
- What is Ethical Hacking?
- How to become an ethical hacker
- Main Objectives Involved in Ethical Hacking
- What Resources Do Ethical Hackers Use?
- Benefits of Ethical Hacking
- Ethical Hacking jobs
- Conclusion
The demand for Ethical Hacking Course personnel has reached an all-time high as digital dangers have become more widespread. Ethical Hacking, often known as penetration testing, has emerged as the most fascinating and lucrative employment option in technology. Organizations currently want individuals who can think like hackers but prefer to defend rather than exploit. How to become an ethical hacker is the most critical initial step toward advancement in this in-demand sector.
Are you curious to know more about Ethical hacker? Take advantage of our comprehensive online Ethical Hacking Training!
What is Ethical Hacking?
Ethical Hacking is the intentional probing of systems, networks, or applications to find flaws before black-hat hackers can exploit them. Cybercriminals violate this rule because they hack without the authorization of the system owners and want to impair the system’s security.
An ethical hacker’s work often comprises the following tasks.
- Penetration testing simulates cyberattacks to assess the effectiveness of security defences.
- Vulnerability assessment is the process of evaluating a system or network for security weaknesses and offering fixes.
- Security auditing assesses the system’s security policies and practices in light of industry standards.
Cybersecurity can only be achieved with ethical hackers who protect data, prevent breaches, and defend systems from developing Cyber Awareness.
How to become an ethical hacker
In the Internet age, all large companies and multinational corporations require a strong security staff. An ethical hacker can aid large corporations by working as a cyber-security expert. Since 2012, Ethical Hacking has grown at a rate that far outpaces all other areas of cybersecurity and the IT industry. According to the Bureau of Labor Statistics, listings for cybersecurity positions have surged by an amazing 75% since 2012. The pay scale for ethical hackers is also impressive. Reasons to pursue a career in ethical Hacking include increased demand for information security professionals in public and private sectors, leading to additional job prospects.
- Ethical Hacking has now crossed the digital world and is invading the real world with real-world consequences.
- Jobs are plentiful; enrolling in an Ethical Hacking course could result in a 50-70% pay increase.
- There are opportunities to collaborate with major brands such as Visa, Cisco, Oracle, Reliance, GE, and American Express, to name a few.
- This provides an excellent opportunity to network with new people and industry experts.

Cybersecurity is regarded as more future-proof in terms of the model, as any firm must take security seriously due to its increasingly interconnected nature. As the number and complexity of cyber threats increase, there will be a greater demand for ethical hackers.More importantly, ethical Hacking provides greater opportunities for job progression. As you gain more knowledge and expertise, you may be promoted to higher ranks or even start your Cyber Media firm. Your career will continue to advance as new technology and threats emerge.
Enroll in ACTE’S Ethical Hacking Training if you want to become an expert in Ethical Hacking field and have a prosperous career.
Main Objectives Involved in Ethical Hacking
The main objectives of ethical Hacking are searching for vulnerabilities, improving security systems, and ensuring digital infrastructures maintain their integrity. How to become an ethical hacker, also known as a white-hat hacker, performs authorized penetration testing to reveal weaknesses in networks, applications, or systems that malicious hackers, known as black hats, would capitalize on. The point would be to detect and rectify any possible security loopholes well in advance instead of allowing a malicious person to misuse them. This then reduces the possibility of data breaches and cyber-attacks. The primary goal is penetration testing, whereby ethical hackers create real-world attacks to test how well the defence of a system can resist attacks. Often, weaknesses in the routine review of security should be noticed. In addition to penetration testing, they also conduct a vulnerability assessment. This scans for and evaluates known security flaws in software and hardware configurations. They give recommendations on how to mitigate the risks.
Technical tasks aside, ethical hackers adopt strict protocols to build better security policies and best practices for organizations ‘ users and IT staff. Generally speaking, ethical Hacking aims to produce stronger, more secure systems by first attempting to break the system and then neutralizing all potential threats to strengthen an organization’s Ethical Hacking Course posture and minimize its chances of suffering a successful cyberattack.
What Resources Do Ethical Hackers Use?
Here are some of the most popularly used ethical hacking tools:
- Nmap: A network investigation and security scanner. It is used to discover network hosts and services and to look for security flaws.
