- Introduction to Steganography
- History and Evolution
- How Steganography Works
- Types of Steganography (Text, Image, Audio, Video, Network)
- Steganography vs Cryptography
- Common Steganographic Techniques
- Tools and Software Used
- Real-World Use Cases
Introduction to Steganography
Steganography is the art and science of hiding information in plain sight, allowing secret messages to be embedded within seemingly harmless media like images, audio, or video files. Unlike encryption, which makes data unreadable, steganography conceals the very existence of the data itself, making it a powerful tool for secure communication. A common application is digital watermarking and steganography, where hidden data is used to protect intellectual property or verify authenticity. One of the most popular forms is image steganography, where techniques such as Least Significant Bit (LSB) manipulation or color channel modification are used to embed text or files within images. This method is widely covered in Cyber Security Training programs, as it teaches professionals how to both implement and detect hidden data within digital media, enhancing their ability to protect sensitive information and identify potential threats. Developers often explore image steganography Python libraries like OpenCV and Stegano to experiment with these techniques in real-world applications. Another category includes masking and filtering steganography, which subtly alters visual elements of the cover media, making detection even more difficult. While steganography has legitimate uses in cybersecurity, digital forensics, and privacy, it also poses ethical concerns if misused. As digital communication continues to evolve, understanding the principles and tools behind steganography becomes crucial not only for data protection but also for developing countermeasures in digital security.
Interested in Obtaining Your Cybercrime Certificate? View The Cyber Security Online Training Offered By ACTE Right Now!
History and Evolution of Steganography
- Ancient Beginnings: Steganography was first used in ancient Greece where messages were hidden beneath wax on tablets or tattooed on a messenger’s shaved head, later covered with regrown hair.
- Renaissance Ciphers: During the Middle Ages and Renaissance, invisible ink and coded messages became popular for espionage, especially in diplomatic and military contexts. Today, similar principles of secrecy and detection are applied in digital security practices, including modern Introduction to Bug Bounty Programs, where ethical hackers search for vulnerabilities in systems sometimes involving hidden or obfuscated code mirroring the covert tactics of historical intelligence gathering.
- World War Stealth: In both World Wars, steganography evolved into more technical methods, including microdots and text masking to hide intelligence within innocent-looking communications.
Steganography has a rich and fascinating history that dates back thousands of years. From ancient secret messages hidden in wax tablets to modern digital techniques used in cyber security hacking and software coding, the evolution of steganography reflects humanity’s ongoing quest to communicate discreetly. Over time, it has advanced from physical to digital mediums, now playing a key role in the tech-driven world of steganography cyber solutions.
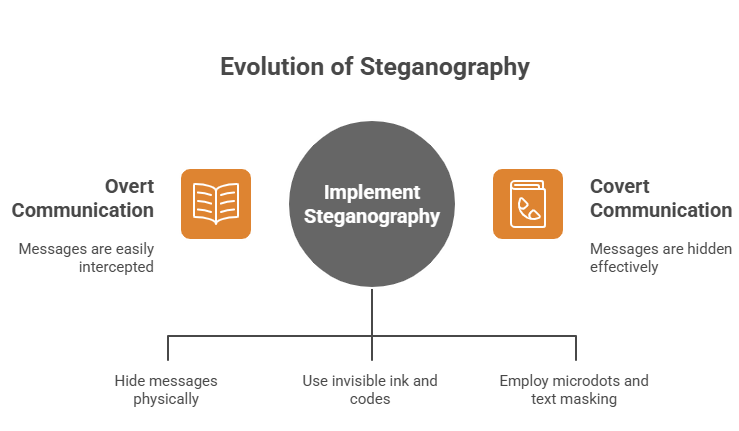
- Digital Revolution: With the rise of computers, software coding allowed data to be embedded within digital files like images, paving the way for image steganography.
- Rise of Stegano Tools: Tools like Stegano, a Python-based library, made it easier for developers and researchers to experiment with steganographic techniques.
- Modern Cyber Applications: Today, cyber security hacking groups and ethical hackers alike use steganography cyber methods for hidden data transmission, making it vital in cybersecurity defenses.
