and executing processing pipelines in ATG. It plays a key role in request processing, allowing the configuration of modular and reusable processing units.
43. Explain the use of slots and scenarios in ATG’s Targeting module for content personalization.
Ans:
Slots define areas on a page where personalised content can be displayed. Scenarios define conditions triggering the display of specific content in those slots based on user behaviour.
44. How does ATG support the implementation of product recommendations in an e-commerce setting?
Ans:
ATG provides a Merchandising module that supports the definition of promotions and recommendations. The module allows for the display of personalised product recommendations based on user behaviour.
45. What is the purpose of the ATG Pricing Engine, and how does it contribute to dynamic pricing strategies?
Ans:
The Pricing Engine in ATG is responsible for calculating prices dynamically based on various factors such as promotions, discounts, and user-specific pricing rules.
46. Explain the concept of promotion chaining in ATG’s Commerce module.
Ans:
Promotion chaining allows multiple promotions to be applied to an order simultaneously. ATG supports the definition of promotion chains to create complex and flexible pricing strategies.
47. How does ATG handle user authentication and authorization in a web application?e?
Ans:
ATG integrates with Java EE security features for user authentication and authorization. It supports role-based access control to manage user permissions.
48. What is the purpose of the ATG Service Framework, and how does it facilitate component interaction?
Ans:
The ATG Service Framework provides a mechanism for components to discover and interact with each other. It allows services to be shared across components in a flexible and decoupled manner.
49. Explain the role of the ATG Transaction Management system in handling transactions in an application.
Ans:
Support for managing transactions and guaranteeing the atomicity and consistency of system operations is provided by the ATG Transaction Management system.
50. How does ATG support the creation and management of user accounts in an e-commerce scenario?
Ans:
ATG provides a User Profile Repository to store and manage user account information. It includes features for user registration, login, and account maintenance.
51. What is the purpose of the ATG PipelineManager, and how is it used in request processing?
Ans:
Managing and carrying out ATG processing pipelines is the responsibility of the PipelineManager. By enabling the configuration of modular and reusable processing units, it plays a crucial part in request processing.
52. What is the purpose of the ATG Profile Adapter, and how does it enhance personalization?
Ans:
The Profile Adapter in ATG allows integration with external user profile systems. It enhances personalization by enabling ATG to leverage user profile data stored in external systems.
53. Explain how ATG supports caching at the component level.
Ans:
ATG supports component-level caching through the use of the CacheControl service. Developers can configure caching settings for individual components to improve performance.
54. How does ATG handle form validation, and what is the role of the ValidationDroplet?
Ans:
The ValidationDroplet is used for form validation in ATG. It provides methods for performing server-side validation and generating error messages based on the form input.
55. What is the purpose of the ATG OrderModifier pipeline, and how is it used?
Ans:
The OrderModifier pipeline in ATG allows developers to insert custom logic for modifying orders during the order fulfilment process. It enables actions like applying discounts or adding gift items.
56. How does ATG support dynamic pricing in e-commerce applications?
Ans:
ATG Commerce provides features for dynamic pricing, allowing for the implementation of pricing rules, promotions, and discounts based on various criteria such as user segments, purchase history, and more.
57. Explain the role of slots and components in the ATG User Interface layer.
Ans:
Slots define areas on a page where content can be personalised. Components are reusable modules responsible for rendering content within slots based on user behaviour and scenarios.
58. What is the ATG Servlet pipeline, and how does it handle HTTP requests?
Ans:
The ATG Servlet pipeline is a sequence of processors that handle HTTP requests. Each processor performs a specific task, allowing for extensible and modular request processing.
59. How does ATG support SEO (Search Engine Optimization) for e-commerce sites?
Ans:
ATG provides features for SEO, such as customizable URLs, sitemap generation, and metadata management. This helps improve the visibility of e-commerce sites in search engines results.
60. Explain the role of the ATG Content Scenarios module in personalization.
Ans:
The Content Scenarios module allows for the definition of scenarios that trigger the display of personalised content. It enables content targeting based on user behaviour, preferences, or other criteria.
61. What is the purpose of the ATG RepositoryFormHandler?
Ans:
The RepositoryFormHandler in ATG extends the functionality of the FormHandler to provide integration with the ATG repository. It facilitates the handling of form submissions involving repository operations.
62. Explain ATG Data Export and Import.
Ans:
ATG, data export and import processes are integral for transferring information between instances or environments. The Flexible File Export and Import feature allows developers to define custom export and import services, enabling the selective extraction and loading of data.
63. Define ATG Form handler extensibility.
Ans:
ATG FormHandlers provides developers with a powerful mechanism to customise form processing logic. By creating subclasses of existing FormHandlers, developers can add additional validation, manipulate form data before submission, or integrate with external services.
64. What is ATG Deployment Strategies?
Ans:
ATG, deployment strategies play a crucial role in ensuring smooth transitions from development to production. Developers can create deployment plans, manage configuration files, and deploy changes across environments seamlessly.
65. Describe ATG Repository Caching
Ans:
Caching is a fundamental aspect of performance optimization in ATG, particularly at the repository level. By implementing effective caching strategies, developers can significantly reduce database queries, resulting in improved application responsiveness and reduced server load.
66. What is mean by ATG B2B Commerce Module?
Ans:
The ATG B2B Commerce module caters specifically to business-to-business transactions, introducing features tailored to meet the unique requirements of B2B scenarios.