- Wireshark: Wireshark is a popular network analyzer for software development. It is also used in network analysis and other related disciplines.
- Metasploit: It is used to test system security and find out related vulnerabilities.
- Burp Suite: This is used to identify all types of weaknesses related to Web Application Security.
Want to Take the Lead in Cyber Security ? Enroll in ACTE’s Cyber Security Expert Masters Program Training Course Program to Begin Your Adventure Now.
Benefits of Ethical Hacking
- Identifying vulnerabilities from a Hacker’s perspective
Ethical Hackers take a different approach, adopting the mindset of malicious hackers, but they do it honestly, correctly, and with legal elements so that it is done correctly and proper security loopholes may be achieved that might be overlooked in traditional security audits.This leads to specific insights from Ethical Hackers as they understand how attackers could potentially exploit these vulnerabilities.
- Preventing data breaches and other security incidents
Ethical Hacking is a preventive measure that deals with vulnerabilities again, saving, saving companies from serious security breaches that may lead to huge financial losses and even harm their reputation.Ethical Hacking safeguards the organization’s data and fosters customer and partner confidence by recognizing and fixing security risks before they are exploited.
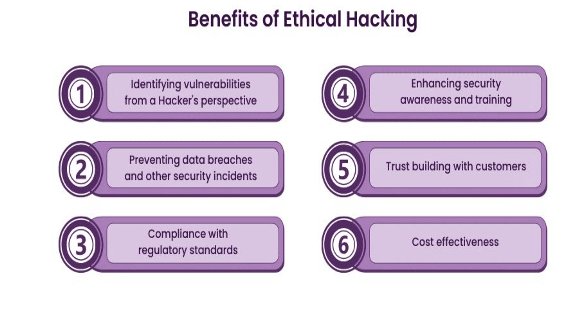
- Compliance with regulatory standards
Strict compliance standards manage many industries. Thus, so they have to conduct routine security checks like penetration testing. Ethical Hacking helps these actions by ensuring the organizations fulfil these requisites; therefore, they will not be punished with the grave legal sanctions of not complying
- Enhancing security awareness and training
Except for testing security measures, Ethical Hacking also plays a very important role in an organization’s educational initiatives. This simply raises workers’ awareness of new threat vectors, thereby enhancing the importance of security best practices.The training prepares employees to recognize and respond to Web Security in ways that improve the organization’s security culture. In addition, it promotes continual learning and adaptability, which is critical in today’s rapidly changing cyber threat scenario.
- Trust building with customers
Regular Ethical Hacking signals customers that an organization is serious about protecting its data. This commitment to security can be very significant for generating much-needed trust and confidence in the brand.A good security reputation is a very strong business asset. It reinforces loyalty from existing customers and may also help attract new customers.
Ethical Hacking jobs
There are numerous Ethical Hacker job opportunities for entry-level and experienced professionals today as most companies are looking for those who can improve their security systems and prevent them from any external threats and breaches. Due to this, the demand for Ethical Hackers has grown immensely in recent years and will continue to do so.
Various job profiles for Ethical Hacking professionals are mentioned below:
- Ethical Hacking Manager
- Junior Cyber Awareness Analyst
- Cybersecurity Analyst
- IT Security Analyst
- IT Security Operations Technical Analyst
- Software Security Engineer
- Network Security Specialist
- Information Security Analyst
Preparing for a Ethical Hacking Job Interview? Check Out Our Blog on Ethical Hacking Interview Question & Answer
Conclusion
The journey of advancement in a career in ethical Hacking is exciting and requires a combination of foundational knowledge, practical experience, certification, and ongoing learning. How to become an ethical hacker involves staying updated on the latest trends and techniques, which opens up numerous job opportunities and offers lucrative salary packages. This career path allows individuals to make significant contributions to the rapidly growing field of Ethical Hacking Course. Whether you’re a fresh starter or someone looking to build on previously gained IT skills, a career as an ethical hacker is both achievable and highly rewarding. The demand for ethical hackers will only continue to rise as digital security remains fluid, with these roles being critical and well-compensated. If you’ve ever wanted to join the world of cybersecurity, now is the best time to dive into become an ethical hacker and advance your career in this dynamic and ever-evolving field.