- Text Steganography: This involves hiding information within the text itself through intentional spelling errors, invisible characters, or formatting manipulation. It’s the oldest form and often used in low-bandwidth communication.
- Image Steganography: Perhaps the most widely used, this method hides data within digital images by altering pixel values in ways that the human eye can’t detect. With image steganography and Python libraries like Stegano, it’s easy to embed and extract hidden messages. These techniques are often taught in Cyber Security Training programs, helping learners understand how steganography can be used both defensively and offensively in digital communication and threat detection.
- Audio Steganography: This type involves embedding data into audio files by modifying sound waves, echo, or phase shifting, used widely for covert communication.
- Video Steganography: By hiding data in video frames or motion vectors, this method combines image and audio steganography, increasing the payload capacity and secrecy.
- Network Steganography: This technique hides data within network protocols or traffic patterns, commonly used in steganography cyber activities to bypass firewalls or avoid detection.
- Software-Based Steganography: Here, hidden information is embedded within software coding or executable files. Hackers may use this to inject malicious scripts into otherwise safe-looking applications, making it a concern in cyber security hacking.
- Least Significant Bit (LSB) Insertion: This method replaces the least significant bits in image or audio files with hidden data. It’s simple and widely used in image steganography Python projects.
- Masking and Filtering Steganography: This technique hides data by adjusting brightness, contrast, or transparency, commonly used in masking and filtering steganography for images and audio.
- Transform Domain Techniques: Data is embedded in the frequency domain using mathematical transformations like DCT or DWT, often applied in JPEG image or audio files for more resilience. These advanced techniques are commonly supported by modern Cyber Security Tools, which enable professionals to analyze, detect, and sometimes utilize such methods for secure communication or forensic investigations in complex digital environments.
- Spread Spectrum: This method spreads hidden data across a wide bandwidth, making it difficult to detect or remove without degrading the original file.
- Digital Watermarking: A form of digital watermarking and steganography used to embed ownership or copyright information into multimedia content to prevent unauthorized use.
- Palette-Based Techniques: These modify the color palette of indexed images (like GIFs) to embed hidden data while maintaining visual integrity.
How Steganography Works
Steganography works by embedding hidden information within a carrier file such as an image, audio, or video in such a way that the alteration is almost undetectable to the human eye or ear. This technique is different from encryption, which merely scrambles data; steganography conceals the fact that a message even exists. One of the most commonly used methods is image steganography, where pixels in an image are subtly adjusted to encode information. With tools like image steganography Python libraries, such as Stegano or OpenCV, developers can embed text, files, or even scripts into images without significantly changing their appearance. These techniques are increasingly relevant in discussions around secure communication and data protection, making them a valuable part of any Guide To Data Privacy, where understanding how hidden data can be stored and transmitted is essential for safeguarding sensitive information. Another method, masking and filtering steganography, alters specific components of an image like brightness or contrast to hide data more securely, often used in conjunction with image formats that support transparency. Additionally, digital watermarking and steganography often work hand in hand to protect digital content, embedding copyright or ownership information directly into the media to prevent unauthorized use. These techniques ensure the message remains hidden until a decoding key or software reveals it, making steganography a vital tool in cybersecurity, forensics, and covert communication across digital platforms.
To Explore Cybersecurity in Depth, Check Out Our Comprehensive Cyber Security Online Training To Gain Insights From Our Experts!