67. Define ATG Cross-Site Scripting (XSS) Protection.
Ans:
Protecting against Cross-Site Scripting (XSS) is paramount in web application security, and ATG provides mechanisms to mitigate such risks. Developers can leverage the HTML Content Security Policy (CSP) feature to define and enforce rules for allowable content sources, preventing malicious scripts from executing.
68. What is mean by ATG Asynchronous Event Handling?
Ans:
Asynchronous event handling in ATG enables developers to decouple and streamline background processing tasks. By leveraging the ATG Event System, events triggered during user interactions or system operations can be processed asynchronously.
69. Explain ATG Custom Droplets.
Ans:
Custom droplets in ATG provide a means to extend and enhance the functionality of JSP pages. Developers can create droplets to encapsulate reusable logic, whether for retrieving data from the repository, invoking services, or performing complex calculations.
70. Explain ATG Service Layer.
Ans:
The ATG service layer is pivotal for achieving modularity and encapsulation in application design. Services in ATG encapsulate business logic and can be easily accessed by other components. This layer facilitates loose coupling between components, allowing for easier maintenance and extensibility.
71. Define ATG Email marketing module.
Ans:
The ATG Email Marketing module empowers businesses to execute targeted email campaigns seamlessly. It facilitates the creation, management, and execution of email marketing strategies, including personalised content delivery and automated scheduling.
72. What is ATG RESTful Web Services?
Ans:
ATG’s support for RESTful web services enables seamless integration with modern web architectures. Developers can expose ATG functionalities as RESTful endpoints, allowing external applications to interact with ATG resources.
73. Explain ATG Navigation and Search.
Ans:
Navigation and search functionalities are critical components of an effective e-commerce platform. ATG provides a robust navigation and search framework that allows users to easily explore product catalogues.
74. Define ATG Form Success URL Configuration.
Ans:
Configuring the success URL after form submissions is a common requirement in ATG applications. Developers can customise the behaviour of form handlers by specifying the success URL dynamically or statically.
75. What is ATG Multisite Content Sharing?
Ans:
The Multisite module in ATG not only enables the management of multiple sites but also facilitates content sharing across these sites.
76. Explain ATG Integration with Payment Gateways.
Ans:
ATG seamlessly integrates with various payment gateways, enabling secure and efficient transaction processing in e-commerce applications.
77. Define ATG Personalization with Scenarios.
Ans:
Personalization in ATG is driven by scenarios, which define the conditions under which specific content is displayed. Scenarios can be tailored based on user behaviour, preferences, or demographics.
78. What are ATG Scenario Development Best Practices?
Ans:
Crafting effective scenarios in ATG requires adherence to best practices. Developers should consider factors such as scenario simplicity, clear targeting criteria, and scalability.
79. Define ATG Order Fulfilment and Inventory Management.
Ans:
The ATG Order Fulfilment module plays a crucial role in managing the entire lifecycle of customer orders. From order processing to inventory management and shipment tracking, this module streamlines the fulfilment process.
80. Explain ATG Integration with Content Delivery Networks (CDN).
Ans:
ATG integration with Content Delivery Networks (CDN) is a method for improving performance. In order to lower latency and speed up page loads, content delivery networks (CDNs) disperse content among a network of servers that are situated closer to end users.
81. What is ATG Multisite Content Sharing?
Ans:
The Multisite module in ATG not only enables the management of multiple sites but also facilitates content sharing across these sites. This feature allows businesses to efficiently reuse and distribute content assets across different digital properties.
82. Define ATG Integration with Payment Gateways.
Ans:
ATG seamlessly integrates with various payment gateways, enabling secure and efficient transaction processing in e-commerce applications.This integration is crucial for creating a reliable and trustworthy online shopping experience.
83. Explain ATG Personalization with Scenarios.
Ans:
Personalization in ATG is driven by scenarios, which define the conditions under which specific content is displayed. Scenarios can be tailored based on user behaviour, preferences, or demographics.
84. Describe ATG Order Fulfilment and Inventory Management.
Ans:
The ATG Order Fulfilment module plays a crucial role in managing the entire lifecycle of customer orders. From order processing to inventory management and shipment tracking, this module streamlines the fulfilment process.
85. Explain the Dynamic Pricing Strategies.
Ans:
Dynamic pricing strategies based on different factors like discounts, promotions, and user-specific pricing rules are made possible by ATG’s Pricing Engine.
86. Define ATG Form Validation with Validation Droplet.
Ans:
The ValidationDroplet in ATG simplifies form validation by providing a centralised mechanism for server-side validation. Developers can configure the ValidationDroplet to validate form input based on predefined rules, generating error messages for invalid dataCross-Site Scripting (XSS) Protection Strategies
87. What are ATG deployment’s Best Practice?
Ans:
Deploying ATG applications requires adherence to best practices to ensure a smooth and reliable release process. Developers can utilise tools such as Ant scripts or the ATG Control Center for automated deployment tasks.
88. Define Integration with Customer Relationship Management (CRM) Systems.
Ans:
Integrating ATG with CRM systems enhances customer relationship management by consolidating customer data and interactions.
89. Explain Cross-Site Scripting (XSS) Protection Strategies.
Ans:
Protecting ATG applications from Cross-Site Scripting (XSS) attacks is paramount for security. Developers can implement strategies such as input validation, output encoding, and utilising ATG’s built-in security features.
90. What Web Services Security Considerations?
Ans:
Security considerations are paramount when exposing ATG functionalities as web services. Developers must implement robust authentication and authorization mechanisms, leveraging industry-standard security protocols such as OAuth or API keys.