Types of Steganography (Text, Image, Audio, Video, Network)
Steganography comes in various forms, each designed to hide information in different types of media while remaining undetectable. As cyber threats grow more complex, understanding the different types of steganography becomes crucial for both defense and offense in cyber security hacking. With advancements in software coding and accessible tools like Stegano, the process of hiding data has become easier and more sophisticated. Below are the key types:
Steganography vs Cryptography
Steganography and cryptography are both essential techniques in information security, but they serve different purposes. While cryptography focuses on scrambling data into unreadable formats to protect it from unauthorized access, steganography hides the very existence of the data within other seemingly harmless media. In modern cyber security hacking, attackers may use cryptography to encrypt stolen data and steganography to hide their activity altogether. For example, image steganography allows users to conceal messages or files within digital images by subtly altering pixel values, making detection nearly impossible without specialized tools. Tools like Stegano, a Python-based library, simplify this process for developers and security enthusiasts exploring steganographic methods. On the other hand, cryptography uses complex mathematical algorithms to encode information, which is still visible but unreadable without the correct decryption key. Both steganography and cryptography are vital components in the Overview of Cybersecurity Threats, as they can be used for both protecting sensitive data and, in the wrong hands, executing covert attacks that evade traditional security measures. Steganography is more discreet, making it a popular choice in steganography cyber operations where undetectability is crucial. Moreover, modern software coding allows both techniques to be combined for added security by encrypting data first and then embedding it using steganography. While cryptography guards the content, steganography guards the context, and together, they offer a layered defense strategy in today’s advanced cyber threat landscape.
Looking to Master Cybersecurity? Discover the Cyber Security Expert Masters Program Training Course Available at ACTE Now!
Common Steganographic Techniques
Steganography employs various techniques to discreetly embed hidden data within digital files, making detection extremely challenging. These methods vary in complexity and effectiveness depending on the media type and use case. From altering individual pixels to modifying file structures, the goal remains the same conceal information without raising suspicion. With growing interest in tools like image steganography Python libraries and enhanced digital watermarking and steganography methods, it’s essential to understand the most widely used techniques in the field.
Tools and Software Used
A wide range of tools and software have made steganography more accessible and practical for both professionals and enthusiasts. These tools are essential in fields like image steganography, cyber security hacking, and digital forensics, enabling users to embed and extract hidden information from various types of media. One of the most popular options is Stegano, a Python-based library that allows developers to perform image-based steganography using custom software coding techniques. It’s especially favored by those working on automated or script-based solutions in cybersecurity. Another widely used tool is OpenStego, which supports digital watermarking and basic steganographic functions, making it useful for educational and copyright protection purposes. In more advanced applications, tools like these may be paired with the Data Encryption Standard Algorithm to first encrypt the data before embedding it, adding an extra layer of security to the steganographic process and ensuring the confidentiality and integrity of hidden information. QuickStego and SilentEye provide more user-friendly interfaces, ideal for those who want to hide messages in images or audio files without complex coding. Tools like Steghide offer robust command-line features, support BMP and WAV formats, and are often utilized in steganography cyber training or ethical hacking exercises. Xiao Steganography is another simple yet effective application for embedding data into BMP and WAV files. These tools play a vital role in modern digital security, allowing both offensive and defensive players to explore the hidden layers of data communication and protect sensitive information discreetly.
Preparing for Cyber Security Job Interviews? Have a Look at Our Blog on Cyber Security Interview Questions and Answers To Ace Your Interview!
Real-World Use Cases
Steganography plays a crucial role in various real-world scenarios where the ability to hide information discreetly is essential. One of the most common applications is in copyright protection, where digital watermarking and steganography are used to embed ownership details into digital images, videos, or documents without altering their visible quality. In the realm of cybersecurity, steganography is employed for covert communication, especially in espionage and intelligence gathering, where sensitive messages are embedded in innocent-looking files. Tools like image steganography Python libraries are widely used by developers and researchers to embed encrypted text or data into images, making detection nearly impossible without the right decryption tool. Journalists and whistleblowers also use steganography to bypass censorship by hiding reports or documents within media files when operating in restrictive environments. Meanwhile, malicious actors may use techniques like masking and filtering steganography to embed malware or commands within multimedia content, making it hard for traditional security systems to detect such threats. These scenarios are commonly explored in Cyber Security Training, where professionals learn how to identify steganographic techniques, analyze hidden data, and strengthen defense mechanisms against covert cyber threats. In corporate settings, steganography helps in securing confidential documents, transmitting hidden instructions, or embedding secure tags for digital tracking. Whether used for protection or exploitation, steganography continues to impact fields like media, cybersecurity, defense, and digital communication in powerful, often invisible ways.
 LMS
LMS




